ICAM Modernization: Honoring Your Legacy to Accelerate Your Future
Transcript
Details
Speaker 1: Hello everyone, and thank you for joining us today. Carahsoft Technology would like to welcome you to our Okta, Radiant Logic and SailPoint webcast. Before we get started, I would like to go over a few items.
Speaker 1: All of your lines have been muted to reduce background noise, and we hope you take advantage of the Q&A pod on the left side of your screen to ask any questions throughout the presentation. We will do our best to answer all of your questions at the end of the presentation. If for some reason we do not get to your question, the Okta, Radiant Logic, or SailPoint team at Carahsoft will follow-up with you offline.
Speaker 1: Carahsoft is a trusted government IT solutions provider, delivering software and support solutions to federal, state, and local government agencies. Carahsoft maintains dedicated teams to support sales and marketing for all of its vendors including Okta, Radiant Logic, SailPoint, Symantec, Adobe, EMC, VMware, and Red Hat. Our contact information will be at the end of the presentation, so please don’t hesitate to call or email us for any of your needs. This webcast is being recorded, and a copy of the presentation will be emailed to you.
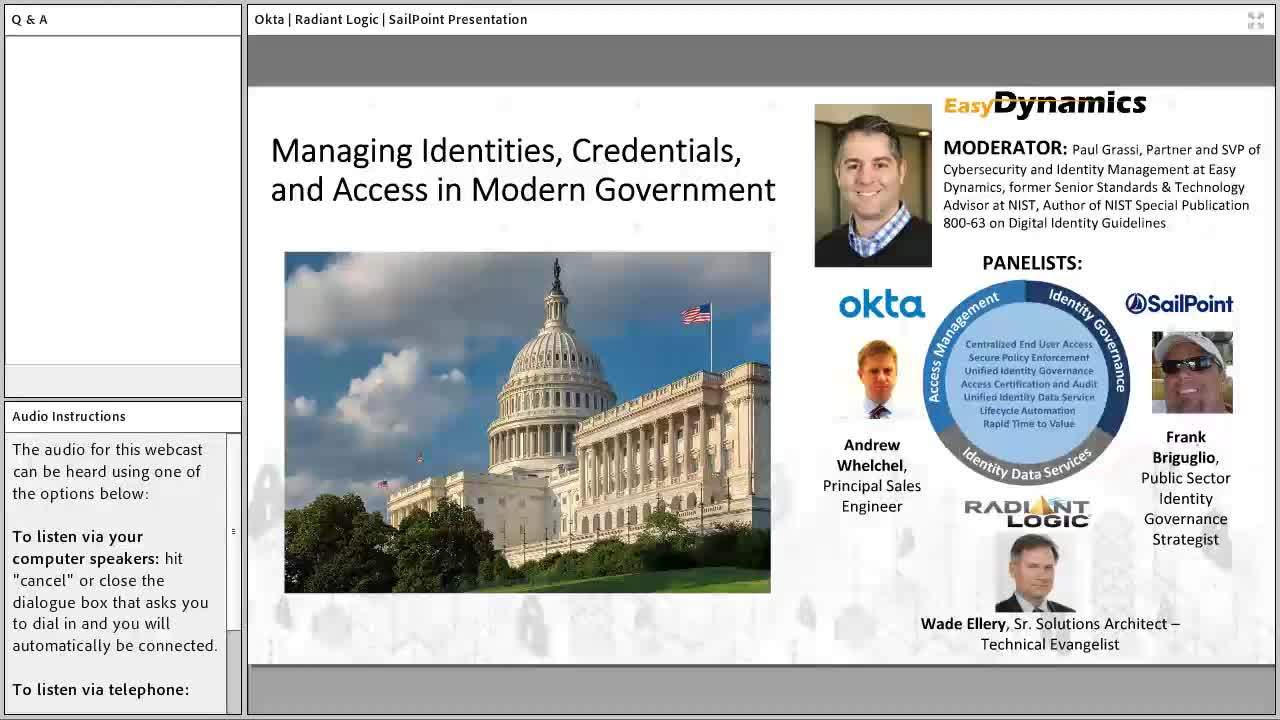
Speaker 1: At this time, I would like to introduce our moderator and speakers for today. Our moderator is Paul Grassi. Paul is a partner and SVP of Cybersecurity and Identity Management at Easy Dynamics, a former senior Standards and Technology Advisor at NIST, and author of NIST Special Publication 800-63 on digital identity guidelines.
Speaker 1: Our speakers for today will be Andrew Whelchel from Okta, Wade Ellery from Radiant Logic, and Frank Briguglio from SailPoint. Andrew Whelchel is a Principal Solutions Engineer at Okta. He started in information security and IAM after after graduation from the University of Memphis supporting identity and access management. He managed Microsoft identities for US federal customers, transitioned to network infrastructure security, and later to consumer identity protection. His most recent roles are at RSC security and Okta. At Okta focuses on both protecting employee, partner, and citizen consumer identities for US federal customers in order to reduce cyber risk as well as accelerate capabilities for cloud transformation. Andrew’s contributions include work as a contributor on the NIST 1800-3 attribute based access control standard and speaking events on identity access management and security.
Speaker 1: Wade Ellery is a senior solutions architect and technical evangelist at Radiant Logic. He has extensive experience in enterprise IT, direct and channel software, and services, sales, and management. He has in-depth knowledge and experience in enterprise IAM, IEG, risk and compliance, and IT security challenges.
Speaker 1: Finally, Frank Brigug-lio is a public sector identity governance strategist at SailPoint. He is a recognized thought leader and authority in identity governance and administration and authentication and access control. Throughout his 22 year career he has been involved in the design and implementation of identity related technologies and the development of identity standards. He has supported the federal, identity, credential, and access management program, FICAM, as subject matter expert, and was involved in the development of the FICAM roadmap, the federal and DoD public key infrastructure, and the federated identity authentication standards.
