Executive summary
Okta Threat Intelligence, working with our partners at the University of Cyprus, have connected a cluster of fraudulent account registration activity to a sprawling cybercrime ecosystem based in Vietnam.
Fraudulent online accounts are more than just a nuisance; they are a critical tool for large-scale financial fraud. From spam to phishing to devastating interpersonal fraud scams, these accounts provide a veneer of legitimacy that allows criminals to abuse platforms and customers of those platforms.
In late 2025, Okta Threat Intelligence investigated signup fraud campaigns using infrastructure clusters internally designated as O-UNC-036 that relied on disposable email addresses in order to execute SMS pumping attacks, which is also known as International Revenue Sharing Fraud (IRSF). In this scheme, malicious actors automate the creation of puppet accounts in a targeted service provider. Fraudsters use these account registrations to trigger SMS messages to premium rate phone numbers and profit from charges incurred. This activity can prove costly for service providers who use SMS to verify registration information in customer accounts or to send multifactor authentication (MFA) security codes.
In the course of this investigation, Okta Threat Intelligence and our partners observed links from O-UNC-036 to dozens of websites that cater to individuals who want to conduct online fraud. This cybercrime-as–a-service (CaaS) ecosystem provides paid infrastructure and services that make it easier for other individuals to conduct online fraud. Many of these online storefronts sell user accounts that have been hijacked or created through automated means. This post will explain the threat that fraudulent registration poses to service providers, how it is executed and steps that can be taken to mitigate abuse.
Fuel for fraud
There is demand and a brisk trade for accounts on social media sites and services like LinkedIn, Instagram, Facebook, and TikTok. Fraudulent accounts can be leveraged in numerous ways that can impact the reputation of a service provider. Accounts can be used to send spam or to direct unsuspecting users to phishing sites. Fraudulent account registration is used to gain access to limited products such as concert tickets, to exploit free trials or manipulate product reviews. This all results in an erosion of trust in a service provider and a degraded experience for users.
Fraudulent accounts are also used to approach targets of interpersonal fraud scams: cyber-enabled crimes that range from investment and cryptocurrency scams to romance and sextortion schemes. Often referred to as “pig butchering,” targets are persistently engaged online and over the phone in schemes designed to defraud them. These operations have exploded in recent years in southeast Asia, particularly in border areas near China, Myanmar, Thailand and Cambodia, and are run out of large compounds by organized criminal networks.
This activity has, according to an April 2025 report by the United Nations Office on Drugs and Crime, resulted in a “surge of specialized service providers” that feature a “range of merchants specializing in the sale of fraud kits, stolen data, malware, AI-driven tools, and various underground banking, money laundering and cybercrime services utilized by other criminals targeting victims globally.”
This trade often happens in relatively open forums, on social networking sites, clear-web websites and on messaging platforms including Telegram. The tools enable fraud perpetrators to find targets, learn about them, gain their confidence and eventually cause them financial losses.
“When [scammers] use fake accounts to win the trust of people, they end up with a lot of personal data about them. They can do lots of damage to those victims,” says Hieu Minh Ngo, a Vietnamese cybercrime investigator who contributed to the U.N. report and runs ChongLuaDao, nonprofit scam-fighting cybersecurity awareness organization.
The “web shops” we observed used website templates produced by a Vietnam-based web design and marketing company. We observed these cookie-cutter templates used for dozens of sites offering account-related products as well as other services used for fraud, such as falsely inflating the popularity of social media posts, phone farms for managing large numbers of accounts, residential proxies and “anti-detect” browsers, which are used to evade the tools used by security teams to detect account takeovers.
While the activity we observed predominantly targets Vietnamese speakers, many of the fake account vendors using these e-commerce templates also seek English-speaking buyers, extending the reach of this threat beyond Vietnam.
In December 2023, Microsoft undertook legal action against a Vietnamese CaaS group that sold fraudulent created Outlook and Hotmail accounts. The group, Storm 1152, created and sold 750 million fraudulent Microsoft Outlook and Hotmail accounts that were used for fraud, ransomware and extortion. The action temporarily disrupted Storm 1152. However, the group has since reformed, and Microsoft filed a second civil lawsuit in July 2024 in an effort to disrupt new infrastructure. We have not observed direct links between the activity we observed and Storm 1152.
