Demo: Reports (Access Reports)
Transcript
Details
Speaker 1: Next, we'll look at several reports that indicate who has access to which application.
Speaker 1: I'm on the reports page in Okta, and on the right hand side you can see that we have a bunch of pre-canned reports. I'm interested in the one called App Access. I'll search for an application called Salesforce, and I'll click the green button to run the report. This gives me a summary view of who has access to Salesforce, how they got that access, and when they got that access. I'll click on the CSV link. This actually downloads the file, and this provides a wealth of information. I can see, for instance, who that Okta user name is, what their corresponding Salesforce username is. When they got assigned to Salesforce and how they got assigned to Salesforce. For instance, it might've been an individual assignment, meaning an administrator by the name of Peggy gave them that access, or perhaps it was a group and the group named that conferred that access is listed right here. Or maybe in the case of George Garcia, on the bottom row, he actually requested access to this application and it was approved by an admin or a username Bob Boss. There's a wealth of information here.
Speaker 1: Back at Okta, perhaps I want a different view of this data. Instead of looking at all users who are assigned to an application, maybe I want to get a list of all applications that a particular user has. I'll search for a user named Christine and run this report. I see that Christine has been granted access to five applications via a mix of group and individual based assignments, and I also see the details behind that. I know which groups or which individuals gave her that access and also on which date they gave that access.
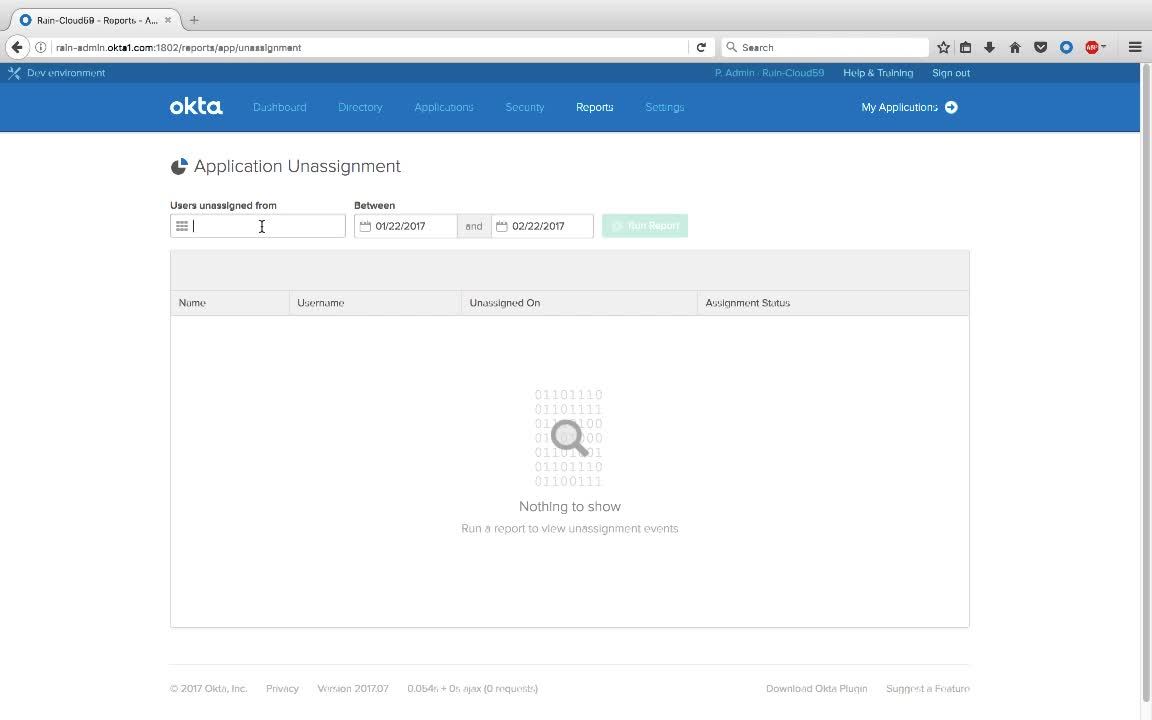
Speaker 1: Next, let's look at an unassignment report. And unassignment report tells you who was revoked from an application. This may be good for audits or may be good for just keeping track of licenses. I'll search for an application called Bamboo HR and I'll look for unassignment events in the past month. I'll run this report and I'll see that five users have been unassigned from Bamboo HR. Again, I can download this in a CSV format for further review.
Speaker 1: Next, we'll look at suspicious activity. Okta has several built in reports for suspicious activity. We have failed logins, and we also have user's locked out. This depends on your lockout policy. If you click on this, we get a list of users who failed to log into Okta properly. We have details around their username, their IP address, as well as the event, sign in failed.
Speaker 1: Next, we'll take a look at the system log, which presents a powerful way to view our data and inspect it more deeply. What you're looking at is a record of all events that Okta has captured. These can be login events, they could be imports, they could be single sign on. We're particularly the interested in potential security risks, so let's look at login failures. I can click on this event and what that did was further filter it down. Next, I want to look at failures, so I'll click on failure, and again, my query is being constructed and my results are further filtered.
Speaker 1: Let's dig into one of these a little more deeply. I'll expand event and I'll look at security context. I have information about where this user is coming from, including the autonomous system number. I also see that this user is actually coming from behind a known proxy based off of IP reputation. That may be indicative of an attack, after all, hackers hide behind proxies, so I'll click on this and that further filters down the results. I now have about six or five results.
Speaker 1: What you see here is a tight correlation. I have five users who all failed to login and they were coming from behind a proxy. Additionally, all the attacks seem to happen around 12:00 PM, so that may be suspicious. If I expand this, I can see, where did my events come from. Bob Boss, that user, generated two events and the other users generated one event each.
Speaker 1: Finally, if I want to save this query so I can run it later, I can simply click on save and I can give this report a name, so I'll call it Potential Security Attacks and I'll click save. Now, if I go back to my reports later on in the future, I can just come back here, click this link, and be taken back to a fresh page of results.
For your application management and user management needs, we’ll show you a few examples how Okta’s pre-built reports indicate who has access to which applications. Included are un-assignment reports and reports that show who has application access, how they got application access, and when they got application access.