Speaker 1: Guys, thank you so much for being with us today. The floor is all yours.
Wade Ellery: Looks like we lost Paul for a moment there. So, this is Wade Ellery, Radiant Logic. Let me take a second here just to give you an overview of what we’re talking about today and how we’re offering a best of breed solution by combining the functional areas of Okta’s access management, SailPoint’s identity governance administration, and Radiant Logic’s identity services platforms in order to give you a complete solution that addresses access management, identity governance, and identity data services throughout the government infrastructure.
Wade Ellery: The content today will be focused around the FICAM and ICAM initiatives and the ability for us to show you, in a single solution set built through these three products, how you can meet all the requirements that you’ll be facing in meeting the government’s new move towards a more secure and more diversified identity infrastructure.
Wade Ellery: The key here is the combination of best of breed.
Paul Grassi: Thanks, Wade.
Wade Ellery: ... Oh, go ahead Paul.
Paul Grassi: I was going to say, go ahead and take that and I’ll introduce the memo and the rest of the slides. I’m sorry about that. I un-clicked mute and it hung up on me.
Wade Ellery: Oh, that’s all right. The key piece here is the best of breed scenario that allows, especially organizations within the federal space, to meet the requirements of identity management across access management, compliance governance, and access to identity resources through a combination of three of the leading products in that space. And as these three vendors will explain today, we built a cohesive model that addresses all the requirements against a seamless integration and codefree model for deploying the solution, secure access to data and applications, high availability, high scalability, which is required in the government space, and the ability to reach globally and act locally, which is critical when you’re defining your security model to be able to operate outside of the original legacy perimeters that we’ve all had to work with. And basically helping to take ICAM into the modern world while still honoring your legacy implementation.
Wade Ellery: So, this best of breed model allows a agency or a department to, with a partnership created between Okta, SailPoint, and Radiant, solve this whole challenge as a holistic solution that is well integrated, works well together, and is able to address everything that is a challenge within this particular integration to deliver a level of security, access, and governance that is now required within the federal space.
Wade Ellery: Paul, I’ll go ahead and turn it back over to you and let you carry it from here.
Paul Grassi: Right. Thank you, and thanks for jumping in there. As I was talking to myself I was saying that really excited to have these three speakers here representing Okta, SailPoint, and Radiant Logic. From my perspective as an independent, they really are a best of breed solution suite in the holistic FICAM space. And really what we wanted this discussion to do is to center around the memo that just came out a month or so ago out of the office of management and budget, which is basically a renewed and modernized, all-encompassing memo related to digital identity in the government space. It fortifies some of the really, really good stuff that’s been happening in the federal government, and it also brings the best of the private sector into the mix to enhance and modernize government solutions.
Paul Grassi: We’re going to talk about each section of the memo, so I won’t get into that in detail. Our presentation is aligned around that. What I wanted to talk about is kind of give you my perspective on this memo. There’s some stuff that stuck out that’s obvious, and there’s also some subtext that if you read carefully and you analyze a little bit you may find some interesting perspectives. The obvious is the enforcement of 800- 63, the canning of the LOA model. Memo 404, which was the quintessential memo around identity has now been rescinded, and their OMB is doubling down on risk management around identity.
Paul Grassi: And that really drives one primary thing that the memo does really, really well, which is it’s agencies “Hey, these are guidelines that you should follow, but you know your mission. You know your risk. You know things that NIST may not have had access to when they wrote this, or the private sector didn’t have access when they were commenting on this. So, go ahead and test systems. Test solutions. Determine other processes that may meet this and share it with the community at large.” So, hopefully agencies will take advantage of that and not try to strictly follow 63 by the letter. It’s a good set of guidance. It gives a good baseline, but by no means is it meant to be the only way to do things.
Paul Grassi: From the HSPD-12 perspective it’s certainly supportive of the PIV card. It continues to state that that PIV card is the primary credential that federal agencies will issue, but it’s broadening the aperture around what is compliant with HSPD-12. There’s a focus on federation. The idea that you could take your PIV card and take it from one agency to another agency and use it on a computer no longer is really a valid use case given everything being web-based. So, let’s federate. Let’s use the card to issue assertions off of not try to get everything to support it.
Paul Grassi: Same with Drive credentials. It doesn’t necessarily have to be all PKI if you are... FIDO, for example, could be a really good Drive credential given this memo and what 800-63 says. And finally, because there’s so much to unpack here, it’s focusing on attributes rather than on credentials. Pretty soon we’ll just be carrying a credential on our phone. There’s no need for agencies to issue those anymore. So, the idea of bring your own authenticator comes out loud and clear in this memo.
Paul Grassi: Okay, so, moving on. For the first slide I’d like to give it to Andrew to talk about Okta’s perspective on this section of the memo.
Andrew Welchel: Thank you, Paul. So, this first part is about the contextualization of identity. And really this is much about looking at the different kinds of context that identity needs to cater to and address. The big scenarios we look at many times that you have to address are modern workforce and also customer identity use cases. And this perspective, federal organizations really need to enable, through modernization of their IT to protect both against security breaches, flexibility, visibility, and security for influencing contractors, and also build secure, seamless user experiences for customer portals and also supplier portals on that end.
Andrew Welchel: What’s really different and there has been some change. The first thing that’s changed and is really different about federal organizations is many times they really have to solve both of these problems. There’s some of the commercial world that only are going to have to solve one. But we’re finding a bigger trend where federal organizations really have to solve both of those. There’s a second trend that we’re observing too, that the government agencies also find that they’re getting both the directive and a motivation just for the new modernization to actually use cloud-based services. So, in this case identity is a service, which Okta is an example of, and also seeking out services for that. So, certainly as you do all those you have to do it securely and keep up with all the controls that were discussed earlier.