Wanted: fake accounts
There is a chicken-and-egg problem fraudsters face when they need to create large numbers of synthetic user accounts with a service provider. Each new account requires a unique email address. Our insight into the fraudulent activity started with a set of disposable email domains used by O-UNC-036.
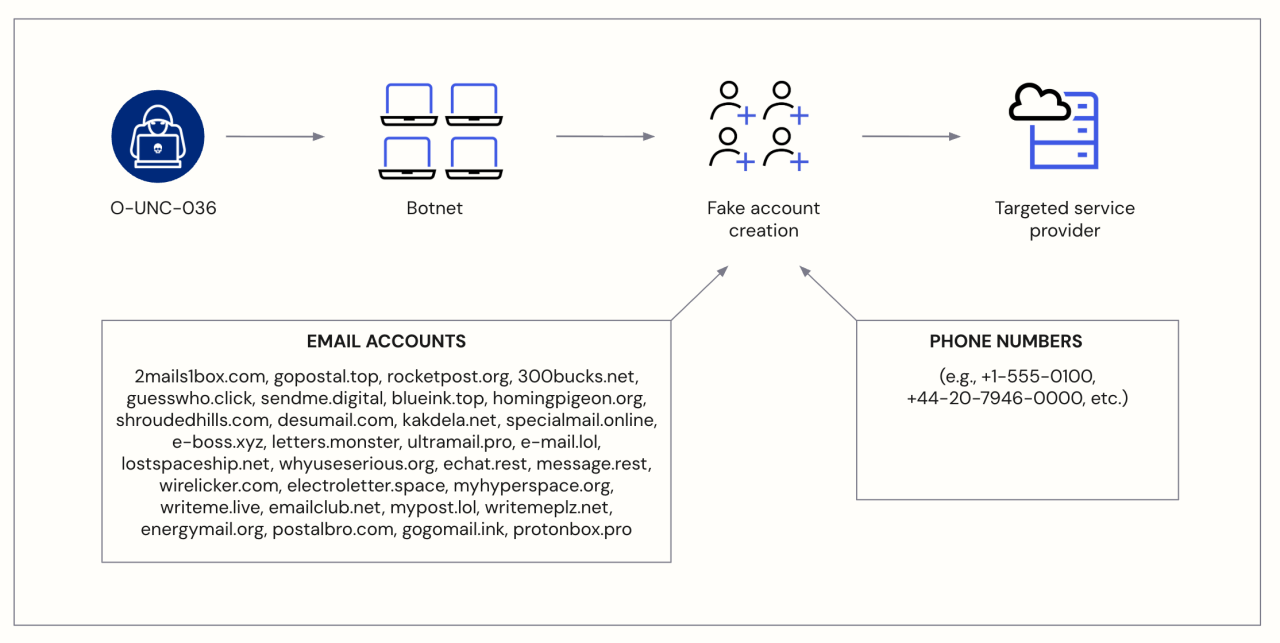 Fig. 1. Fraudulent sign-ups are often created with the help of botnets.
Fig. 1. Fraudulent sign-ups are often created with the help of botnets.
There are a variety of email services that offer “disposable” email addresses to cater to users with privacy concerns. These addresses can be generated en-masse and the services are often designed to cater to users that will likely only use an account for a short time. Correspondence to an address is typically available via an online service, and the email address provided may only be functional for as little as 10 minutes before being disabled. For fraudulent registrations, this arrangement is fine, since users of the service have no intention of actually using the address and may need only to view its inbox once to receive a verification code.
Okta Threat Intelligence observed a flood of suspicious-looking account registrations using multiple disposable email domains, which given the nature of the services is a red flag that the registrations are not being used for legitimate purposes. Our analysis of email provider domains turned up visual similarities that led us to a sprawl of web-based storefronts hosted in Vietnam and involved in the sales of web-based accounts.
All about MMO (“Make Money Online”)
The website CMSNT.co appears similar to other marketing and website design services aimed at the e-commerce market.
“We design websites for your online money-making ventures,” the site reads. “Automate your online money-making process.”
What follows is a series of tiles that advertise website templates.
 Fig. 2. The front page of CMSNT[.]co, a Vietnam-based company that sells website templates (translated by Google).
