Demo: User Authentication
Transcript
Details
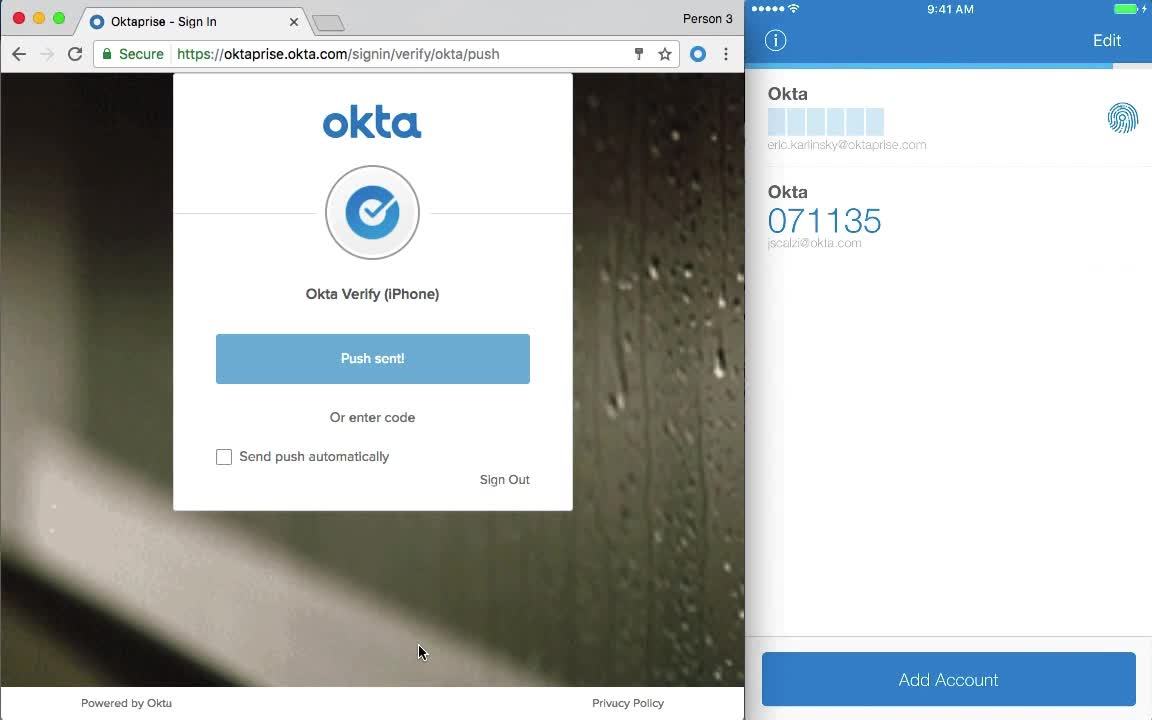
Speaker 1: What I'm going to show here is how to do multi-factor authentication using our push mode authentication, also known as Okta Verify. On the right, you have my phone. On the left, you have the login screen. I've enabled a policy that prompts me for MFA every time I log into the Okta Access Management Platform. Click Sign-in here for my primary auth. I click send, push. I could also automate this by clicking send, push automatically. I tap on the notification, tap approve. It prompts me for touch ID, because I've configured the extra security setting, scan my finger, and then I get access to the access management platform in all my apps that are connected.
Speaker 1: Now I'm going to demo a biometric authentication method that Okta natively supports. In this case, it's Windows, Hello. We also support touch ID on iPhones. Windows Hello is built into windows 10, so we expect it to be a pretty popular way to authenticate to applications, especially since you don't have to use a password. So to use it in Okta, it's natively integrated to the platform. Whenever I click on a protected application, like in this case Amazon Web Services, I'm prompted for a second-factor authentication. I still have access to my other methods, like Okta Verify and SMS, but I'm going to use Windows Hello here. So I click it, it recognised me based on my using the facial recognition camera. I click okay, and then I get access to my application. Seamless, integrated and native to the operating system. And to Okta.
Learn how MFA works with Okta’s login. We’ll show you how Okta Verify works on a mobile device, and how to use Okta’s natively supported biometric authentication on any device.