The hidden identity crisis powering your AI agents
Why Identity Security Posture Management Is Essential
When machines inherit dangerous permissions
It's 3 a.m., and an AI agent is negotiating between your Salesforce instance, AWS infrastructure, and ServiceNow workflows. The agent operates tirelessly, making thousands of decisions per minute.
But here's what should terrify you: This AI agent isn't using its own credentials. It's borrowing the identity of an application — and that identity might have permissions that could compromise your entire organization.
Welcome to the world of workload app identities, where the promise of autonomous business operations collides with a security reality most organizations aren't prepared for.
The new identity landscape
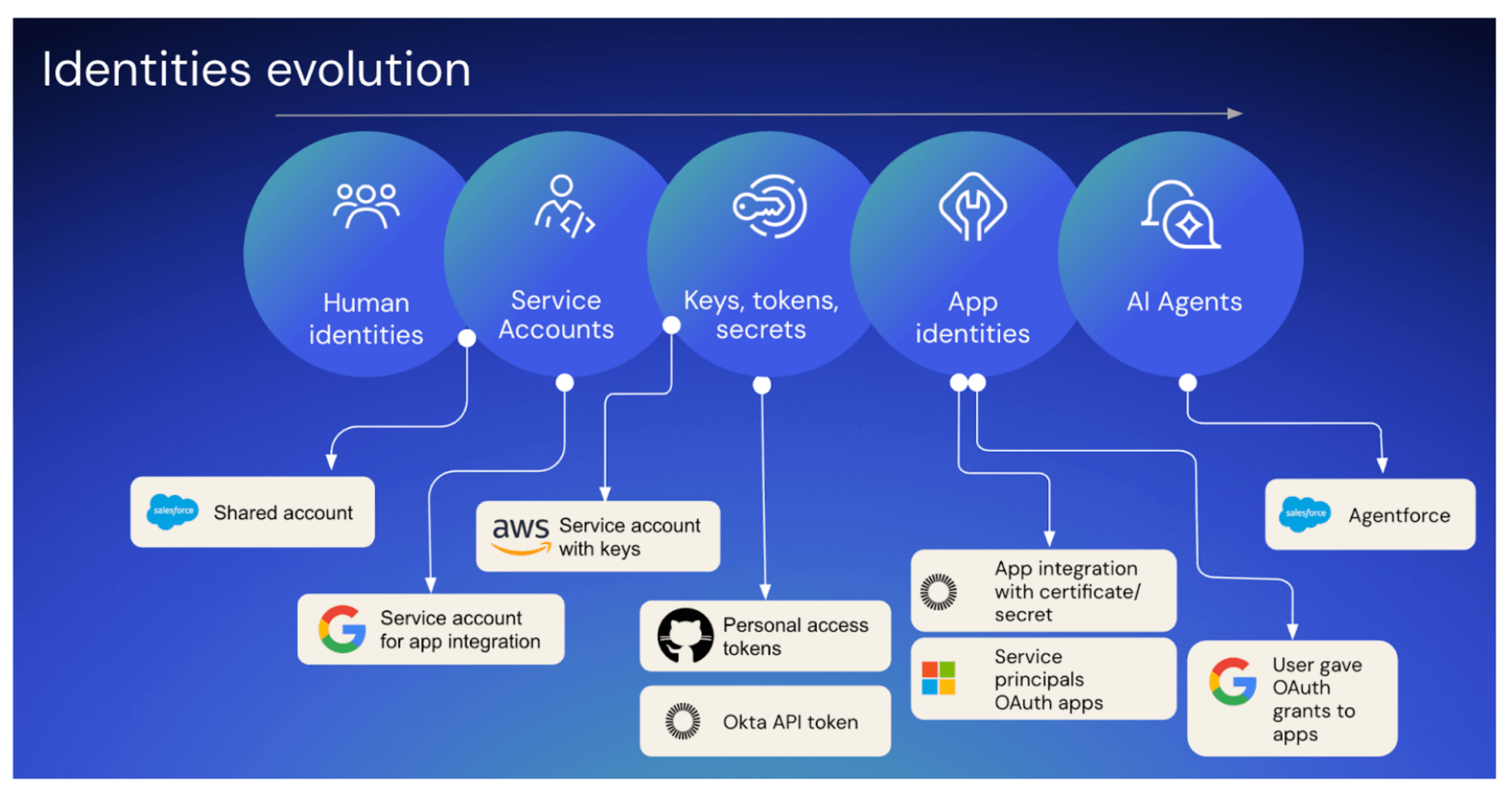
As we explored in our recent blog on the convergence of human and non-human identities (NHIs), organizations have begun addressing traditional service accounts and API keys. Workload identities represent the next evolution in this challenge.