Andrew Welchel: Thank you, Paul.
Paul Grassi: Sure. How about kicking it over to Frank? Because we luckily got to hear Wade at the beginning, so we’ll share some air time. Frank, thoughts?
Frank Briguglio: Yeah, thank you. I’ve kind of looked at the contextualizing in a little different factor. When we look at managing the identity we have to look at all the personas and relationships that identity has to an agency. And you’re going to hear me repeat a lot of the same things in a lot of my responses today, is it all boils down to how we’re doing that.
Frank Briguglio: As you mentioned, the PIV card or the CAC card is the current form factor, and we’re going to base other factors off of that. But really we’re talking about a single heartbeat. So, the modernization that the agencies need to go through as we go through this digital transformation is keeping those principles in mind of how we’re managing the identity, not the authenticator or the authorization. And when we look at the access that’s being granted, how is it being granted? Is it being automated? Is it being audited? And that’s where this solution, this best of breed solution, brings to the table. Very easily on the front end can determine, by the authenticator you’re using, what type of role you may have once you’re inside the wall. But how did you get that access, right? And what entitlements do you have?
Frank Briguglio: So, I think it’s just key that the agencies that continue to move forward with their ICAM initiatives build with a modern IGA solution that they have. And it’s connected everywhere: cloud; on-prem; connected to everything, whether it’s a stash or a business app; devices; data. We’re looking at that context as a whole. So, I’m going to turn it back over to Wade and he can expand on that. I think he’s going to add to what I’m saying about connected everywhere, connected to everything, and centralization. Wade, go ahead.
Wade Ellery: Thank you Frank, and that’s exactly right. The key, from Radiant Logic’s perspective and the reason the three of our products work so well together, is that we can act as that aggregation point, that ability to quickly connect to all the places for identity information exists. Because the richer contextualization that you can create comes from having a really rich profile of identity information.
Wade Ellery: And just as Frank said, being able to understand what access someone has, what they should be able to do with that access, and being able to manage that within the perimeters of an organization, or when they’re outside that organization, or when they’re up on the cloud, all that has to do with context, with understanding the user, his role, and the environment he’s operating in and being able to apply policies against that.
Wade Ellery: And the underlying foundation of that is feeding all that identity data up into the applications like Okta and SailPoint that consume that in exactly the format, the protocol, and the structure they need it, while aggregating it from multiple disparate back ends that don’t necessarily easily operate together, or even correlate information easily. And then being able to reuse that effort over and over again and broaden this out so as you move outside of your organization, we’ll talk more as we go along about the ability to work cross-domain, that broadening of access and your context is dependent on being able to pull more information in and make that information valuable and accessible.
Wade Ellery: So, contextualization, for us, is really important component because it relies on good quality information without disrupting back end systems, or legacy systems, still operating, but being able to modernize, basically painting the cars you’re driving down the road while you’re increasing the value of the information being fed up to your access management and compliance layers.
Wade Ellery: Frank? I’m sorry, Paul?
Paul Grassi: Great. So, moving on to the next slide. This section of the memo really kind of tees up identity as kind of a first class citizen, not only in cyber security but also in mission, which, other than HSPD-12 and having the card, wasn’t really explicitly stated in government. The more traditional cyber security disciplines were more important, and now we’re seeing a rise in identity and almost really a focus on identity as the center point of all things related to cyber.
Paul Grassi: This also tees up what you may have heard as zero trust. I’ve joked that zero trust is just a way for the identity market to rebrand itself and be relevant. This really is a discipline that is valuable in the marketplace, especially with cloud and mobility is something that the government is eager to move forward on.
Paul Grassi: So, with that, Andrew, what are your thoughts?
Andrew Welchel: Yes, Paul. Thank you. When we look at the managing identities, credentials, and access on the modern government side, one big thing that continues to resonate and what we see and also we’re seeing agencies speak to us about is just the fact that identities really needs to be its own modern, independent platform that allows organizations to choose the solutions that are best for them. And really on the commerce needs to move away from identity being in each applications as much as it kind of used to be in the past.
Andrew Welchel: If we go back to the OMB ICAM policy that we kind of discussed earlier, that really is much rooted in the realization that this change is happening throughout the federal government, and really we need to modernize this IT to support these evolving technology needs and uses, while obviously keeping security itself a top priority. But in order to do this, the path of success, what we’re seeing, is really based on the cloud-based identity platform. Because that, really, is going to be the part that will give the speed and agility to do this and provide a simple, secure access point for all the applications that are getting managed by this ICAM for both traditional applications, cloud-based services, and also mobile and desktop applications.
Paul Grassi: Thank you.
Andrew Welchel: Give it back to you.
Paul Grassi: Frank. You’re up.
Frank Briguglio: Oh, hey. So, yeah. This really goes back to the framework of what ICAM is. And it’s the processes of, what we call at SailPoint, joiner, mover, leaver. We have employees, contractors joining me at organization. They move around the organization. They leave the organization. They come back. ICAM is fundamental to ensuring not only our security controls and objectives, but also our compliance objectives.
Frank Briguglio: And this really gives, from a SailPoint perspective, I talked to a lot of customers, and what we really try and do is get them to think about... because they come to us, “Do you do access management?” And we say, “Well, no. That’s our partner like Okta.” And they say, “Okay, well, maybe we want to talk to them.” And then we ask what the real problems are, and it’s usually provisioning, efficiency in provisioning, de provisioning orphaned accounts, and all of these things have led to cyber breaches. They’ve led to data leaks because that’s leaving overexposed accounts around that get attacked.
Frank Briguglio: So, the process of ICAM needs to be governed. And I think you said it, Paul. Giving the identity market this resurgence or rebranding ourselves, it’s also giving the agencies a little poke to bring their FICAM offices back to where they were when they were implementing the HSPD-12 solution. And that’s going to allow the agencies to have the program governments and include the identity in decisions how to move to the cloud, in how to meet compliance objectives, how to meet security frameworks.
