Identity Rules: Forrester Recognizes Okta as a Leader in Zero Trust Security
Today, analyst firm Forrester published The Forrester Wave™: Zero Trust eXtended (ZTX) Ecosystem Platform Providers, Q4 2019*, which recognized Okta as a Leader in the Zero Trust security market. The report also recognized Okta as having the highest possible score in the evaluation criteria of “people/workforce security,” “automation and orchestration,” and “manageability and usability.” As Dr. Chase Cunningham wrote in Okta’s vendor profile, Okta’s Zero Trust approach can be summed up in two words: “Identity Rules!”
Check out the full report here.
Why Identity-Driven Security?
Before we dig into the full report, let’s take a step back. ”In 2009, Forrester developed a new information security model, called the Zero Trust Model, which has gained widespread acceptance and adoption*. The internal network could no longer serve as a barrier for trusted access to sensitive resources. Since then, the proliferation of mobile devices and rapid adoption of cloud services across the enterprise have served as a catalyst for the Zero Trust model’s rise and adoption in the enterprise.
Today, putting up a network perimeter is not sufficient to protect against the modern threat landscape. As users increasingly need to access apps and infrastructure from any network, device, or location, identity becomes the single control point for access management. In other words, identity is the new perimeter and serves as the foundation of a modern security strategy. Organizations like AECOM, 21st Century Fox, and USA Today have leveraged the unique power of the Okta Identity Cloud as the foundation for their Zero Trust security strategy.
Earlier this year, Okta was named a Leader in The Forrester Wave™: Identity-as-a-Service (IDaaS) for Enterprise, Q2 2019, scoring highest in both “current offering” and “strategy” categories across all evaluated vendors. Forrester calls out the critical convergence of identity and security in this report: “Further, organizations increasingly view identity as one of the cornerstones of the Zero Trust security framework in which every action and event can be attributed to an identity.”**
Making Zero Trust a Reality
Zero Trust has stirred lots of buzz in the security industry, but now the question is: How do organizations turn this framework into a scalable solution?
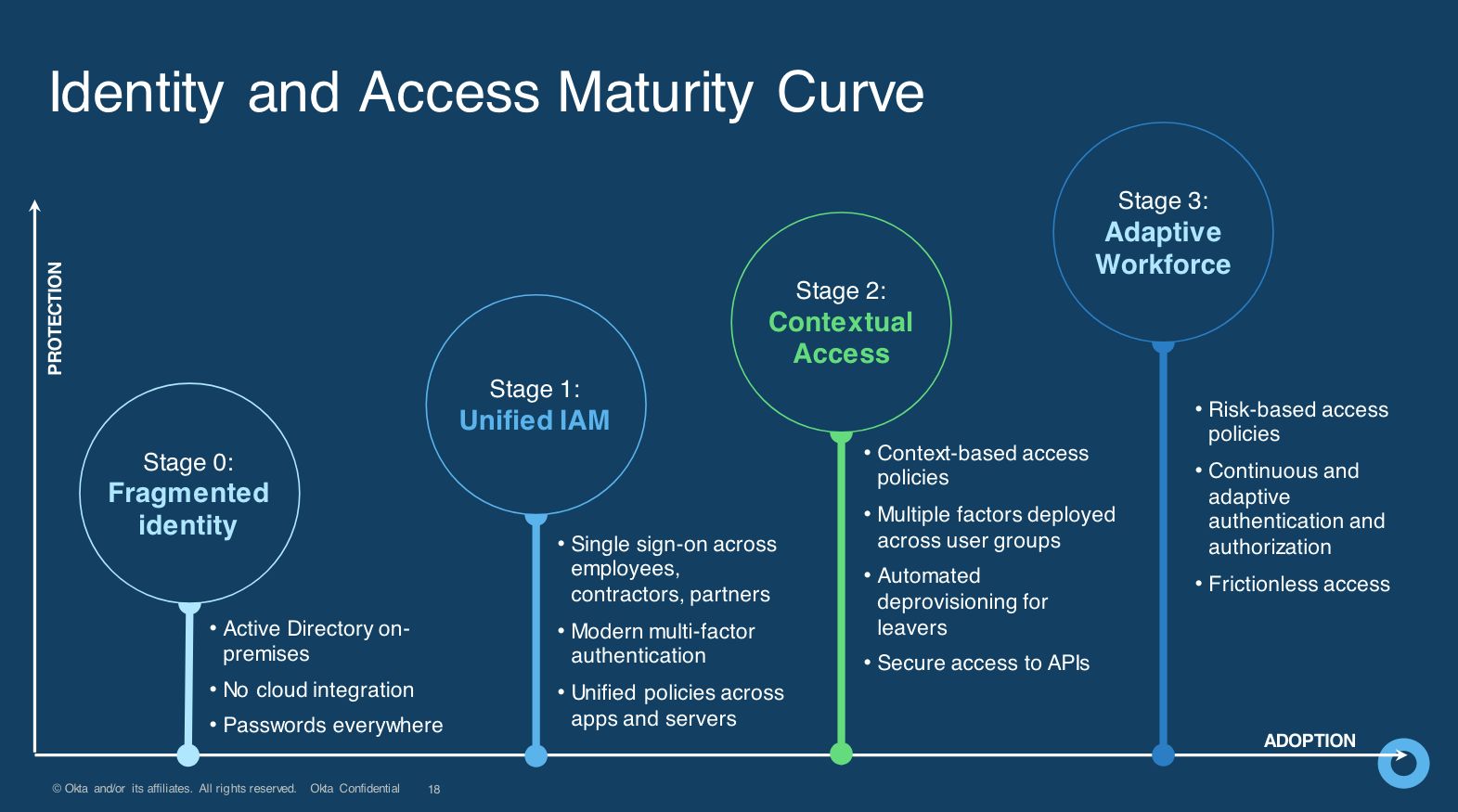
In addition to investing in our product advancements and integrations to best support our customers, we are also rolling out Okta’s Identity Zero Trust Assessment Tool, designed to help your organization determine where you are on your path to identity and Zero Trust maturity and also to provide personalized recommendations for how to improve your security posture with identity and access management.
Give it a try, and let us know what you think of your results. We’re happy to review them, share best practices, and help see how you can further strengthen your identity-driven security foundation.
For more information about how organizations are approaching Zero Trust security, download our whitepaper, Getting Started with Zero Trust: Never Trust, Always Verify.
*”No More Chewy Centers: The Zero Trust Model Of Information Security”, Forrester Research, Inc., March 23, 2016 **Forrester's Identity And Access Management Maturity Assessment, Forrester Research, Inc., September 12, 2019

