Your Employee Onboarding & Offboarding Process: Is it Killing Your IT Admins?
With the increased adoption of cloud services, and in order to keep pace with innovation and the requirement for every organization to develop applications, IT is facing some new and complex problems. IT teams today are constantly striving to improve productivity and security for both their own internal processes, but also for end-users, who are essentially their customers. Any IT manager whose organization is looking to modernize is challenged with onboarding new employees, managing the many different identities lifecycles, and overseeing a cumbersome offboarding process that can entail some major security risks. Let’s look at some of those top issues:
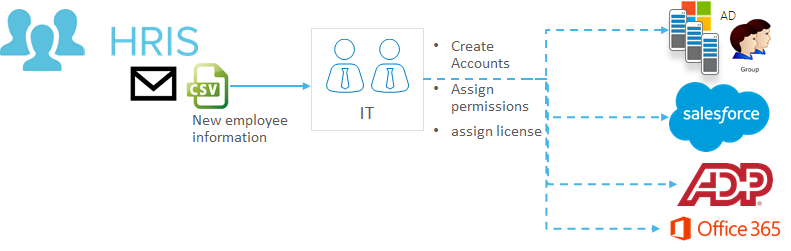
More Employees + More Apps → Overwhelming Account Management
As companies scale they hire more employees and increase their usage of an always growing app catalog to help the business grow. The problem starts when IT is on the receiving end of requests to create accounts, assign permissions and licenses from both HR and frustrated end-user who sit waiting for access for days, and sometimes weeks. Many times, IT hands are tied, since they depend on a business app owner to approve access and create the new employee account, which can of course be frustrating to all parties involved. A recent survey, held by our partner ServiceNow, found that 8 in 10 companies both large and small, still use unstructured manual tools such as email, spreadsheets and even personal visits to drive routine work processes, and fewer than 1 in 10 have automated applications for employee onboarding.
Once onboarded, employees are then tasked with managing all the different accounts and passwords and will often open more IT tickets, because they’ll often forget passwords to the many applications they use to do their job. In an average organization we see around $500K in value of IT and app owners time spent on creating, updating, and removing accounts.
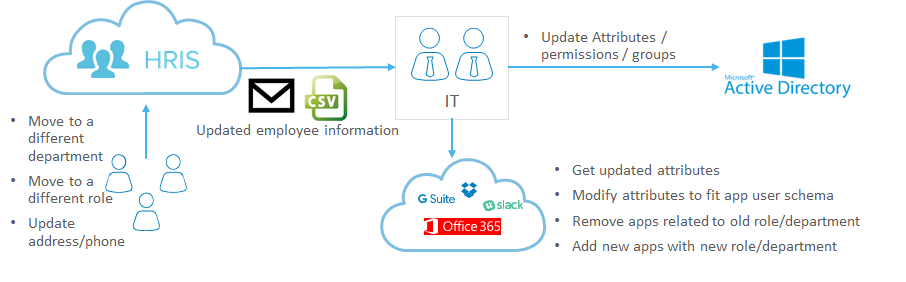
Internal Mobility - Great for Employees, a Productivity Drain for IT
Onboarding employees is just the start, often there’s internal mobility within the company, which opens up not only more work for IT to figure out what accounts to close, and what accounts to open, but also a security risk as they can potentially accumulate too many access rights beyond what their job requires. An average user will spend 300 minutes every year waiting for access.
Change requests can include are not isolated to a new role or department. They include also a new address or a new phone that was assigned. This requires IT to be responsible for the downstream applications update, and also to keep HR informed on employees’ changed personal information. Change requests like the above might sound trivial, but an average organization can spend up to 6,250 hours a year on such tasks.
Fewer Users, More Headaches
While some users move between different departments, today’s modern workforce is characterized with transitioning between companies more a lot more often than in the past. There is a desire to give people access to everything, because IT doesn’t want to create friction for user to do their jobs, but when these employees leave with access to sensitive apps or systems it can create a major security hole.
While a server crashing won’t keep IT up at night these days, forgetting to deactivate all the accounts of employees who left the organization sure will. Even a single account of one employee that was left active for any reason, might create a security loophole. According to a security survey “More than 13% of respondents can still access a previous employer's' systems using their old credentials.”
While HR is tasked with offboarding users and maybe deactivating accounts in payroll or travel systems, it’s too often a few days before anyone tells IT that the employee has been terminated. This is exactly the time, where an employee who was involuntarily terminated may be most motivated to inflict damage however possible. When that happens, the average cost of a data breach in the US is estimated at a staggering $7M. While some organizations can recover or bare the cost, the trust with their customers might be permanently damaged.
Is Automating Processes for Onboarding and Offboarding the Best Solution?
To solve all the issues above, organizations need to integrate all the separate systems that govern the identity lifecycle of a user and automate user access. Starting with connecting the HR system, which is the source of truth for when employees join, leave or move, to all the applications and permissions granted to users in the organization. In many cases this includes an overlay over old systems like Active Directory. An end to end automation of onboarding and offboarding processes can benefit not just the IT department, but also the business and the end-users.
If you’re curious on how this gets done with many of our customers stay tuned for the second part of this blog that will walk through how Okta can help solve all the above problems, and significantly reduce the friction in IT.