Identity has become the primary attack surface for modern enterprises. More than 80% of breaches stem from identity-based attacks, while organizations must now secure not only human users, but also service accounts, workloads, and an exploding population of AI agents, often across hybrid and multi-cloud environments. In some organizations, non-human identities can outnumber human users by 50:1 or more, dramatically expanding the attack surface.
For CISOs, the business risk of inaction is no longer theoretical. A single compromised identity can trigger operational disruption, regulatory penalties, lost revenue, and damaged customer trust, while diverting security and IT resources from growth and innovation.
Most enterprises have responded by investing in identity security tools across access management, governance, privileged access, threat detection, and more. But the real question isn’t whether you have these tools. It’s whether they work together to reduce breach risk, improve operational efficiency, and secure the growing population of AI agents.
When identity systems operate in silos, security teams lack the unified visibility and control needed to stop identity-based attacks. Instead of reducing risk, fragmented identity architectures often create the very gaps attackers exploit.
To close these gaps, security leaders are adopting a modern architectural approach: identity security fabric, a unified layer that weaves together identity capabilities to secure human, non-human, and AI agent identities across your environments.
Why fragmented identity tools are a security liability
Most enterprises didn’t intentionally build fragmented identity security stacks. It’s the result of how identity programs evolved.
Organizations typically start with foundational controls like single sign-on (SSO) and multi-factor authentication (MFA). As identity programs mature, they add identity governance, privileged access management, and threat detection to address new risks and compliance requirements.
Over time, this creates a patchwork of tools operating in silos. Security teams often rely on custom integrations and manual processes just to keep identity workflows functioning.
Even then, gaps remain. The business consequences are significant.
- Breach exposure: When identity tools operate in silos, attackers can use a compromised identity to move laterally across systems undetected, turning a single account compromise into a full-scale breach.
- Operational drag: Managing multiple identity tools creates administrative overhead and integration complexity. Teams spend time maintaining connections between systems instead of improving security outcomes. Visibility becomes fragmented and audits become harder to manage.
- AI blind spots: AI agents and other non-human identities are growing rapidly. Fragmented tools couldn’t keep up with the scale to discover, govern, and revoke access for these identities, leaving unmanaged access paths and limited auditability.
These risks show up in everyday operations:
- An overprivileged service account can persist for months because no single tool has a complete view of its access.
- Manual provisioning workflows introduce unnecessary risk during onboarding or role changes.
- Shadow AI agents spin up outside central IT governance with no verified owner.
Fragmented identity security doesn't just leave security gaps, it actively undermines your ability to protect revenue, maintain compliance, and scale with confidence.
Rethink your strategy: Adopt an identity security fabric
That’s why Identity security fabric is emerging as a critical foundation for modern enterprise security.
Identity security fabric is an architectural approach that weaves identity capabilities together so they operate as a unified security layer rather than fragmented point solutions.
With identity security fabric as the central control plane, security teams gain the ability to coordinate defense, detect risk faster, enforce least-privilege access, and respond immediately to identity-based threats.
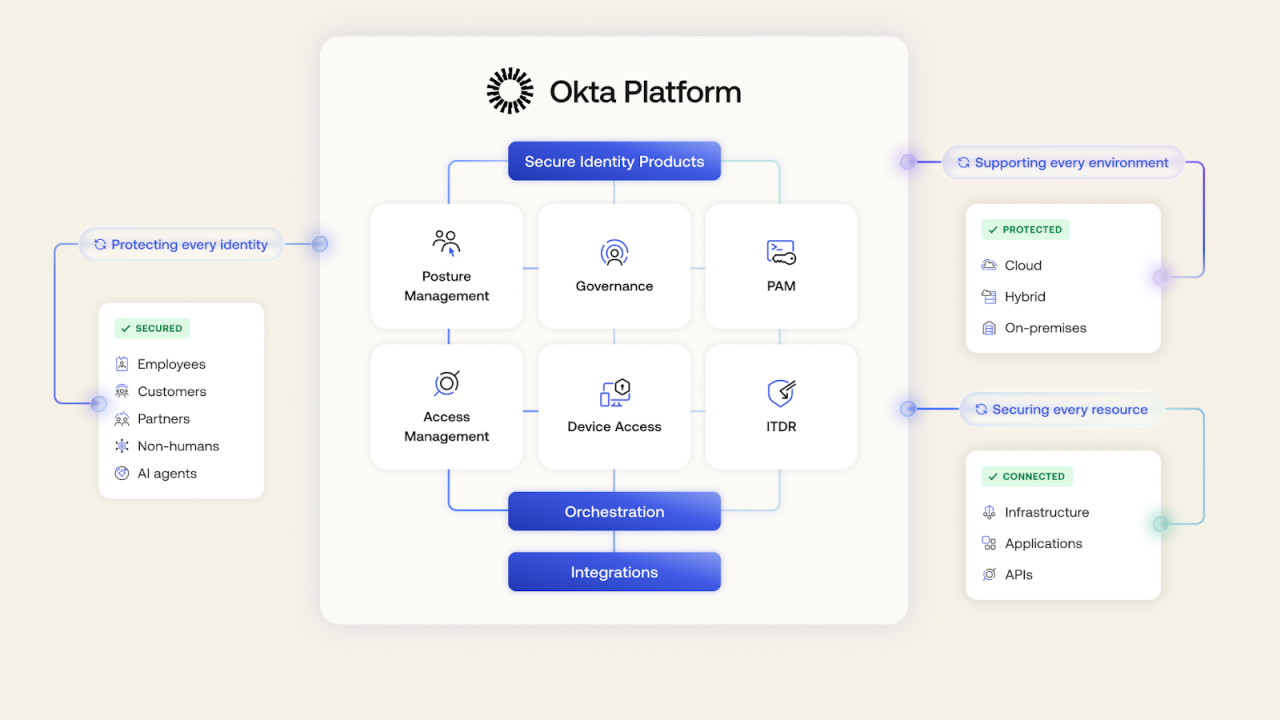
The Okta Platform brings the identity security fabric to life.