Frank Briguglio: So, that makes me really excited that we’ve had this resurgence, and the SailPoint platform, really, we’re managing privileged accounts, non privileged accounts, any type of users, bots, service accounts. The agencies haven’t had this control in their hands, and I’m speaking to the implementations that they got in CBM. Now, DoD didn’t participate. They’re looking at that CBM model very closely now because the agencies how have identity data and context to do access control roles and make some easy provisioning decisions based on just attributes that we have already gathered in an identity profile.
Frank Briguglio: Wade, your take on this?
Wade Ellery: Yeah, I agree completely. And I think that the key here with managing identities, and it all feeds up into credentials and access management, goes back to actually the identities themselves and the attributes that define those identities. As Paul mentioned earlier, the move and the focus is getting farther away from simple authentication and more to authorization. And the idea of zero trust says that “I’m not going to grant you access to the whole store just because you’re in the front door. I’m going to authorize you at each stage in the process to make sure that you’re getting the access that you should have and not getting access you shouldn’t.”
Wade Ellery: And key to that is being able to pull enough information, contextual information, about that user in real time together in a way that decisions can be made, risk can be assessed in real time. This can’t be a report that’s run overnight, it has to be a real time authentication authorization process because the customers and the government employees and the end users and just basically infrastructure now has gotten to expect Google speed and an Amazon experience. It should be fast, it should be rich, it should be complete.
Wade Ellery: So, with Radiant we’re able to pull all that disparate information together without disrupting the existing system. It’s not a rip and replace model where you have to disrupt all the legacy platforms and transform everything. It’s take everything you have and make it faster, make it more efficient, make it better, and serve that information up to Okta. Serve it up to SailPoint quickly and easily in exactly the format and the structure they need it, and make that information available in real time.
Wade Ellery: So, now this idea of identity management becomes a more real time event that can be more responsive to needs. And because you can do this cross-domain, because you can move outside of the physical perimeter of one department or one agency and start to build a trusted identity exchange as DHS has done, I can now bridge these disparate worlds. I can break down these siloed walls that I’ve had before and offer a much more holistic view, but then layer in the compliance and the governance from SailPoint to make sure that people stay in their lane, that just because you have a broader set of information and more range to go, you don’t get into things you shouldn’t get into and audit and deliver that.
Wade Ellery: And then Okta can deliver that access layer user interface where the rubber meets the road to verify that all access is simple and seamless. This all is sort of a synergistic model here where very rich sets of identity information get leveraged in very powerful ways for the end user experience, which is this seamless I get everything I need. I’m not adding more risk to my profile, and I’m audited, and I’m compliant, and it doesn’t appear to me to be a bigger burden than it is today.
Wade Ellery: If we can deliver that we can make a major shift in the way in the way the modern government can operate.
Paul Grassi: Great. As you move through the memo and you look at this HSPD-12 section, section 3, at a glance it’s probably underwhelming. But if you really dig into this section there’s actually some cool things going on. They’re encouraging innovation. They’re encouraging agencies to go beyond just the traditional PKI based approach that the card and the Drive credentials have traditionally been focused on. Not that PKI is a bad thing, it’s obviously very, very good. But there are new as secure, if not more secure, techniques out there that agencies should be able to consider.
Paul Grassi: So, this section is pretty much saying to do that, and then, as I said earlier, share. Share what you’re doing because, likely, if it’s benefiting you it could have benefits to the rest of the government. And then the other thing here is the PIV card has done a wonderful job at what it was supposed to do, but it wasn’t meant to be all things to everyone. It’s kind of been, in the early days, was the authenticator, it was the federation protocol, and it was the attribute provider. It does one of those things really, really, well, which is authentication. The other two, as we’ve seen, not so well.
Paul Grassi: So, OMB is saying, “Let’s get into a federated, interoperable model that has nothing to do with the card. Detach yourself from the form factor, and federate the share identity rather than just accept, flat out, PKI.” So, with that I’ll turn it over to Andrew for his thoughts.
Andrew Welchel: Thank you, Paul. A great lead-in and this is definitely a section, from an Okta perspective, we’re definitely excited about both of the reasons you mentioned from the standpoint of expanding the understanding of what factors should and could mean, but also expanding the ways in which you can use it. And that’s kind of what I think of when we lead-in to this particular space in that there have definitely been some advances in technology that bring some new challenges, and even as OMB memo has, we’ve got new policies and regulations that have been added to meet even other industry standards at the same time, really with an end goal to provide customers and employees with the safest secure solutions.
Andrew Welchel: So, to this effect, what we’re seeing very much is the challenge of not just applying HSPD-12 as, I can even mention a second ago, about just to the desktop. And credit to the federal agencies that most have actually done a good job of getting that part complete, but actually bringing HSPD-12 to all on-premise applications as well as cloud use cases. So, that can certainly be a challenge in many cases.
Andrew Welchel: So, really the opportunity is now available to take a service, a cloud service for identity, Okta is an example, to really take an identity as a service and take one that can do enforcement for an HSPD-12, and run the mechanism to take that, really federate them, to all applications so that you really get the benefit of both worlds in that, “A”, you’re using a more secure mechanism, and “B”, you’re able to really take that to any app as well, across the board.
Andrew Welchel: So, some thoughts there. Thank you, Paul.
Paul Grassi: Sure. Let’s mix it up. Let’s mix it up. I was thinking maybe Wade, you can jump in here and give us your thoughts.
Wade Ellery: Oh, yeah, definitely. And I think there’s a hand and glove model here. For a long time in the industry we’ve focused on authentication. How do I verify the user is who he says he is? Because that’s the critical first step in the process, and I think HSPD12 does a good job of trying to define some common platforms, some common standards, some levels of assurance to make sure that we are authenticating people properly, we’re not just sort of saying close enough.
