Okta Privileged Access: Unlocking Zero Trust Security at the Infrastructure Level
Every company that operates production software has compliance requirements. The vast majority of those organizations also carry significant infrastructure in the cloud and/or on-premises. And they all require a safe way to provide access to their developer workforce. Traditionally, there were two ways to achieve this: building a DIY system to manage accounts and credentials or adopting a heavy-weight, traditional Privileged Access Management (PAM) product. Either method is notoriously time-consuming, slow to deploy, expensive to maintain, and often fails to meet its promise.
Today, I’m excited to announce an innovative third option that makes PAM simple and accessible. Our new product, Okta Privileged Access, leverages Okta’s centralized identity-centric policy framework to completely shift the old shared-account, credential model of legacy PAM and unites flexible, least-privileged access requirements with identity.
Securing critical computing resources with Okta Privileged Access
Of course, if you're an existing Okta customer using Advanced Server Access, leveraging an identity-centric approach to privileged access (as an alternative to traditional products and solutions) is nothing new. But you demanded more, so we've expanded our resource coverage to manage privileged access further across the IT stack. We’ve added support for databases, containers, and appliances, with additional session capture and logging capabilities for compliance and auditing.
The benefits of Okta Privileged Access include:
- Increased risk mitigation: Minimize the attack surface area of privileged accounts and credentials by offering just-in-time, least-privilege access controls.
- Reduction of operational burden: Retire legacy PAM products and error-prone manual operations by unifying privileged access with identity. You also get a seamless end-user experience with a fast deployment to production, lowering the lift experienced by IT teams.
- Velocity at scale: Use automation to remove barriers to cloud adoption, helping support the business of delivering highly available, resilient, performant, and secure production software. You’ll find it easier to apply security policies based on a user’s role and to audit when all the activity is tied to a specific person.
- Faster time-to-value: Resolve your challenging compliance requirements in less time, with less dedicated resources than traditional approaches. It also mitigates the risk of admin account credential sprawl—a basic requirement within all compliance guidelines.

A unified approach
With the introduction of Okta Identity Governance in addition to Okta Privileged Access, the Okta Identity Cloud is delivering a comprehensive solution to access management, identity governance, and privileged access. Okta’s unified platform meets enterprise challenges by bringing together core identity use cases in one centralized experience.
Okta’s unified approach to privileged access and governance delivers enterprises:
- A single control pane: brings together core identity issues in one, centralized experience, allowing for the management of governance and privileges for all types of access. This single system makes setup and management easier and, for compliance initiatives and access decisions especially, offers the best user experience and rich data insights.
- Faster time-to-value: organizations reach productivity more quickly and effectively than other SaaS alternatives, providing seamless access management across any hybrid or multi-cloud environment.
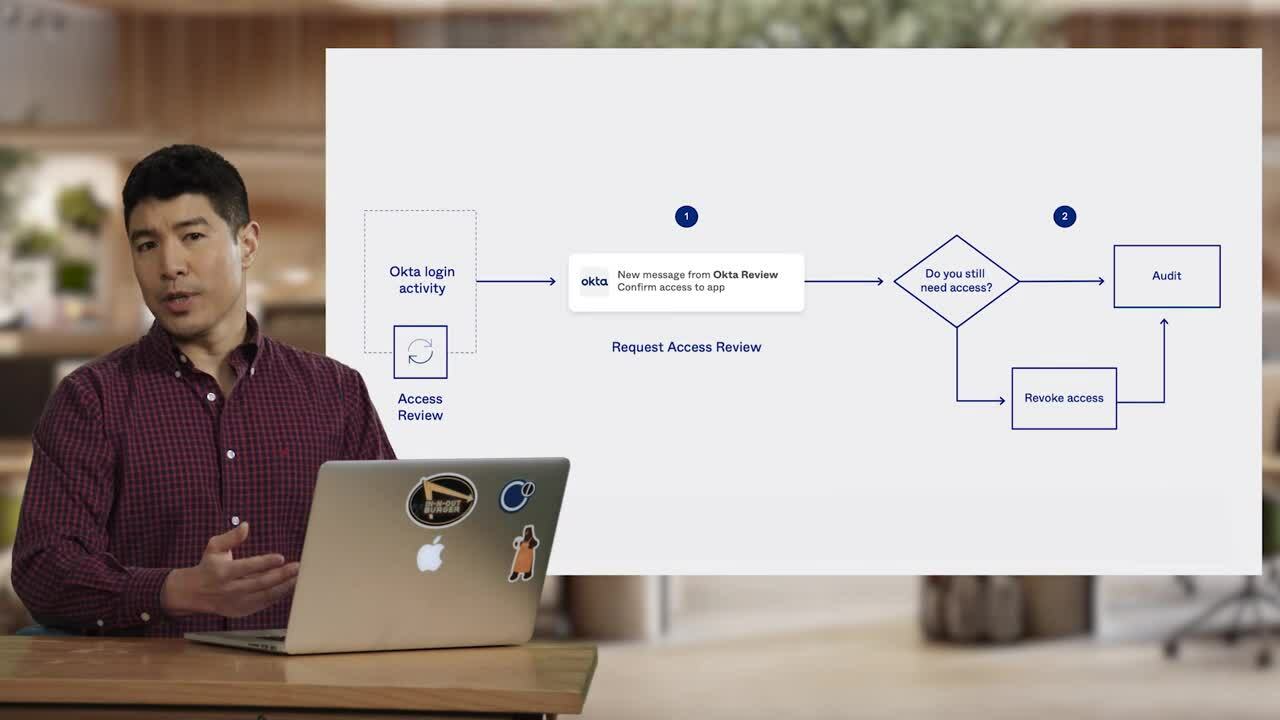
- Seamless automation: enables end-to-end access management and governance processes across the full IT stack. Organizations can leverage automation without having to code with Okta Workflows. They can also use our extensible APIs to create identity, access, and governance flows that match their business processes across their apps, infrastructure, and APIs.
Get started
Okta Privileged Access will be available to customers in Q2 2022. Learn more about Okta’s new product offerings that will reshape identity governance and privileged access.
Don’t miss out on all our Oktane21 Day 2 Product Roundtable and demos, and feel free to contact us with any questions.
Any unreleased products, features, or functionality referenced in this blog are not currently available and may not be delivered on time or at all. Product roadmaps do not represent a commitment, obligation, or promise to deliver any product, feature, or functionality, and you should not rely on them to make your purchase decisions.