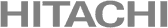
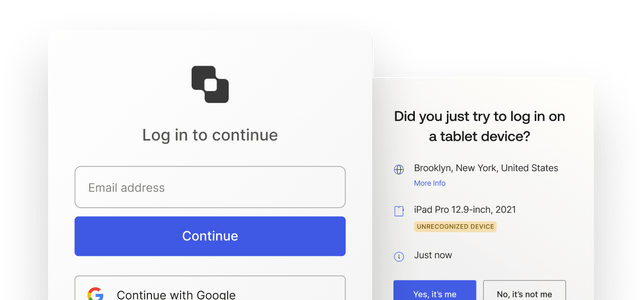
Go further with secure Identity that streamlines user experiences, increases customer sign-ups, improves workforce productivity, and gets apps to market faster.
Looking to log in?
Go here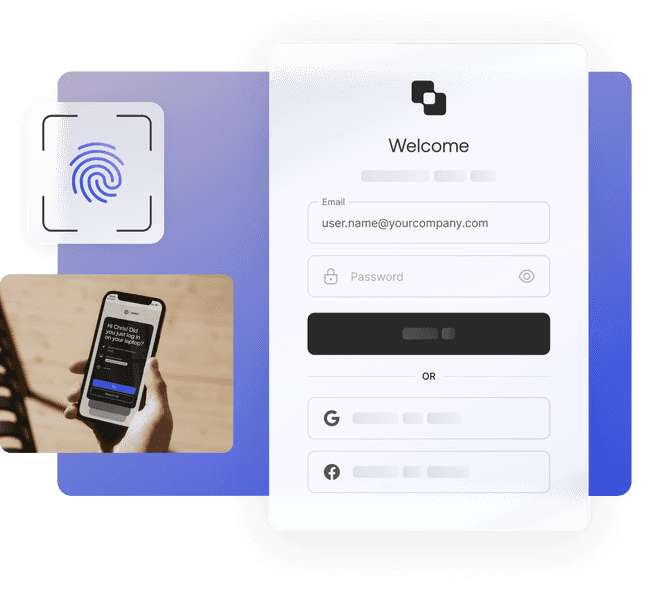
The most trusted brands trust Okta to accelerate business

Wyndham Hotels & Resorts is increasing customer loyalty and expanding rewards for 100 million members.
100M
85%
Key Products
Key Products
Okta helps Navan increase adoption, bookings, and revenue with better UX and smarter personalization.
50%
One
Key Products
Key Products

With the Okta-powered TakedaID platform, Takeda delivers increased security that enables greater scalability.
3.6M
500
Key Products
Key Products

Okta helps Zoom rapidly scale with simplified, secure identity and privileged management across its business.
30x
2
Key Products
Key Products

By streamlining disparate SaaS, cloud-native, and legacy on-prem apps into one unified cloud, FedEx has improved their security posture.
250+
5
Key Products
Key Products
Virgin Media O2 automates complex lifecycle management processes to improve efficiency and productivity, saving time and money.
32
1
Key Products
Key Products
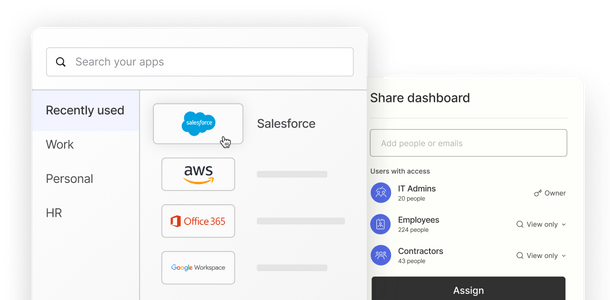
Leverage the most comprehensive and powerful Identity solution out there
We’ve got your back, no matter your stack
- Neutral
- Comprehensive
- Fast

































Easily extensible with 7000+ prebuilt integrations that free you to safely use any technology you choose.