Wade Ellery: But, again, now the understanding is that this has to work outside of just the physical single building that someone goes to work in. We have models, now, with an interaction and collaboration where I have to be able to take who I am someplace else and be able to verify my identity in another system and in another platform. So, I have to have this cohesive model that lets me move cross domains, multiple departments, multiple divisions within organizations to bring my credentials with me.
Wade Ellery: But that’s only the half of the problem, because the challenge is not just who are you, but now that I know who you are, how can I access a rich set of identity information about you to make valid decisions about what you have access to? I may have certain rights to do certain things in one organization, and a subset of rights that I should be able to exercise in another organization. I’m the same person, but my context has changed. So, I have to link those two together. I have to be able to take my authentication model and extend it, now, with more of an attribute based authorization model.
Wade Ellery: And this becomes critical, as Frank has pointed out with SailPoint, you need to be able to onboard those users, build that rich profile, get them into the right systems. We’re working to extract identity information out of the endpoint applications and centralize that so it’s more easily available and shared across organizations and across domains. But at the same time you have to audit that information to make sure it’s accurate. Because now it’s not just who are you, but what are you doing, what do I know about you, what about what I know about you changed by the context that you’re in, and how am I using that to authorize you to access things.
Wade Ellery: And this becomes critical, especially in things like natural disasters where DHS ends up responding with FEMA and sending resources outside of the agency boundaries. Those people have to be not only authenticated that they are who they say they are, but then, quickly, FEMA has to be able to understand what is that person authorized to do. Can they really fly helicopters, or are they just thinking this is a lark and maybe I can get a good helicopter ride? I have to understand everything about that user, and that comes from extending that authentication with authorization with a rich set of data.
Wade Ellery: That’s where Radiant Logic come into play is making that ubiquitously available so that the authorization authentication and auditing applications can verify that information and provide it at the right time at the right place to get the right result. Frank?
Frank Briguglio: Yeah. No, that was perfect, Wade. And I’m just going to throw a couple comments in here. When I look at, from a SailPoint perspective, when I look at HSPD-12, it’s just another credential or an account that I’m adding to your identity profile. And as you said, I’m using that, contextually, in access policy decisions. I’m using that in audit any account or credential that I might have. A user may have an RSA token. They may have a PIV card. They have access associated with those because it’s really not the identity. The heartbeat is represented differently based on the token.
Frank Briguglio: So, it’s very important that that information is included in those contextual based decisions. I’m just going to leave it at that and we can move on and maybe touch something a little bit.
Paul Grassi: Great. I appreciate it. So, don’t let the title mislead you. No good policy would not have a compliance section and a governance section and this is really what this operating model is all about. It codifies the roles across the organization that have an interest in identity to include human resources, to include physical security leaders, and brings those together under one umbrella in terms of a governance structure per agency.
Paul Grassi: It also codifies what I was saying at the beginning, which is if you need to vary from 800-63 because you have a good reason to do so, then by all means do it, but document it and share it. Don’t share it because people are going to judge or people are going to critique. Share it because you might be doing something that others should be doing as well. There’s something called a digital identity, I think, acceptance statement that we wrote into 800-63 that’s an example of where this stuff can be documented. The intent, when we wrote it, was let’s get agency feedback so we can update these guidelines more frequently and learn about agencies, rather than kind of sit over top and be draconian about what they can and can’t do. And OMB is basically saying that “approach” we’re in favor of and go ahead and vary if you have to and just share across the board.
Paul Grassi: And then, at the same time, there’s a backstop here. We never wanted the wild, wild west, and the smart card and the Drive PIV specs kind of put a nice little box around what was possible to keep that wild, wild west from occurring. With all these new options available, that wild, wild west issue could occur. So, instead of just letting agencies do their own thing all the time, there’s still a compliance part where, I think, GSA and NIST are being asked to evaluate these technologies against open standards and NIST standards and FIPS and all those good things. So, while we’re using multiple options, we’re not using bad ones.
Paul Grassi: So, with that let’s go with Wade to kick this one off.
Wade Ellery: Okay. Thank you, Paul. And for us, looking at shifting the operation level beyond the perimeter, I kind of want to do a nested doll kind of model here. Because the first perimeter we run into in most organizations is an application layer, a siloed application that has its own set of users and has everything locked inside it, and it operated in an island type of mentality. And that was not the fault of anyone, it’s just the way the industry and the implementation of applications sort of grew up over time. No one thought, originally when these things were built 20 years ago, that the were going to have to share information all across a more ubiquitous environment.
Wade Ellery: So, that’s the key is being able to break down those silos, break down those perimeters, and be able to share the information uniformly and ubiquitously across the organization. But not only within the organization, the perimeter, now, becomes cross-department, cross-organization, cross-function. And as we get farther out in the DoD model, we’re talking about cross-nation and working with partners and securing a more effective fighting force by being able to build a richer set of collaboration with other nations. And as we talk about this structural model, the move, now, from onpremise applications into the cloud and this whole variation in expansion of the way information is stored and how it’s accessed and where it’s updated from and what the sources of truth are. This creates a whole new ecosystem.
Wade Ellery: So, from Radiant Logic’s standpoint, we look at this as a very broad model but a very uniform one in the sense that, from our perspective, information stored in any location that we can access is just another data point. It doesn’t really matter if it’s in your organization, it’s in a partner organization, it’s in a database that is maintained outside your organization or is sitting in the cloud. We can connect to it. We can bring that information in. We can add uniformity to that data. We can normalize that data set so that it’s usable by everybody that needs to consume it in exactly the schema, the format, and the protocol they’re looking for. And then we make that ubiquitously available, whether it needs to be consumed off a cloud application, whether it needs to be consumed internally, whether it needs to be shared, whether it needs to be deployed in a subset of data for a particular purpose.