Unlike traditional service accounts that rely on human-born users with static passwords, workload app identities use modern, token-based authentication (usually OAuth or certificates) with fine-grained permissions that are not tied to a human user's lifecycle and are purpose-built for automation. In theory, that makes themperfect for our AI-powered future. In practice? They've become the most overlooked attack surface in your environment.
Modern enterprises run on workload identities, those critical authentication mechanisms that allow applications to connect securely. Examples include:
- Entra ID service principals and registered apps
- Salesforce connected and external apps
- Google custom apps and GCP service accounts
- AWS IAM roles
- Okta Integration Network apps and custom app integrations
- GitHub OAuth apps
- Snowflake OAuth integrations
The AI agent inheritance problem
When AI agents and MCP Servers interact with your applications, they inherit that application's workload identity permissions. The app's identity dictates the maximum scope of what an AI agent can do autonomously.
This creates unprecedented risks:
1. Highly privileged identities: Admin-level access granted during "just make it work" moments becomes a permanent backdoor for attackers — with far less visibility than human breaches.
2. Unused pPrivileges: That OAuth app from a six-month-old POC? Still active, still has privileged production access, still a door any compromised system could walk through.
3. Toxic privileges combinations and segregation of duties:
Individually reasonable permissions become dangerous combinations when inherited by autonomous systems operating at machine speed. Real scenarios keeping security teams awake:
- A GitHub app with read access to private repos AND write access to production. A single identity holds the power to steal valuable IP and directly attack and compromise the live, customer-facing product
- An AWS role with write/delete privileges on dev AND production. A compromise in the less-secure dev environment can then directly impact the critical production environment.
- A Salesforce connected app accessing customer data AND modifying security settings. An attacker who compromises this one identity gets the keys to the kingdom: They can steal data and cover their tracks by disabling audit logs or other security features.
4. Unrotated secrets: Without automated rotation, credentials become permanent. An AI agent could make thousands of API calls with tokens that should have expired months ago.
5. Missing network controls: Workload identities lack IP restrictions, exposing your systems to being accessed from anywhere, making it easier for malicious actors, and you'd never know.
6. Misconfigured trust: Overly broad trust relationships create attack paths that machines can exploit faster than humans can detect.
The Okta Identity Security Posture Management advantage
Okta ISPM provides the foundation for securing the entire identity perimeter, including human, non-human, and agentic identities as they become more prevalent across your technology stack. Whether it's a Salesforce admin service account with a password, a GitHub OAuth app, an AWS IAM user with an API key, or an Okta Admin with a token, Identity Security Posture Management gives you the visibility and control to manage these powerful permissions before they’re exploited.
Cover your most critical apps — including IdPs, SaaS, and Cloud infrastructure: Unlike tools focused on infrastructure or individual applications, Okta Identity Security Posture Management provides comprehensive discovery and management across your identity landscape.
Cover the most critical NHI types: Okta Identity Security Posture Management supports a wide range of NHIs, from legacy service accounts, through API keys and tokens, to modern OAuth apps and Salesforce AI Agents.
Work on scale: Okta Identity Security Posture Management automatically discovers and classifies NHIs across your environment.
The path forward: Future-ready for AI agents and NHIs
Every workload identity is a potential superpower — or vulnerability — for AI agents and automated systems. The question isn't whether you need a comprehensive identity security strategy. It's whether you'll implement it before your first AI agent incident.
In a world where AI agents make autonomous decisions through inherited identities, identity security isn't just about protection — it's about enabling your business' AI-powered future. Okta Identity Security Posture Management gives you the visibility and control to embrace AI agents confidently, starting with comprehensive identity discovery and management across your entire environment.
Because the organizations that solve the workload identity crisis won't just survive the AI revolution — they'll define it.
Ready to secure your workload identities? Discover how Okta Identity Security Posture Management helps leading organizations protect their autonomous future.
