The Foundation for Cloud-first, Mobile-first IT
In the legacy IAM world, identity governance and administration (IGA) products were often designed for maximum flexibility – but this led to endless customization work and complexity. Okta offers a solution to access management for the modern world. This paper introduces identity lifecycle management – user provisioning and de-provisioning – and the importance of building a solid foundation for cloud-first, mobile-first IT.
Getting Started: Becoming the Department of “Yes”
Gone is the notion of command and control IT, where all devices, applications and user experiences were dictated centrally. Adoption of cloud and mobile, with a boost from the Okta Application Network, has enabled organizations of all sizes to start saying “yes” more often to business groups and end users. New marketing app? Yes! New tablet? Yes! New special-purpose project management tool? Absolutely!
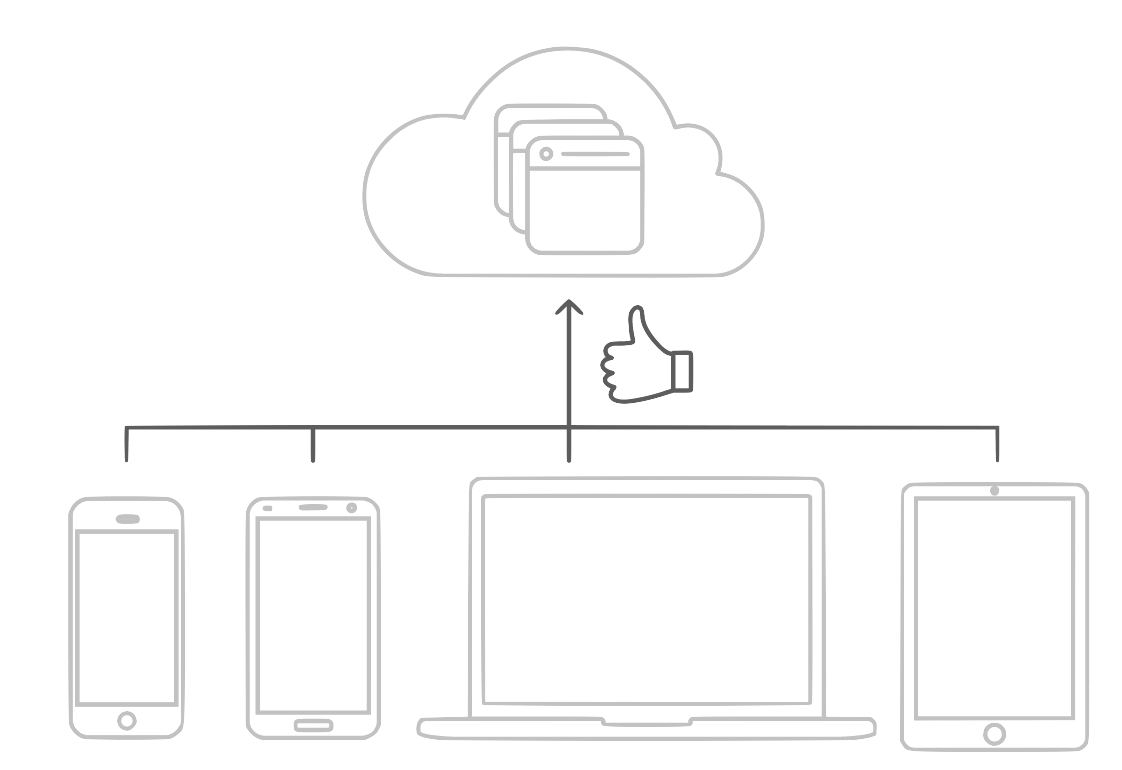
With all these yeses, the number of cloud apps an organization uses explodes. Customers tell us before they purchase Okta, they typically have five to seven cloud apps. Within six months of purchasing Okta, customers connect 10 applications, with 10% of Okta customers eventually connecting more than 40 applications. In the Okta Businesses @ Work report, we found that the average Okta customer has 13 cloud applications.
For most customers, Okta solves the basic problems of too many helpdesk calls and too much wasted end-user time remembering passwords, and the security concerns of users re-using personal passwords across many business apps. With Okta Provisioning, many of our customers also reduce IT admin time spent provisioning and deprovisioning accounts in applications.