Wade Ellery: It’s that ability to understand that these barriers that we thought were real before are actually no longer effective and no longer required, we can operate, now, openly. But with that comes more responsibility. As you get more functionality you need to add in more security, so you need to be able to see across this whole external perimeter model, understand where your information is, what’s happening to it, and be able to pull that back in to a centralized auditable space that a product like SailPoint can come in now and say, “I can not only see your identity and active directory and in the security database and inside your local HR application, but I can see your identity as it’s being used outside with a partner. I can see your identity up in the cloud application. I can pull all those data points together and make a more uniform and more holistic evaluation of risk, of authorization, of everything you need to be able to handle that model.”
Wade Ellery: So, going outside the perimeter requires more infrastructure, but it delivers so many more benefits if you can make that shift outside to pull in more data and make it more a richer experience for the user and a more valued risk model.
Paul Grassi: Great. Frank. Thought?
Frank Briguglio: Yeah, absolutely. Wade, thanks for stealing my thunder, man.
Frank Briguglio: At SailPoint we’ve had this concept for several years now, identity is the new perimeter, identity at the center. And what Wade talked about was exactly that. It’s centralizing the identity. Whether you’re virtualizing it to create a virtual identity profile, or we’re building that identity profile and all the accounts and entitlements, policy violations, that you may already have against you. We’re assessing your risk in the applications that you already have access to. So, we’re building that profile. It’s so much more important, now, that we’re going outside the perimeter, and not only for security reasons but for cost reasons. We’re providing a platform to do the access certifications that are required not only by security policy and compliance policy to determine who has access. How’d they get that access? Who approved it? Is it still suitable? Is it still required?
Frank Briguglio: So, the identity, as we have this explosion to the cloud and bring on mission partners and we want to do this federation, we still need to look very closely at the account or at the identity that has the access to make sure we’re not leaving exposed accounts behind, and we’re not leaving orphaned accounts that can just be picked up and stolen. And whether or not we’re leaving residual assertion live or whatever it might be, we have to be centralizing the governance processes. And I think that’s what’s key here is putting those processes, that risk evaluation, the policy models, all the things that we do on our compliance manager, is critical.
Frank Briguglio: And now as we look at outliers through our AI tools. We’re looking at peer group analysis. It becomes so critical to have all these key functions in place to really move beyond that perimeter.
Paul Grassi: Thanks, Frank. Andrew, what do you think?
Andrew Welchel: Yeah. Great lead-in Paul, definitely. And Wade and Frank. And this is an area we’re definitely super excited, not just to talk about, but also that it was in the OMB memo itself, and definitely think it was important to have it in there for kind of going into the future. And to Paul, for your point, that shifting operating model beyond the perimeter. You had a really great point about that fact that you’re really talking about people and groups, and more types of groups are using these access and these resources.
Andrew Welchel: And the other thing we kind of observe from the access management is we’re seeing these accesses occur from more locations than before. So, it certainly has an opportunity, as Frank mentioned, to lower costs when you can do that, but the effect of this is it’s definitely dissolved the traditional perimeter. You think about traditional infrastructure, firewalls, routers, switches. Those things many have, in many ways, they haven’t gone away, but people are now everywhere, so you have to have a way to secure people wherever they are.
Andrew Welchel: So, very much in this world, people and their identities, as I kind of mentioned a little bit before, they are the new perimeter. So, the other way we kind of say this many times is you hear people talk about segmentation and micro segmentation in order to deliver security in a modern way. Really, the new true micro segmentation we’re looking at is people and their identity, much in the way that Frank talked about it, it is that new micro segmentation. So, your person, your attributes, who you are, that really should drive that level of access that you have.
Andrew Welchel: Now, when we flip that around to the operating model, that kind of gets us something that Paul talked about earlier about zero trust. So, there’s a whole lot of talk about zero trust and zero trust security across the industry, but if you look to kind of find what it is in this case, the root idea of that is the idea that regardless of who is attempting to access applications or information, that the system or systems have a way of verifying who that person is regardless of their location, bring in context, bring in that information implied on a contextual based basis at that point of origin. And regardless of where the location is, regardless of the interfaces.
Andrew Welchel: And they key on that is to do it at speed and be agile, and really our thought on this from an access management is that being able to have a cloud identity really enables you to execute on that zero trust and that shifting operating model beyond the perimeter in a way that we haven’t been able to do before. And be able to implement a zero trust strategy itself and securely embrace that rise of the cloud adoption, but moving away from that kind of single traditional perimeter and really evaluating the context in order to get access to applications.
Paul Grassi: Great. And as we close out the session
Andrew Welchel: Thank you.
Paul Grassi: As we close out the presentation and get to your questions it’s fitting that we end with a shift from employees to, actually, citizens, because more and more services and benefits are coming online. We’ve got to be able to deliver these services over a digital channel in a way that’s user friendly and secure. Too often we’ve given up security for usability. I think we’re at a point now where we can get both. So, this is what this section is about.
Paul Grassi: My interpretation of this, I’m sure OMB wasn’t thinking this but this is my take, this is basically saying “Stop thinking you’re special as an agency. There’s no special snowflakes.” The IRS and the SSA and HHS, as just examples, serve fairly similar populations. So, why are they each doing their own thing? If the VA credentialing veterans, why are we asking them to get a credential for some other agency and putting them in a process that provides undue process on their end?
Paul Grassi: So, this section is saying federate, use credentials that exist. This is the one that supports bring your own authenticator. It specifically says “allow individuals to bind non government authenticators to their identity.” So, that’s great. There was a previous section that I was remiss to not speak about that I will. It’s saying, “Hey, government. Open up your data. Identity proofing is important and government, you have a lot of that authoritative data. Start opening it up. So, state department, let us access passport data.”
