At one stage in mid-2025, Tycoon 2FA was responsible for more Identity Threat Protection (ITP) detections than any other phishing kit.
Tycoon 2FA offered threat actors an affordable, reliable service for MFA bypass against Microsoft 365 and Google Workspace tenants, without having to build and maintain the infrastructure required to perform Attacker-in-the-Middle (AitM) campaigns.
All that changed in March 2026, when a global law enforcement campaign disrupted 330 domains associated with Tycoon 2FA operations, including its distributed control panel and phishing pages built using the kit.
Okta Threat Intelligence can reveal that while the law enforcement operation put a significant dent in Tycoon operations, some of its operators continue to use the service. Several of its operators appear to have diversified into new forms of social engineering: including abusing the device code authorization flow.
The making of Tycoon
The original Tycoon phishing kit debuted in 2023 and did not include the ability to intercept session tokens.
But as controls like multifactor authentication (MFA) made traditional phishing more difficult, the kit evolved into Typhoon 2FA, an AiTM phishing kit that captured session tokens in real time. The service surged in popularity, primarily targeting Microsoft 365 and Google accounts.
Customers with little technical skill could subscribe to Tycoon 2FA via private Telegram channels for a few hundred dollars per month, allowing them to use an end-to-end service to execute account takeovers. Attackers sent tens of millions of phishing emails that directed unsuspecting users to Tycoon 2FA.
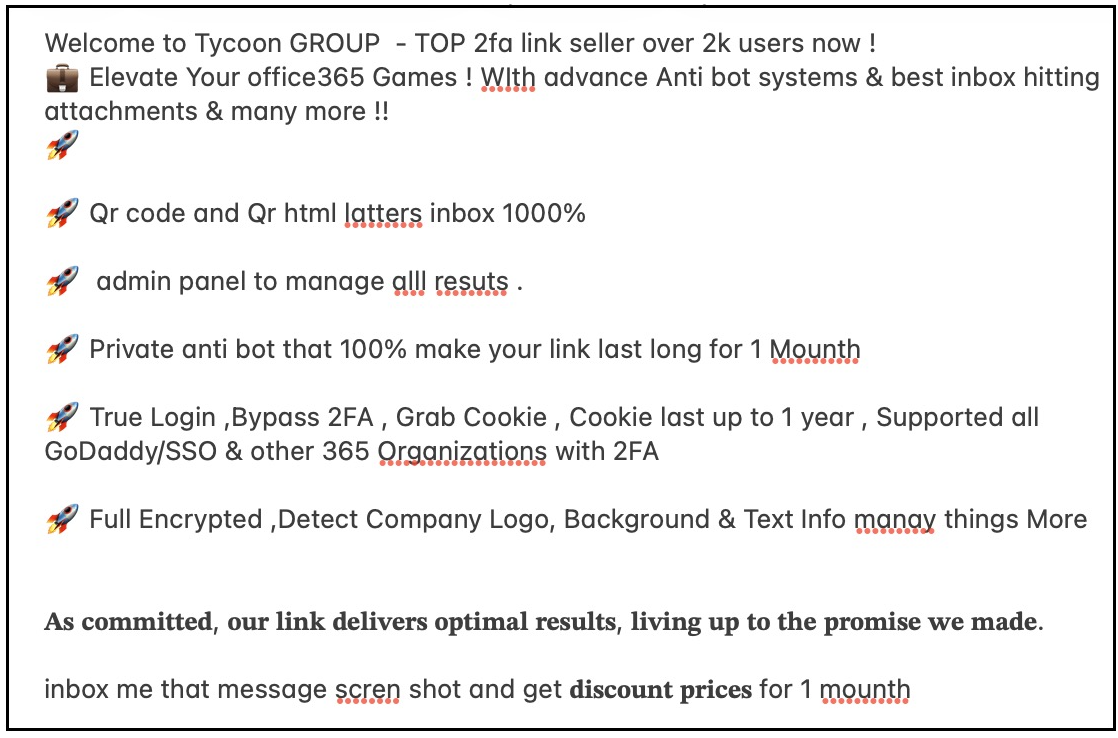 An advertisement on Telegram for the Tycoon 2FA PhaaS kit, which promotes key features including capturing session tokens and can be used to bypass MFA.
An advertisement on Telegram for the Tycoon 2FA PhaaS kit, which promotes key features including capturing session tokens and can be used to bypass MFA.
Targeted users were tricked into logging into familiar login pages that impersonated popular service providers. The targeted user’s email address was typically pre-filled into the phishing page.