The Okta Platform is purpose-built to deliver identity security fabric. Not as a collection of stitched-together tools, but as a unified platform engineered from the ground up.
Okta brings together identity security capabilities across access management, governance, privileged access, posture management, and threat detection within a single platform. These capabilities work together as one orchestrated layer, delivering end-to-end security with unified visibility, control, governance, and remediation for human, non-human, and AI agent identities across cloud, on-premises, and hybrid environments.
This unified approach helps security leaders achieve three outcomes that matter most:
- Identity security breach protection: Proactively detect, contain, and remediate identity-based attacks before, during, and after authentication, minimizing the risk of breaches and the catastrophic losses that follow.
- Operational efficiency & resilience: Consolidate fragmented identity solutions into a single, unified platform, streamline end-to-end identity lifecycle, and maintain audit readiness, freeing resources for growth and innovation.
- AI visibility & control: Establish a centralized control plane for all AI agent identities, enforce least-privilege access, and maintain an instant "kill switch" to revoke sessions and tokens across integrated applications.
For organizations navigating hybrid infrastructure, AI adoption, and rising regulatory pressure, identity security fabric is quickly moving from nice-to-have to a strategic foundation for enterprise security.
Identity security fabric in action: key use cases
Identity security fabric isn’t just a concept, it delivers measurable value across real-world security priorities. Below are three key use cases where identity security fabric drives stronger outcomes for modern enterprises.
Secure AI agents
AI agents are your newest digital workforce, but right now, most are operating in the shadows. Okta for AI Agents provides an identity layer for the agentic era. We enable you to bring your AI agents into your identity security fabric—allowing you to see, manage, and govern AI at scale.
→ Learn about Okta for AI agents
Secure hybrid & on-prem environments
Managing identity and security across modern cloud applications and legacy on-premise systems has become a critical challenge for many large organizations. They are having to manage access and security policies in different point solutions and cobble together risk insights to try to protect their entire environment.
The Okta Platform enables you to extend an identity security fabric seamlessly to your legacy on-premises systems and applications. This modern approach centralizes visibility, governance, access, and protection across your hybrid environment, allowing you to consolidate siloed directories and manage security for your cloud and on-prem resources from a single control plane.
→ Learn how to secure your hybrid & on-premises environment
Enable security-driven governance
For decades, Identity Governance and Administration (IGA) has been treated as a siloed, reactive “check-the-box” compliance exercise performed only a few times a year. This leaves gaps for attackers to exploit.
Okta’s platform-based approach helps enable security-driven governance, where all the components necessary to drive real security risk reduction are connected. Identity and access data, detections, and governance logic coexist within a single, unified identity security fabric.
→ Learn how to enable security-driven governance
Secure workforce onboarding
New hires represent a critical vulnerability window. Traditional onboarding prioritizes speed over security, leaving new employees exposed to phishing, credential compromise, and inappropriate access levels during their first 90 days when they're most vulnerable.
An identity security fabric transforms onboarding from a security liability into a security advantage by automating identity proofing, enforcing passwordless authentication from day one, and provisioning just-the-right-access through role-based, policy-driven processes.
→ Learn how to secure workforce onboarding
The bottom line: Identity security fabric is your business enabler
The identity challenges facing security leaders today, including hybrid complexity, AI-driven identity sprawl, and increasingly sophisticated attacks, can't be solved by adding more point solutions. They require a unified approach that brings visibility, control, governance, and remediation together into a single, cohesive layer to prevent, detect, and stop threats across the entire ecosystem.
Identity security fabric delivers exactly that: stronger security outcomes, greater operational efficiency, and the confidence to move fast without leaving gaps for attackers. It turns identity from the enterprise’s largest risk surface into one of its strongest security controls.
Don't let fragmented tools leave security gaps that attackers can exploit. Build a unified identity security fabric with Okta.
→ Explore more about identity security fabric
→ See identity security fabric in action
→ Talk to our identity security experts
These materials are intended for general informational purposes only and are not intended to be legal, privacy, security, compliance, or business advice. © 2026 Okta, Inc. and its affiliates.