Connecting apps for SSO and automating provisioning for IT apps like email and ITSM are great, but really just the start. As you get deeper into trying to automate provisioning for your full catalogue of applications, you start hitting barriers to managing your business process that are not easy to overcome.
Integration to Apps Is Not Enough
Okta’s unique role in managing identity for thousands of organizations enables us to look at trends in our customers’ use of apps and gain a deeper understanding of what customers need. About a year ago, we found that customers were not using as many provisioning integrations as they could be using. Of the applications they had connected for single sign-on, there were several where Okta had a provisioning integration as well, but the customer had not enabled provisioning for that app.
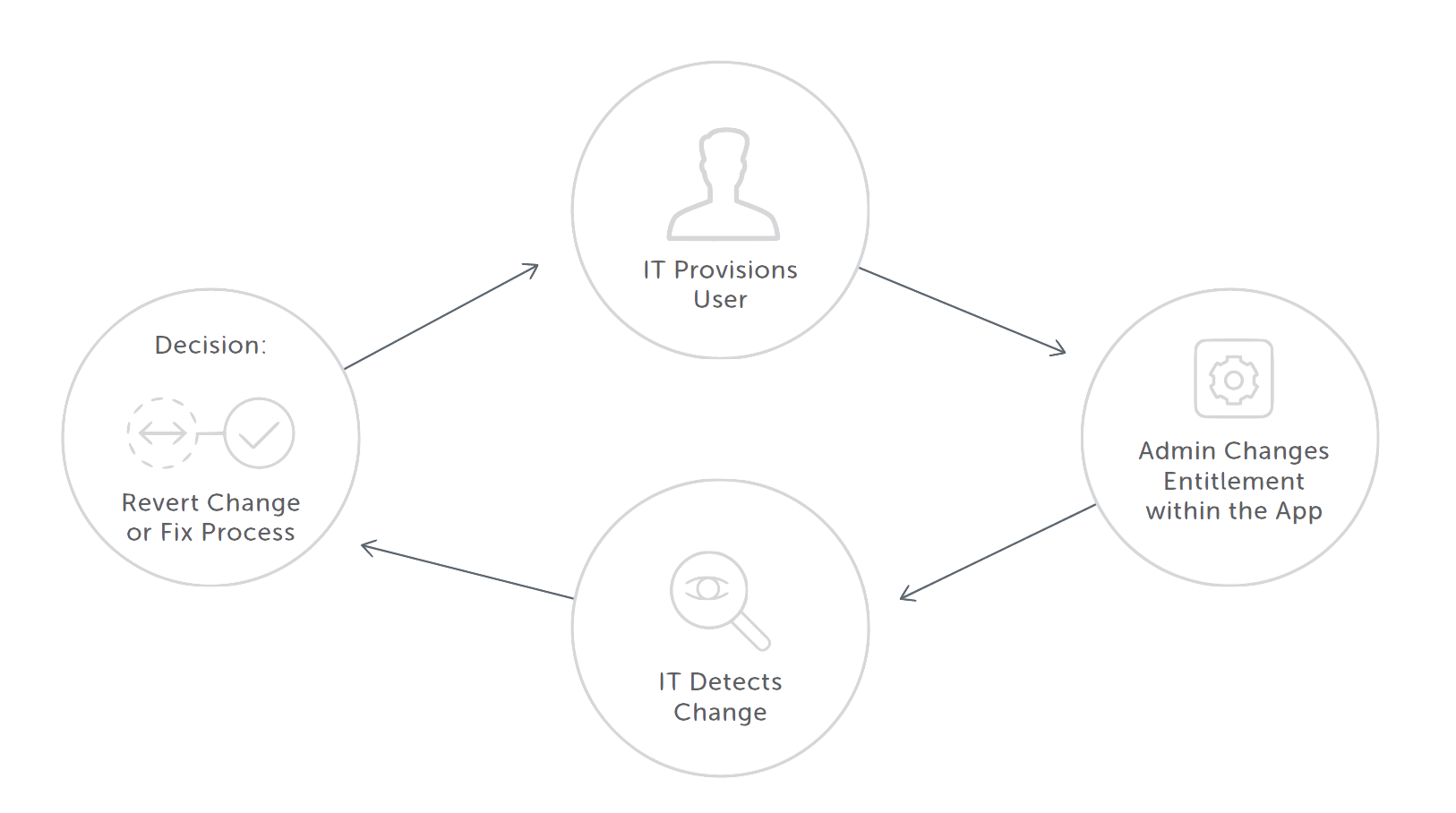
The root cause of this low usage of provisioning integrations was that IT needed additional “intelligence” around identity lifecycle management and governance in order to automate more applications. IT organizations spend a lot of time just keeping track of who should have access to what, and at what time, and for how long. Keeping up with application requests from users as well makes their job even more difficult. And finally, business teams often have their own application admins that can manage users without the knowledge of IT. IT needs to be able to keep an eye on overall changes within an application and sync those changes back to Okta or correct them in the app.
