Magic links are a form of passwordless login. Instead of the user entering any login credentials to sign in, they are sent a URL with an embedded token via email, and sometimes via SMS. Once the user clicks that link to authenticate, they are redirected back to the application or system having successfully signed in—as if they used a “magic” password, but without the actual password.
As many organizations move beyond password-based authentication, magic logins are emerging as a popular consumer authentication method, depending on a company’s risk appetite. Whether your users need a Slack magic link, a Tumblr magic link, or a way to easily access your own apps and services, magic login frees them from remembering a long list of passwords.
In this post, we’ll explore how magic links work in depth, discussing various situations where organizations can use them to create secure and user-friendly experiences. We’ll consider how implementing magic link authentication benefits end users and your developers—and where they may fall short.
How do magic links work?
Magic login involves three steps:
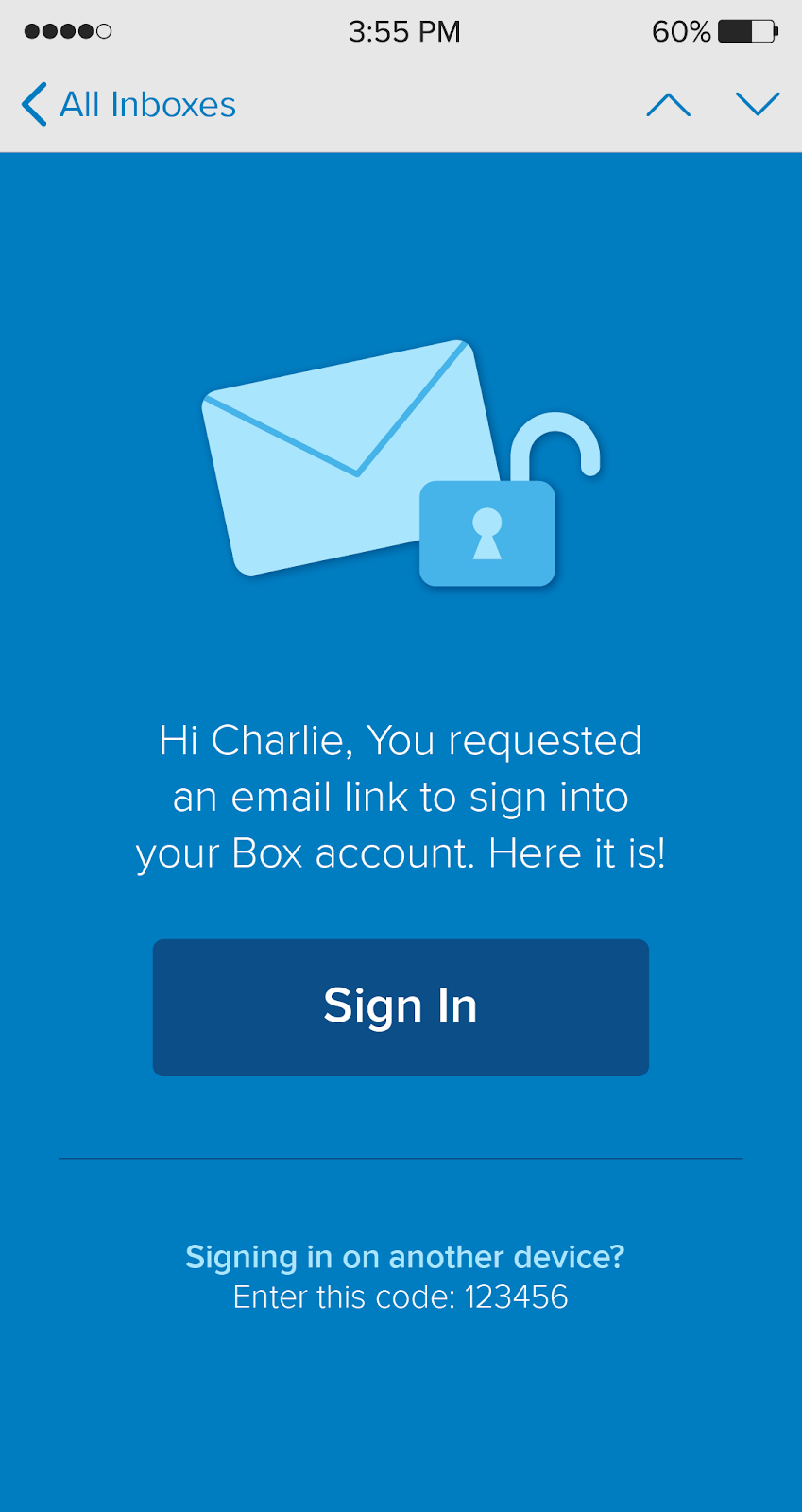
- The user enters their email address at your sign-in screen.
- If it’s a registered email address, the user will receive an email with a magic link.
- The user opens the email and clicks the magic link to complete the sign-in process.
Alternatively, the user can be sent a live link at the time of registration that can be used subsequently for authentication. This procedure is similar to a password reset flow, where a user receives a secret link that allows them to bypass their password and create a new one. To establish magic login, app designers need to have a process for removing the password (and any associated resetting ceremonies) and instead sending a secret, single-use link to the user’s email address.