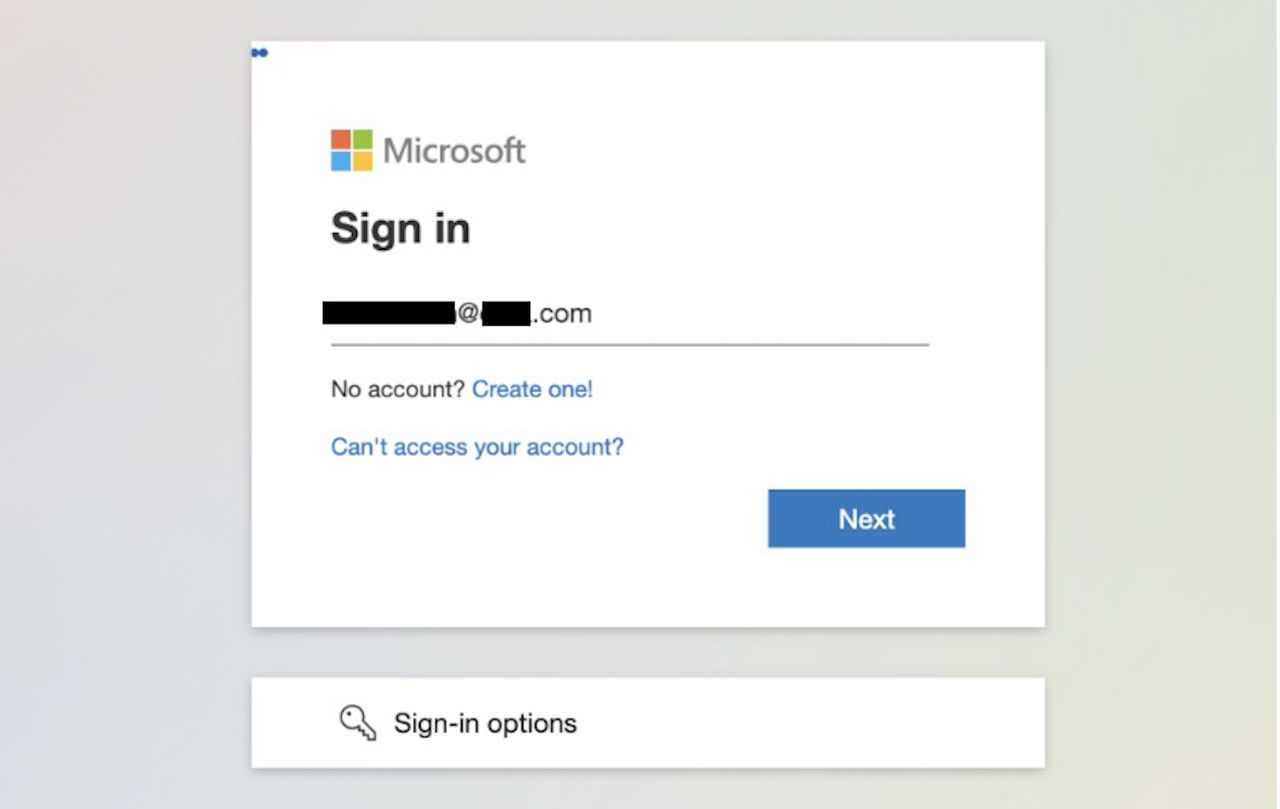 The email address of a targeted user was usually pre-filled on Tycoon 2FA phishing pages.
The email address of a targeted user was usually pre-filled on Tycoon 2FA phishing pages.
Using a transparent reverse proxy, Tycoon 2FA passed a person’s credentials to the legitimate service and relayed most types of MFA challenges satisfied by the user. When an impersonated service returned a session token to the user's browser after a successful authentication, Tycoon 2FA’s proxy grabbed it.
From there, attackers could replay the session token and gain account access. Replaying a session token bypasses both login and MFA challenges. Session token replay has grown into one of the most common identity-based attacks.
By mid-2025, Tycoon 2FA was the most-observed phishing kit with these AitM capabilities. In July 2025, Okta Identity Threat Protection detected 11,199 phishing attempts against Microsoft customers that federated identity to Okta - a figure that was more than double the previous three months combined.
By August 2025, detections fell to 5,982 before sliding further still. In the month prior to the March 4, 2026, takedown, Tycoon 2FA phishing attempts numbered just 885.
Perversely, we observed an increased number of detections in the weeks that followed the takedown activity.
Okta detected 1,470 Tycoon 2FA phishing attempts through the end of March 2026.