There are two distinct types of applications IT needs to manage. First are “birthright” applications like email, expenses and ITSM that are provisioned to everyone in the company, and which often have similar entitlements. However, since these are core IT applications, they require rich synchronization of attributes. And, they are often heavily tied to the process around employee onboarding and offboarding.
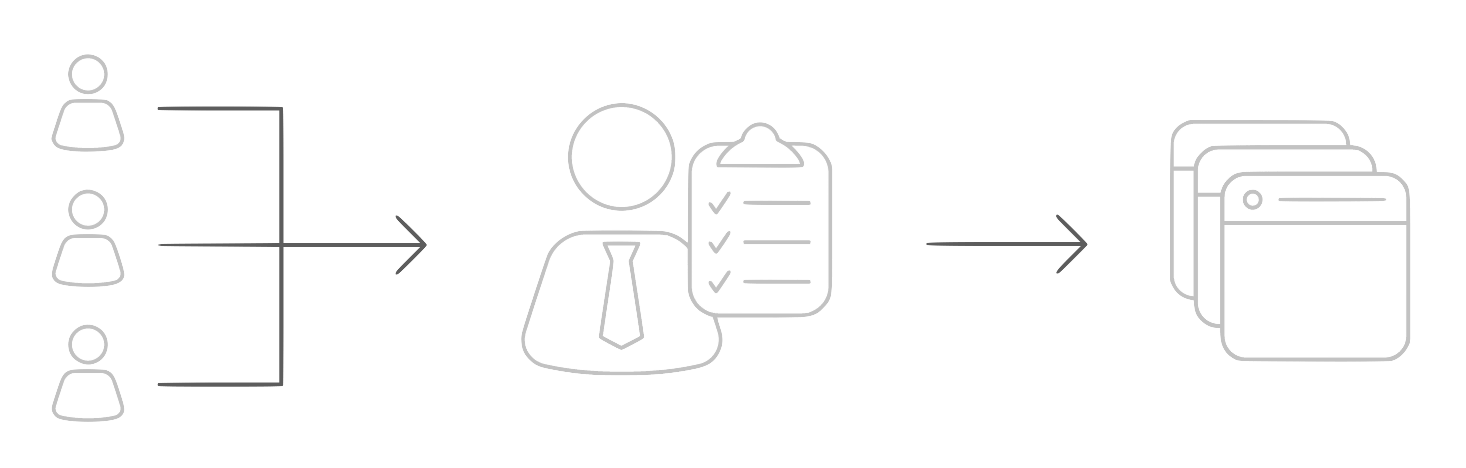
The second group are business apps. These are often provisioned based on a business unit—like CRM being provisioned to a salesperson, or a marketing demand gen app to someone in marketing. Users also have much more nuanced entitlements, based on role, seniority or other factors. Often, the knowledge of how a user should be provisioned sits with an admin in the business unit—not someone in IT, let alone on the identity team.
There are clearly many deeper issues to solve here in order to operate an efficient IT shop in a cloud-first, mobilefirst world. The common thread across these issues is identity lifecycle management.
Building a Solid Foundation with Identity Lifecycle Management
IT leaders and administrators consistently provide feedback to Okta that efficient identity lifecycle management is the absolute foundation to IT. It drives who has access to what—everything else proceeds from there. VPN access, MFA policy, BYOD policy, and application access entitlements all depend on the foundation of user lifecycle management. To achieve full adoption of provisioning, you have to solve lifecycle management.