Paul Grassi: Now, laws may have to change to get this to be fulfilled, but at least OMB is making that statement. And, finally, on that vein of stop thinking you’re a snowflake, don’t think for your users. Actually reach out, touch them, solicit them, and get direct feedback to figure out what it is that they actually want before you give them something you think they want. I think that’s very important guidance for federal agencies, especially when budgets are always tight.
Paul Grassi: So, let’s go back to our original order and have Andrew lead us off.
Andrew Welchel: Sure, thank you for that, Paul. So, in the slew of the improving of digital interactions, one of the key, interesting observations is that we’re very much still struggling with technology that has been in place for many years. The new challenges will come at us, there’s new challenges of technology coming at us from the outside, but many times we’re still dealing with technology solutions that have been there for many years.
Andrew Welchel: So, in this case, one of the kind of observations is just the fact that similar modernization needs to be seen in the government agencies for the external, really to bring that digital interaction, optimize it for the public for ease of use and high security. And, really, if done right, this really does have the opportunity to provide us solutions, and they provide a more enlightened, empowered use for all the citizens, and certainly do it in a secure way. And really everyone benefits in the end on that.
Andrew Welchel: Thank you, Paul.
Paul Grassi: Thank you. Frank, you’re up.
Frank Briguglio: Thanks. When I think of this my head kind of explodes. You can think of all the context that you, as a US citizen, interacts with the government. You can be a government employee. I’m a military veteran. My son is on active duty. We’re all tax payers. You have farmers that also could work somewhere under USVA, or some other agency needs to interact with USVA that may also have to file forms with the IRS. So, the American public interacts with the government in so many ways for our benefits when we retire. There’s just so many.
Frank Briguglio: We need to take all of this into consideration to ease this pain of the citizen in how they interact with government systems. It’s going to take some time. It’s going to take some change, as you said, in legislation and how we free up some of that data. But I think it’s possible, and it will be a challenge to maintain it. But I feel that technology and what we’re talking about today and how to federate,how to manage profiles, how to use access, how to grant access, how to keep systems in compliance within security controls, keep everyone secure. I think it’s achievable. Back to you.
Paul Grassi: Thanks. Wade.
Wade Ellery: Thank you Frank. I think what you’re-
Wade Ellery: Yeah, by all means. Thank you. I think what you pointed out earlier was critical that the amount of interaction with the public that the government agencies have, and, as you pointed out, there is such a overlap of identity information, overlap of models. And this is really sort of a reflection of what we’re seeing in the commercial space, also. And there’s some really good lessons learned there in terms of what the end user is expected, or what frustrates them when they start interacting digitally with a organization.
Wade Ellery: It starts out simply with registration. I shouldn’t have to enter information more than once into a organization that should already know about. And unfortunately for a lot of the departments within the federal government, the citizen may assume that they should all be talking to each other already. So, as you mentioned, if I’m already in the IRS database for certain information, shouldn’t my FDA farm loan people have access to that same data?
Wade Ellery: So, you need to be able to build a model where that information is asked for once, is input once, and then a trusted identity exchange, a model for interchanging that information between organizations. But you can’t simply throw open the doors and let everyone have access to everything. As you pointed out earlier, passport data could be essential for a certain organization to be able to see, but information that’s far too personal for someone else to be able to access in another purpose. You have to be able to add controls on top of that information, and then deliver it to each consuming agency in the format, in the structure, in the protocol that they’re looking for so that they can get that information and consume it quickly. And you minimize the amount of integration overhead.
Wade Ellery: And that’s where Radiant Logic plays in is that ability to build a ubiquitous identity exchange context and infrastructure so you can move data around and not ask people to register and re register and re enter information in multiple different agencies, but leverage that data for a rich profile.
Wade Ellery: And then tying that back to the authentication, you should be able to authenticate once to the federal government and then go anywhere you need to go in an ideal world. And again, as Frank mentioned, there’s a lot of growth and a lot of expansion that has to take place for this to happen, but the goal should always be to try and make things as ubiquitous as possible to let the user’s experience be driven by the user’s information and their context. Where they have interactions with the government, their credentials should work, and even bringing their own credentials in certain scenarios when those are proven to be secure.
Wade Ellery: And then authorizing that person, making sure that you have enough rich information about that public persona to be able to let them gain access to the right information, let them do the functions they need to do. There’s nothing more frustrating than getting into a system and running into roadblocks in a poorly designed or an incomplete digital experience, and having no one to talk to and no idea where to go next. It’s much more stifling than sitting across a table with someone and sorting something out.
Wade Ellery: So, the system has to be rich and complete in its data. And then it has to understand context. It has to understand hey, if you’re coming to the IRS you’re talking about taxes. If you’re coming to the state department you may be looking for a visa. You shouldn’t have to necessarily define what you need from a global list when you’re already within the context of a certain agency. So, being able to tie that identity back to the purpose of the interaction, but use that rich identity infrastructure.
Wade Ellery: And that all goes back to correlating data for multiple places, making it ubiquitously available, giving it out in a profile and in a format that everything needs to be consumed in. And in that way you can deliver that experience and start building that going forward. And that’s where Radiant Logic lays that foundation, so now all the compliance and governance and role management and proper provisioning of endpoint applications through SailPoint can be done based on that rich set of data. And as that data gets enhanced the world just gets larger as that can be fed in at the bottom with Radiant. And then make it available to Okta so you have the authentication authorization experience for the end user is much more seamless and much more ubiquitous across the agencies.
Wade Ellery: So, that’s a great goal to head towards and it’s great to see that’s been called out, because I think one of the ideas is that we assume the federal government is a service that we consume, and the more that can be made digital and a positive experience, the better it is for everybody on both sides.
Wade Ellery: Paul, I’ll turn it back to you.