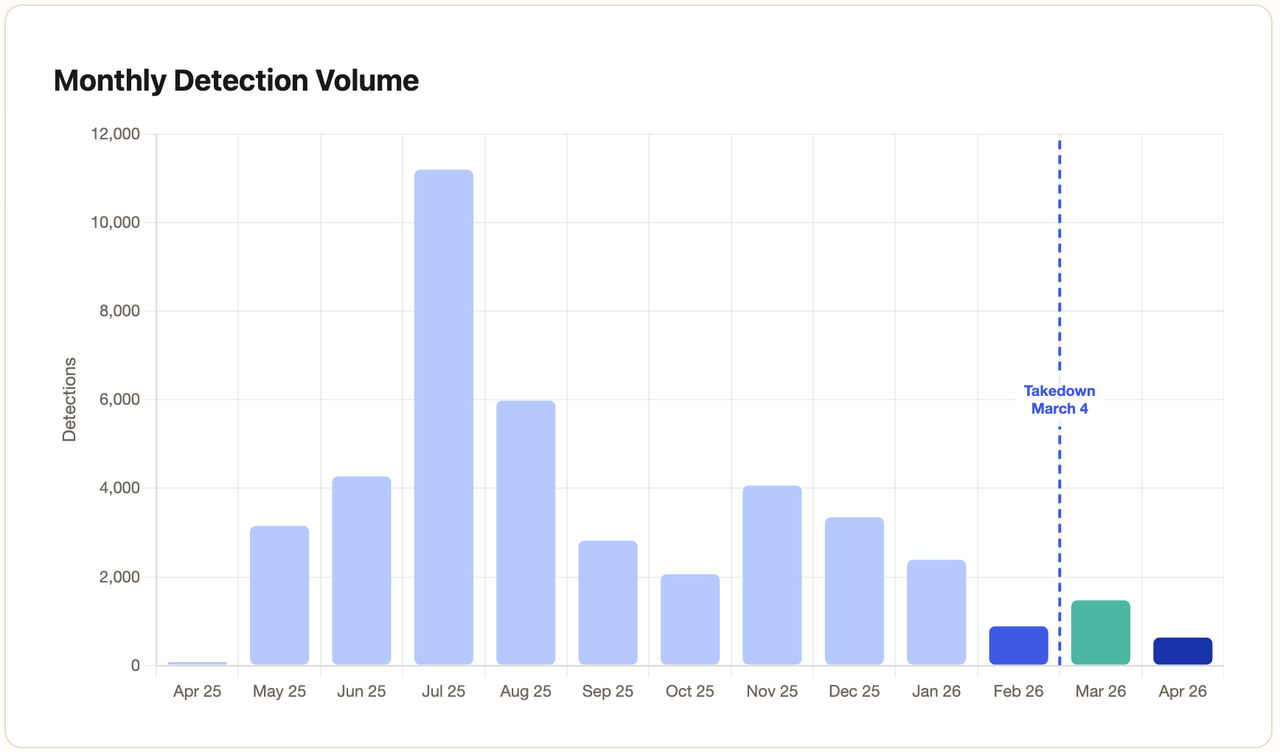
Detections observed leveraging Okta’s data have continued to trend downward but have not disappeared entirely, numbering 631 in April 2026.
Adaptation
In the wake of the disruption, the first obvious sign of how Tycoon 2FA operators would adapt was our detection of new and more diversified infrastructure.
Prior to the law enforcement action, most Tycoon 2FA detections originated from the networks of just three entities: Global Connectivity Solutions, M247 Europe SRL and Hivelocity.
Within one to two days of the disruption, new infrastructure started to appear. The only existing network operator that continued to host Tycoon 2FA infrastructure was M247 Europe SRL. Four new operators were observed hosting Tycoon 2FA-related activity, including a few smaller providers.