Developers can configure whether the link stays valid for set intervals of time or for the user’s session lifecycle. Clicking the link in time authenticates the user and sets a cookie that keeps them logged in for the duration of their session.
Magic links work in a way that users have seen hundreds of times through password resets, except the user doesn’t need to remember or enter a password to access their account. Thanks to this, magic links streamline the login process and provide an inviting user experience while imposing no hardware requirements.
How can I use magic links?
If you’re thinking about implementing magic links, you’re likely looking to add user-friendly features to your app that contribute to a strong security strategy. We’ll run through some of the main use cases for magic links so you can get a sense of what they offer.
Magic links:
- Are ideal for infrequent login demands. Magic links are issued at the start of each user session, authenticating the user on a single-use basis. This makes them highly compatible with apps that require infrequent or single authentication, providing a frictionless path to access.
- Pair well with WebAuthn. WebAuthn is a standards-based framework for passwordless authentication that allows web applications to use registered devices as authentication factors. In addition to an internal authenticator (e.g., supporting browsers like Google Chrome), WebAuthn incorporates a range of external authenticators, like YubiKeys and biometric identifiers. Magic links can provide an alternative layer of authentication for apps that support WebAuthn without requiring companies and users to implement additional hardware.
- Prevent password-based attacks. For the fourth year in a row, Verizon's Data Breach Investigations Report finds stolen credentials the top hacking tactic, with 80% of breaches classed as “hacking” involving stolen or brute-forced credentials. With password-dependent attacks like credential stuffing and phishing on the rise, magic links are a ward against the security risks inherent to passwords—poor passwords are easy for others to guess or obtain, and the frustration of remembering different credential sets promotes poor security behaviors, like setting weak and recycled passwords across accounts.
- Streamline account creation and logins. With magic links, app developers can bootstrap users into registration and sign-in at the same time. New users can use the registration step to get a sign-in link without needing to enter details or set credentials, reducing user friction and essentially allowing for account creation at any point in the user journey.
What are the benefits of magic links?
Organizations that implement magic links benefit in a variety of ways. Magic links allow for:
- Easy authentication deployment and use. As magic links follow a near-identical flow to password resets, implementing them means making some minor adjustments in code at no extra cost.
- Seamless onboarding. Users just need to enter their email address and click the magic link to register for an app, providing a simple and inviting onboarding process.
- Reduced login troubleshooting. By trading passwords for magic links, organizations experience reduced administrative overhead. You’ll spend less time dealing with security alerts from failed logins and will no longer need to act on new password requests.
- Increased app adoption. A positive experience with the login process through “magic” passwords can encourage users to continue using your app. Magic links allow you to build loyalty and a returning fanbase.
- Fewer cart abandonments, more conversions. Simplifying the login process at checkout means you’ll have fewer customers who give up on their purchases, opening the door to more conversions on both web and mobile.
- Decreased attack surface. Each set of weak or recycled credentials is an attack window into your organization. By virtue of going passwordless, you’ll reduce the risks of account takeover and data breaches via compromised credentials.
There are also a number of benefits for end users, too:
- No hardware dependency. While authentication methods like hard tokens and biometrics depend on users owning certain technologies, magic links come with no resource demands. This means there’s no barrier to entry, making authentication accessible to the widest possible user base.
- Familiar, intuitive user experience. Magic links offer a simplified version of the familiar password reset process, requiring little effort to register and sign in.
- High usability on a range of devices. Magic links offer easy authentication on any device where users can access their emails, meaning they’re equally viable across smartphones, tablets, laptops, and desktops. Magic links will authenticate users on the device where they click the link. As it’s instinctive for users to open emails on the device they’re working from at the time, this shouldn’t introduce any friction.
What are the challenges of using magic links?
Magic links may offer stronger protection than passwords, but they come with several security blindspots to address:
- Security is tied to the user’s email account. This presents its own set of security risks. Magic emails may be sent insecurely between mail servers and could be visible to employees at the user’s email provider. User inboxes are also easily accessible on unattended devices. To keep magic emails secure beyond doubt, users need to protect their email accounts with multi-factor authentication.
- Admins have no control over link sharing. As with passwords, poor security behaviors introduce vulnerabilities. Admins have no way to see or prevent users from sharing confidential links with others.
- Susceptible to man-in-the-middle attacks. Unless users access their emails through encrypted networks, hackers can intercept less secure connections and steal the session token from a magic link.
Magic links: The bottom line
Ultimately, magic links are a great means of providing your users with convenient logins—but they’re not the most secure authentication method.
One workaround would be to use magic links in tandem with Okta Adaptive MFA. Given the vulnerabilities of magic login, setting a policy to prompt for additional authentication when users are accessing their email accounts on untrusted (and unencrypted) networks will mitigate the risk of man-in-the-middle attacks. You can use Adaptive MFA to implement dynamic and contextually aware access policies—for example, you might choose to deploy magic links only to registered users on encrypted networks.
If security is your chief concern, we recommend exploring additional methods of protecting logins. Making use of WebAuthn, for instance, balances password-free convenience with stringent protection, pairing magic links with a variety of higher assurance authentication factors to keep your organization and users secure.
Passwordless authentication is the way forward. Explore our full slate of passwordless building blocks—and understand why your customers need them. For developers, check out our tools that’ll help you build secure authentication into your app.