Fig. 2. The front page of CMSNT[.]co, a Vietnam-based company that sells website templates (translated by Google).
The website templates reveal a common theme: the sale of digital accounts for various types of services, including email providers, gaming sites, and social media services. However, there is no indication that CMSNT[.]co is involved itself in the sale of digital accounts or activity that could potentially violate computer crime laws.
Some templates are customized for the sale of accounts linked to video streaming, graphic design or AI chatbot service subscriptions, or for the sales of application software keys. Another template is a Social Media Marketing Panel, which appears to be designed as a storefront for a service that artificially boosts social media engagement on major social network sites. This inflation can include bogus “likes”, comments or views. CMSNT[.]co says that “AI technology simulates real user behavior. No password required, just a public link. Trusted by over 15,000 customers.”
Another template is customized for offering chron job services (scheduled tasks) using python, which can be used for tasks like web scraping.
Our research revealed that CMSNT[.]co’s templates are used by dozens of websites. But not everyone is paying CMSNT[.]co to use them. At some point the source code for some templates was leaked, resulting in some entities using the templates without paying for licenses.
One of those freeloaders is Via17[.]com. “Via” is a slang term for hacked accounts, and it appears frequently on sites that are selling accounts. The compromised accounts may have been acquired using brute-force techniques, where attackers try different combinations of usernames and passwords, or from “logs” collected by information stealer (infostealer) malware. These types of malware logs, which can contain login credentials, payment card details, cryptocurrency wallet information and personally identifiable information extracted from infected devices, are routinely sold on underground forums and messaging platforms.
In an instructional video on YouTube, a person affiliated with the site bills Via17[.]com as the “#1 reputable website providing Facebook accounts.” The video focuses on how people can access a Facebook account using a session token, which is a small data file that allows a user to remain signed into a website. Via17[.]com sells session tokens (also referred to as “cookies”) as part of some fake account offerings.
![The front page of Via17[.]com (translated by Google).](/content/okta-www/se/en-se/blog/threat-intelligence/vietnamese-cybercrime-operation-enables-fraudulent-account-signups/_jcr_content/root/container_wrapper/container_main/container_right/container/image_1095968747.coreimg.png/1772514937615/oti-viet-fig3cmsnt.png) Fig. 3. The front page of Via17[.]com (translated by Google).
Fig. 3. The front page of Via17[.]com (translated by Google).
One of the primary products at Via17[.]com is the resale of accounts from social networking sites. One package offers Vietnamese Facebook accounts with 10-50 friends with two-factor authentication enabled. More than 1,000 accounts are available at a price of 55,240 Vietnamese dong, or US$2.13 each. Other tiles advertise “vintage” Facebook accounts as old as 2006. Some accounts are listed as “real” accounts. It is unclear how Via17[.]com or its users have acquired them prior to sale. “Clone” accounts are created by software, according to the site. Depending on the type of account purchased, the data provided includes a userid, password, the ability to collect 2FA codes or notifications, a recovery email address and session tokens.
![A screenshot of “cloned” accounts on Via17[.]com, a Vietnamese-language website that sells social media accounts.](/content/okta-www/se/en-se/blog/threat-intelligence/vietnamese-cybercrime-operation-enables-fraudulent-account-signups/_jcr_content/root/container_wrapper/container_main/container_right/container/image_112546195.coreimg.png/1772514937659/oti-viet-fig4cmsnt.png) Fig. 4. A screenshot of “cloned” accounts on Via17[.]com, a Vietnamese-language website that sells social media accounts.
Fig. 4. A screenshot of “cloned” accounts on Via17[.]com, a Vietnamese-language website that sells social media accounts.
A similar account marketplace is nladsgiare[.]shop, which also runs the CMSNT[.]co website code. The advertisements for accounts on this site show the role that disposable email accounts play in the account trade. A section of the front page of the site advertises Facebook accounts that have Thai or “foreign” names that are linked to disposable email addresses from a service called mailclone[.]site.
![The main page for mailclone[.]site.](/content/okta-www/se/en-se/blog/threat-intelligence/vietnamese-cybercrime-operation-enables-fraudulent-account-signups/_jcr_content/root/container_wrapper/container_main/container_right/container/image_1508310858.coreimg.png/1772514937702/oti-viet-fig5mailclonesite.png) Fig. 5. The main page for mailclone[.]site.