Paul Grassi: Great. Thank you. We got a couple minutes left. There’s three questions that came into the queue. If there’s any more please submit them. We’ll try to get to them, if not here afterwards in some way, shape, or form. One of the questions is kind of targeted at two of our speakers, so I’ll go with that one first, which is, “What about this solution stack requires... Wait a minute, I lost the question. Sorry. I think the question was something like, “What does Radiant Logic bring to the party that SailPoint can’t already do?” And I think, Wade, you certainly have an opinion there, and I think, Frank, you have some complimentary compliments to that as well. So, Wade, answer?
Wade Ellery: Yeah, definitely. And what we really want to make the point here is up front that this is a best of breed solution, because there are functions that each of us do really, really well. And to operate in the real world there’s functions that each of us have taken on as a requirement to function, to integrate, to be able to operate that are not necessarily our core value adds.
Wade Ellery: So, from Radiant Logic’s standpoint, we are built and engineered. We’ve been active 18 TM for 20 years to be able to connect to multiple systems of identity information, and even information that’s not necessarily identity centric, and be able to handle multiple different protocols and structures and schemas and back end sources, pull that information together, normalize that data, correlate an identity across multiple systems. So, if I have Paul Kim in one system and Paul K127 in another system, I join those together, but I don’t inadvertently put Paulette Kim together in that profile if either she has a P. Kim as an identifier. So, I can make sure that I have a rich profile that is accurate across all of my systems, and then provide that information, do that heavy lifting once, and provide that data to all the points that need to consume that information.
Wade Ellery: On the SailPoint side, and I’ll let Frank talk more about that piece, though, the focus is really on what you do with that information, the nasty job of laying the concrete and putting down the foundation and putting in the plumbing is what we do, and then let others build the house on top of that, consume that data, and add value to it.
Wade Ellery: And this is where Radiant Logic’s play is most effective is minimizing and simplifying that process and making it repeatable and make that information available in multiple different ways through multiple different endpoints. So, you don’t repeat that heavy lifting more than once.
Frank Briguglio: Yeah, and-
Paul Grassi: Frank, we’re at time. We’re at time, but please. Did we lose Frank? Frank go ahead, we’re just at time.
Frank Briguglio: Okay. I’ll make this real quick. There is a lot of overlap with what Wade just said and what the SailPoint connector framework can do. We’re more on the provisioning side, so think how an account gets in a system, how an identity gets created in the system. It wouldn’t be there for Radiant to virtualize if we didn’t provision it. So, that’s a big part of the difference, and there’s cases where SailPoint and Radiant will be connected to the same application and each other where Radiant is presenting the profile, but we’re provisioning the entitlement deep within that application. And Radiant can be virtualizing the SailPoint database and making, let’s say, the risk core that we determine or the policy violations. We can use those as attributes, things like that that Radiant can then have in the identity profile that then Okta can look at when it’s looking at the interface through Radiant Logic for authentication.
Frank Briguglio: So, that’s where these three solutions really build that best of breed. It’s because we inter operate so well together even though there is overlap. I mean, there’s overlap in all three of these components. And it’s us coming together as industry saying, “Hey, this is what we do best. You do this other part better.” We go in together and we decide who should be doing what. And we don’t squabble over it. So, this is a very different model as we move forward with relationships like this in the industry. Ten 19 TM years ago you wouldn’t have seen three identity vendors doing this together like we do today.
Wade Ellery: Yeah, just to reiterate on the end of that, this is Wade again.
Paul Grassi: Thanks, Frank.
Wade Ellery: To build on what Frank just said, that last piece was critical is that, really, it’s a matter of looking at the environment, looking at the scenario, and designing a solution where each platform does what it does best. And that will vary from use case to use case. But that level of cooperation, that level of integration that we’ve been able to put together, I think, as Frank mentioned, is unique in the industry in the sense that you now have a synergistic model that will solve your problem, and that solution will be optimized for your particular use case because we have a tremendous, broad set of tools, now, to address a lot of different scenarios. So, the sum of the parts is greater than the whole, or the whole is greater than the sum of the parts, however that’s said.
Paul Grassi: Thanks, guys. Well, we’re going to wrap up. I appreciate all the participants for joining us today. We had really great attendance. When we end this there’ll be a poll. If you have time and can stick around please fill that in for us. Thanks to Wade and Frank and Andrew for all your insights. Their contact information is here on this last slide, so is mine. I think we all provided it because we are happy to take thoughts or questions offline, if you wish. And, finally, thanks to Carahsoft for hosting this. We will conclude now and thanks for hanging in there a couple minutes late. Bye Bye.
Government agencies require a higher level of security and user experience than ever before. According to the Office of Management and Budget’s updated policy around Identity, Credentials and Access Management (ICAM), agencies are being encouraged to use more flexible solutions, supporting pilots for new authenticators, and requiring the creation of a dedicated ICAM team.
The answer? A multifaceted approach, involving access, security, governance automation and controls, and federated identity based on virtualization. View this on demand webinar with Okta, SailPoint, and Radiant Logic, where we discuss:
• A modern cloud-based IT architecture that empowers agencies and organizations to increase efficiency in managing the identity lifecycle automation and access for all applications providing contextual access management to cloud and on-premise applications and data and support secure collaboration with partners and vendors beyond the firewall to help agencies meet the objectives of the new guidance provided by OMB.
• Automated access and governance controls, driven by the power of AI, to mitigate the risk of a security breach and enforce compliance and regulations such as the NIST Cybersecurity Framework, along with the most efficient workflow and provisioning necessary.
• A federated identity and directory service based on virtualization to integrate and rationalize identity from across diverse data stores to provide one common, infinitely reusable identity hub to drive all initiatives, from tactical to strategic.
• Our best-in-class identity governance, access management, and virtualization solution is proven to facilitate digital transformation, providing agencies and organizations the convenience of unified access and single sign-on with the needed control of identity governance.
