- Home
- Centralized Logging
- Sumo Logic
Overview
Sumo Logic is the pioneer of continuous intelligence (CI) software. Organizations of all sizes can use CI to address the data challenges and opportunities presented by digital transformations, modern applications, and cloud computing. The Sumo Logic CI Platform automates the collection, ingestion, and analysis of your application, infrastructure, security, and IoT data to derive actionable insights within seconds. More than 2,000 customers around the world rely on Sumo Logic to securely build and manage their modern applications and cloud infrastructures. Sumo Logic delivers the CI Platform using multi-tenant SaaS architecture, across multiple use-case scenarios, enabling businesses to thrive in the new intelligence economy.
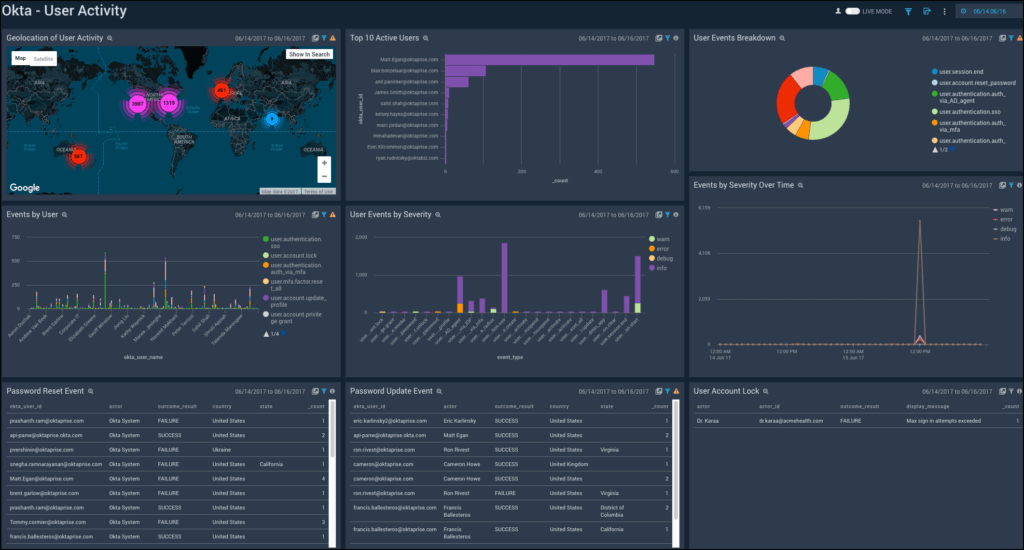
Sumo Logic's integration with Okta provides visibility and access control across your IT environment, so you can gather and analyze data from across your entire infrastructure.
The Challenge
- Cloud and digital transformation initiatives bring significant advantages, but introduce new security challenges
- There is more data to protect, in more locations–including cloud, mobile, and on-prem–than ever before
- Organizations need end-to-end visibility into security threats and security controls across the entire IT environment, from applications and data all the way to the end users themselves
The Solution
The Okta + Sumo Logic integration pairs the leading independent provider of identity for the enterprise with a cloud-native, realtime data analytics solution to provide visibility and access control across your IT environment
The integration lets you gather and analyze data from across your infrastructure: from firewalls and VPNs, from cloud-based apps including Okta authentication activities, and from other software and hardware
Easy-to-understand, pre-built dashboards present this data to security operations in real time, to help you spot anomalous activity and identify threats quickly
Security teams can automate response actions against these threats, like disabling suspicious users or forcing multi-factor authentication, to protect the enterprise

Functionality
Add this integration to enable authentication and provisioning capabilities.
Authentication (SSO)
-
API
-
Cross App Access
-
Entitlement Management
-
Event Hooks
-
Identity Security Posture Management Identity Security Posture Management helps to harden the identity attack surface proactively, by identifying vulnerabilities, prioritizing risks, and streamlining remediation.
-
Inbound Federation
-
Inline Hooks
-
Outbound Federation
-
Partial Universal Logout
-
Privileged Access Management
-
RADIUS
-
Secure Identity Integrations - Advanced Supports 4 of the following integration types for the 65+ business-critical applications: SSO, SCIM, entitlements, universal logout, workflows, and ISPM
-
Secure Identity Integrations - Fundamental Supports 3 of the following integration types for the 65+ business-critical applications: SSO, SCIM, entitlements, universal logout, workflows, and ISPM
-
Secure Identity Integrations - Strategic Supports 5+ of the following integration types for the 65+ business-critical applications: SSO, SCIM, entitlements, universal logout, workflows, and ISPM
-
Universal Logout
-
Workflow Templates
-
Workflows Connectors
-
SAML Security Assertion Markup Language is an open standard for exchanging authentication and authorization data between an identity provider (IdP) and a service provider (SP) that does not require credentials to be passed to the service provider.
-
SWA Secure Web Authentication is a Single Sign On (SSO) system developed by Okta to provide SSO for apps that don't support proprietary federated sign-on methods, SAML or OIDC.
-
WS-Federation
-
OIDC OpenID Connect is an extension to the OAuth standard that provides for exchanging Authentication data between an identity provider (IdP) and a service provider (SP) and does not require credentials to be passed from the Identity Provider to the application.
Provisioning
-
Create Creates or links a user in the application when assigning the app to a user in Okta.
-
Attribute Sourcing The application can be defined as the source of truth for a full user profile or as the source of truth for specific attributes on a user profile.
-
Update Okta updates a user's attributes in the app when the app is assigned. Future attribute changes made to the Okta user profile will automatically overwrite the corresponding attribute value in the app.
-
Deactivate Deactivates a user's account in the app when it is unassigned in Okta or their Okta account is deactivated. Accounts can be reactivated if the app is reassigned to a user in Okta.
-
Sync Password Push either the users Okta password or a randomly generated password to the app. This feature is not required for all federated applications as user authentication takes place in Okta, however some apps still require a password.
-
Group Push Push existing Okta groups and their memberships to the application. Groups can then be managed in Okta and changes are reflected in the application.
-
Group Linking Link Okta groups to existing groups in the application. Simplifies onboarding an app for Okta provisioning where the app already has groups configured.
-
Schema Discovery Import the user attribute schema from the application and reflect it in the Okta app user profile. Allows Okta to use custom attributes you have configured in the application that were not included in the basic app schema.
-
Attribute Writeback When the application is used as a profile master it is possible to define specific attributes to be sourced from another location and written back to the app. For example the user profile may come from Active Directory with phone number sourced from another app and written back to Active Directory.
Documentation
Here is a section all about documentation, integration, and implementation.
-
Datasheet:
Safeguard Your Security Ecosystem with Okta and Sumo Logic
Read it