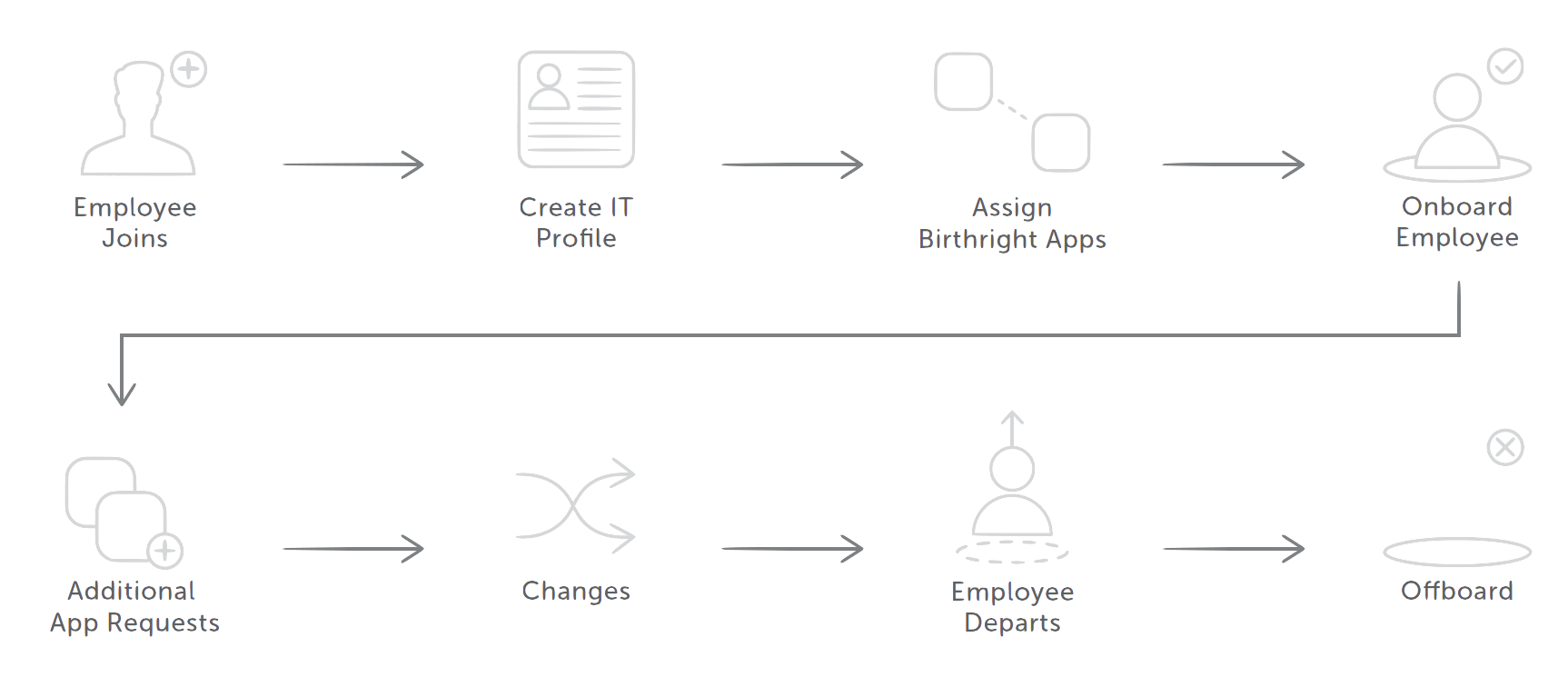
A lifecycle management engine helps drive the process around provisioning. It enables IT to orchestrate more of the onboarding process, automate how users are assigned groups, provide flexibility for how business applications are provisioned, and provide admins in the business with more power in the provisioning process.
In the legacy IAM world, identity governance and administration (IGA) products were often designed for maximum flexibility—but this led to endless customization work and complexity. Okta offers a solution for the modern world. Created with insight from across our customer base, Okta Provisioning uses the best practices of efficient IT organizations and implements them with easy-to-configure options. With Okta Provisioning, IT can get the most out of the largest network of deep provisioning integrations. Organizations can then build on this foundation with Okta Adaptive MFA and Okta Mobility Management, to make IT more agile and secure.