Fig. 5. The main page for mailclone[.]site.
Anyone can generate an email address on mailclone[.]site. Content sent to the address — such as an email verification link — is visible directly on the site. The same style of verification is recommended for accounts on Via17[.]com, with the site recommending buyers get codes sent to accounts from another free, temporary e-mail service, temp-mail[.]io.
![Via17[.]com mentions a disposable email service called temp-email[.]io which allows users to generate email addresses that are valid for periods ranging from 10 minutes up to an hour.](/content/okta-www/se/en-se/blog/threat-intelligence/vietnamese-cybercrime-operation-enables-fraudulent-account-signups/_jcr_content/root/container_wrapper/container_main/container_right/container/image_1719554353.coreimg.png/1772514937747/oti-viet-fig6temp-mail.png) Fig. 6. Via17[.]com mentions a disposable email service called temp-email[.]io which allows users to generate email addresses that are valid for periods ranging from 10 minutes up to an hour.
Fig. 6. Via17[.]com mentions a disposable email service called temp-email[.]io which allows users to generate email addresses that are valid for periods ranging from 10 minutes up to an hour.
Via17[.]com recommends 11 other disposable email services that can be used for account registration.
![Other disposable email services recommended by Via[.]17.](/content/okta-www/se/en-se/blog/threat-intelligence/vietnamese-cybercrime-operation-enables-fraudulent-account-signups/_jcr_content/root/container_wrapper/container_main/container_right/container/image_1779573270.coreimg.png/1772514937791/oti-viet-fig7via17.png) Fig. 7. This screenshot shows other disposable email services recommended by Via[.].com.
Fig. 7. This screenshot shows other disposable email services recommended by Via[.].com.
Conclusion
Preventing fraudulent account registration is a careful balance between preventing fraud and introducing undue friction on customers. (Users may be legitimately using masking or email forwarding services - consider Apple’s Hide My Email feature). Organizations are typically prepared to tolerate a certain level of fraud to avoid events in which potential customers cannot complete a registration - this must be balanced against the risks an abundance of bogus accounts poses via a degraded customer experience.
Mitigations
Auth0
Auth0 customers have several tools at their disposal to mitigate fraudulent signups before, during and after the account creation process. Okta Threat Intelligence has written a playbook to guide efforts to mitigate abuse.
To protect their tenants from signup attacks, Auth0 customers can:
Use Bot Detection to challenge bots with a CAPTCHA of your choice within the configured risk tolerance.
Tighten Suspicious IP Throttling limits on signup to reduce the number of accounts attackers can make from individual IPs.
Create a Tenant Access Control List (ACL) rules, which denies observed malicious activity from sources based on indicators such as IPs, ASNs, geolocation values and JA3/JA4 signatures and has been shown to help mitigate signup attacks.
Enforce email verification using post-login Actions or a one-time password.
Block registrations that use known disposable email domains with pre-user registration actions.
Detect signup attacks with Auth0’s open source Security Detection Catalog, especially the rules detecting risks of signup fraud by disposable domains and by volume and mass unverified account creation events.
Implement identity proofing tools, like those in the Auth0 Marketplace.
Okta Customer Identity
Okta Customer Identity also has controls that can be used to mitigate fraudulent sign up. Customers can block attackers before, during and after the signup process:
Identity Threat Protection, which is now in early access for Okta Customer Identity, evaluates IP reputation and looks at behavioral signals to block scripted account signups and signins and detect when threat actors use compromised credentials to sign up for accounts.
Use Okta APIs or Workflows to identify large batches of fraudulent registrations. Okta has published a sample workflow specifically to manage the abuse of self-service registration. The workflow compares the email address from a registration attempt and runs it against a customer-defined list of malicious or disposable domains. The workflow can be configured to deactivate these accounts.
Consider forcing verification of newly registered accounts via email link or OTP validation.
- Consider performing identity-proofing with specialist third-party providers for users of high value services.
- Consider blocking the most risky anonymizers and proxies by leveraging enhanced dynamic network zones. This stops attackers from reaching registration pages from high-risk services. Network blocking is the most extreme response and may not be an option for some.









