- Home
- Directory and HR Sync
- UKG Pro
Overview
UKG Pro is a powerful human capital management (HCM) solution. Transform your business with a connected global workforce experience delivered through resilient and mindful HR technology. From payroll and talent to service delivery and surveys and everything in between, UKG Pro is the powerful HCM suite you need to drive people-focused results.
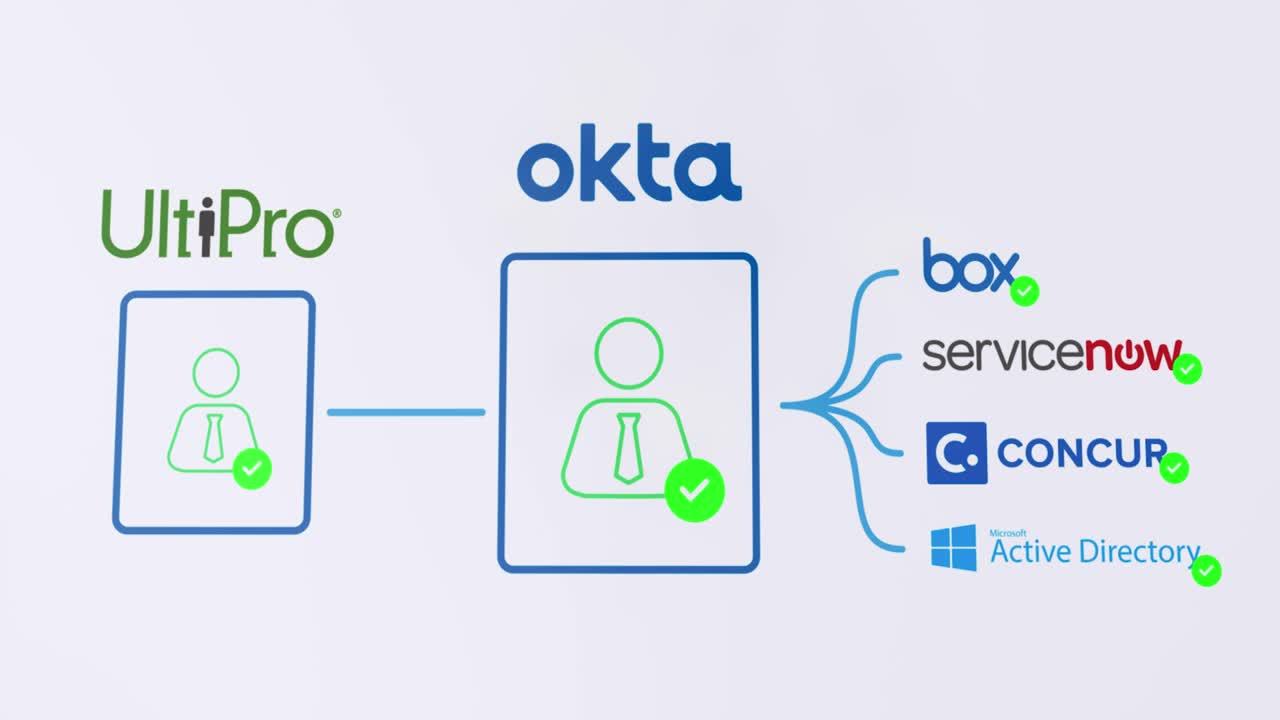
The pre-built UltiPro app integration with Okta vastly simplifies and automates communication between HR and IT, accelerating your processes by automating and streamlining user lifecycle management.
The Challenge
HR Information Systems (HRIS) like UltiPro are often an enterprise’s system of record. HR must share employee data back and forth with IT to enable the creation of user accounts, provision applications, set permissions, and deactivate users who leave the company. This data transfer is often done through email and other manual means, which is both inefficient and risky. And as more and more apps and directories migrate to the cloud, HR and IT need a more efficient and less risky system for communicating and processing employee data.
- Inefficient communication: Transferring data via file extracts, phone, or email attachments wastes hours and adds friction
- Risky employee departures: On average, it takes two days for enterprises to fully deprovision a departing employee
- Unproductive users: Employees waste time waiting to be provisioned to apps or for permissions updates
The Solution
The pre-built UltiPro integration with Okta vastly simplifies and automates HR-IT communication, reducing friction and automating and streamlining common lifecycle management processes. Employees’ data and profile updates in UltiPro propagate across IT systems, including Active Directory, SaaS and on-premises applications, informing the entire user lifecycle from onboarding through offboarding.


3 months
to develop proof of concept, validate, and roll out
Functionality
Add this integration to enable authentication and provisioning capabilities.
Authentication (SSO)
-
API
-
Cross App Access
-
Entitlement Management
-
Event Hooks
-
Identity Security Posture Management Identity Security Posture Management helps to harden the identity attack surface proactively, by identifying vulnerabilities, prioritizing risks, and streamlining remediation.
-
Inbound Federation
-
Inline Hooks
-
Outbound Federation
-
Partial Universal Logout
-
Privileged Access Management
-
RADIUS
-
Secure Identity Integrations - Advanced Supports 4 of the following integration types for the 65+ business-critical applications: SSO, SCIM, entitlements, universal logout, workflows, and ISPM
-
Secure Identity Integrations - Fundamental Supports 3 of the following integration types for the 65+ business-critical applications: SSO, SCIM, entitlements, universal logout, workflows, and ISPM
-
Secure Identity Integrations - Strategic Supports 5+ of the following integration types for the 65+ business-critical applications: SSO, SCIM, entitlements, universal logout, workflows, and ISPM
-
Universal Logout
-
Workflow Templates
-
Workflows Connectors
-
SAML Security Assertion Markup Language is an open standard for exchanging authentication and authorization data between an identity provider (IdP) and a service provider (SP) that does not require credentials to be passed to the service provider.
-
SWA Secure Web Authentication is a Single Sign On (SSO) system developed by Okta to provide SSO for apps that don't support proprietary federated sign-on methods, SAML or OIDC.
-
WS-Federation
-
OIDC OpenID Connect is an extension to the OAuth standard that provides for exchanging Authentication data between an identity provider (IdP) and a service provider (SP) and does not require credentials to be passed from the Identity Provider to the application.
Provisioning
-
Create Creates or links a user in the application when assigning the app to a user in Okta.
-
Attribute Sourcing The application can be defined as the source of truth for a full user profile or as the source of truth for specific attributes on a user profile.
-
Update Okta updates a user's attributes in the app when the app is assigned. Future attribute changes made to the Okta user profile will automatically overwrite the corresponding attribute value in the app.
-
Deactivate Deactivates a user's account in the app when it is unassigned in Okta or their Okta account is deactivated. Accounts can be reactivated if the app is reassigned to a user in Okta.
-
Sync Password Push either the users Okta password or a randomly generated password to the app. This feature is not required for all federated applications as user authentication takes place in Okta, however some apps still require a password.
-
Group Push Push existing Okta groups and their memberships to the application. Groups can then be managed in Okta and changes are reflected in the application.
-
Group Linking Link Okta groups to existing groups in the application. Simplifies onboarding an app for Okta provisioning where the app already has groups configured.
-
Schema Discovery Import the user attribute schema from the application and reflect it in the Okta app user profile. Allows Okta to use custom attributes you have configured in the application that were not included in the basic app schema.
-
Attribute Writeback When the application is used as a profile master it is possible to define specific attributes to be sourced from another location and written back to the app. For example the user profile may come from Active Directory with phone number sourced from another app and written back to Active Directory.
Documentation
Here is a section all about documentation, integration, and implementation.