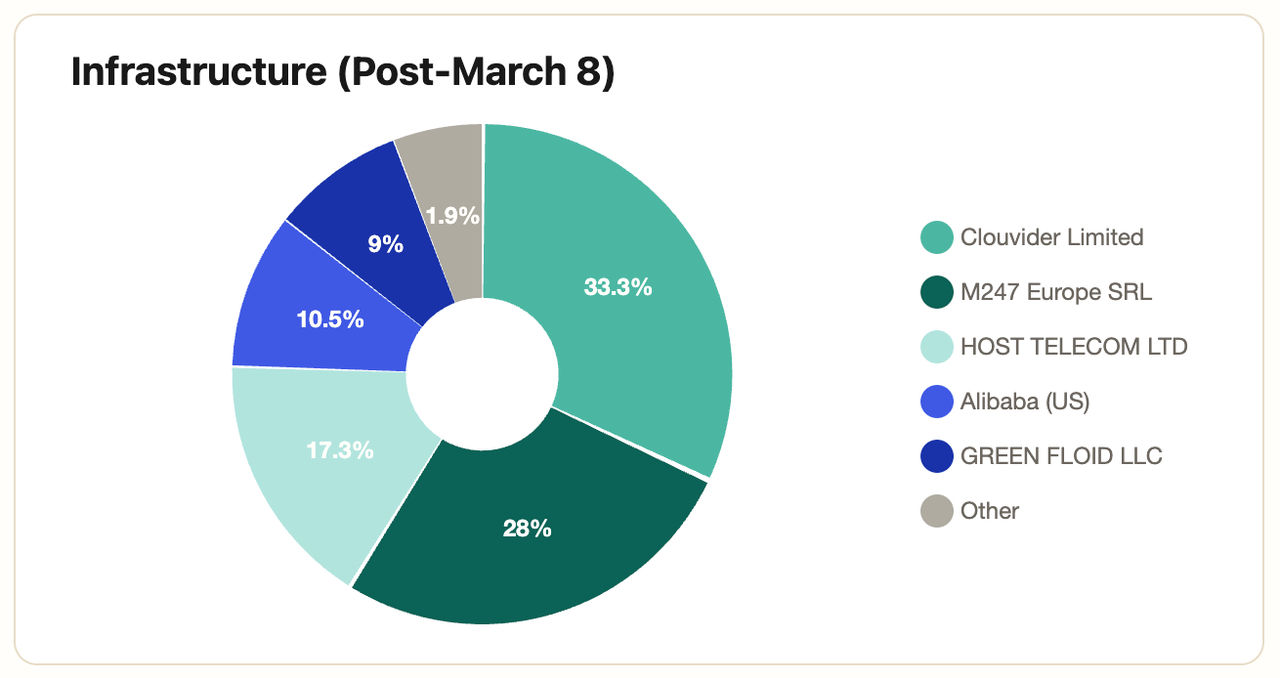 Tycoon 2FA phishing infrastructure was seen across new service providers as its operators diversified following a March 2026 law enforcement operation.
Tycoon 2FA phishing infrastructure was seen across new service providers as its operators diversified following a March 2026 law enforcement operation.
A more intriguing change is threat actor interest in a more covert form of attack: Device Code Phishing.
In this scheme, threat actors abuse the OAuth 2.0 Device Authorization Grant, which is an authentication scheme designed for input-constrained devices that is also used frequently to authorize command-line applications. Given it is inconvenient to log in to a streaming video service via a TV, users are provided a code and directed to login on a device better suited to sign-in. Once authenticated, OAuth tokens are issued to the requesting client. Threat actors see great opportunity in this abstracted flow, as users approve access to an application that is not necessarily on their device. Unsurprisingly, device code phishing has become a productized cybercrime service. EvilTokens is one such hosted device-code phishing kit targeting Microsoft environments, amongst others.
Threat researchers at Proofpoint recently spotted a tantalizing clue that suggests that even Tycoon 2FA users are re-tooling in favor of this attack type. They discovered a PDF in a phishing email used in a device code phishing campaign that re-used an artifact related to a Tycoon 2FA URL.
Okta Threat Intelligence has directly observed strong similarities between past Tycoon 2FA campaigns and recent device-code phishing campaigns. Both re-use similar anti-analysis tradecraft, for example. These include evasion strategies in the phishing lures common to Tycoon lures. The device-code phishing pages employ CAPTCHAs and use multi-hop redirect chains through legitimate infrastructure providers before the actual phishing page is shown. Recent device-code phishing pages also employ similar anti-analysis techniques as Tycoon to attempt to deflect analysis.
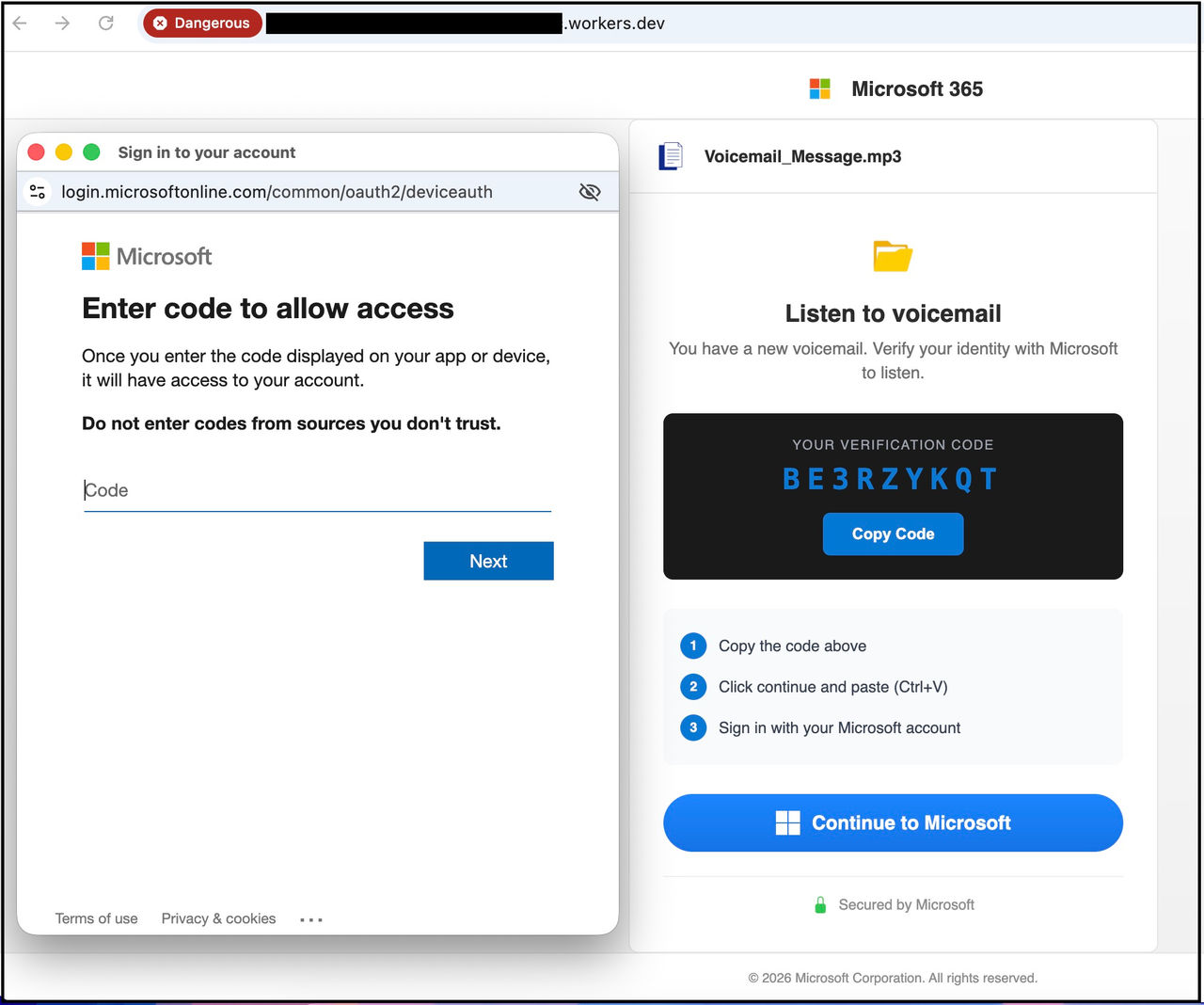 A screenshot of a recent device-code phishing attempt. In this example, a user is falsely informed of a pending voicemail. One sign-in is complete, the attacker has access to the person’s Microsoft 365 account.
A screenshot of a recent device-code phishing attempt. In this example, a user is falsely informed of a pending voicemail. One sign-in is complete, the attacker has access to the person’s Microsoft 365 account.
AitM: Still prevalent and potent
This type of retooling we have observed is part and parcel of cybercrime. It does not mean that imposing costs on the cybercrime ecosystem is fruitless. We should expect that profitable cybercrime operations will adapt to the tools available.
There remain several viable Phishing-as-a-Service alternatives to Tycoon 2FA. While organisations continue to allow users to sign-in using low-assurance factors vulnerable to phishing (especially passwords and OTPs) AitM phishing will be an effective tool for attackers.
The prevailing defense to session token theft via phishing is to enroll users in phishing-resistant authenticators such as Okta FastPass or passkeys and to enforce the use of those factors in authentication policies. AitM phishing kits cannot defeat either of these factors, and Okta FastPass offers the additional utility of being able to provide server-side detections to Okta administrators when users are targeted.
Organizations that do not or cannot enforce phishing resistance can also use services that detect the attempted re-use of a token. These services are as relevant to any form of session token theft (including malware) as they are to phishing.





