Oktane18: How Phillips 66 Fuels their Cloud Security Practice with IAM + CASB
Transcript
Details
Kurt: My name is John Myer, I'm with Okta, and welcome to our first session of the day, "How Phillips 66 Fuels their Cloud Security Practice with IAM + CASB." I just have a couple of housekeeping items, we just got surveys a couple minutes ago so you might not have all received one of these, but try to pick one up. We'll have them in the back. You can fill it out so that we can make sure these sessions are even better next year. After you fill them out, you can leave them with one of us in the back, or on one of the back tables. I appreciate that. Also, a reminder, we're recording all of our session over the next couple of days. So, please, silence your cell phones and remain seated through the entirety of the session since we are recording it. I'm going to introduce the speakers and then they'll be able to give a brief bio for each other. We have Srini Gurrapu from McAfee and Kurt Haberstroh from Phillips 66. So, gentlemen, take it away.
Srini: Thanks, John. Good morning. Welcome everyone. I'm Srini Gurrapu. I'm the Chief Evangelist and Vice President of Customer Solutions at McAfee club business unit. I've been in the security industry for the past twenty years with companies like BlueCoat, Neoteris/Juniper and FireEye. The last five years have been very transformational for me and very much focused on the cloud security. Go ahead.
Kurt: I'm Kurt Haberstroh. I'm with Phillips 66. I've been in the oil/natural gas industry for, going on ten years now. I run our cyber security operation center. I also have the unique experience to be able to combine, we're going to be talking about today, with the CASB implementation and identity management as in my previous role I was in charge of our identity management group.
Srini: Excellent. Today, the focus of our discussion is about how Phillips 66 fueled their cloud security with a combination of Okta and McAfee SkyHigh products, both for identity and access management and the cloud access security broker. So what we're going to do is, I'm going to start with a quick overview on the cloud security and then Kurt is going to walk us through the Phillips 66 cloud first strategy and their journey. Then we're going to have some interactive discussion about how to govern the cloud services within an organization like Phillips 66, and some of the best practices. Then, we are also going to talk about some of the other use cases for later Office 365 and how to secure applications in the public cloud such as Amazon and then we're going to open up for some Q&A towards the end. So, if you look in the IT security market, every major technological shift created new type of security challenges. It also resulted in new big markets to emerge. If you look back about thirty years ago, the shift from mainframe to the PCs, gave us the opportunity to make computing available to everyone with the advent of PCs. That created big security challenges with data decentralization, now scattered all over the endpoints. That created the opportunity where we created new security markets, the notion of endpoint security with companies like McAfee and Semantic. Then the Internet revolution happened. With the promise, with the opportunity to connect everyone and every organization to the Internet. That created new diverse security challenges. Every organization had to focus on how to protect themselves from Internet born threats. That created new security markets, such as Nexum firewall or a Proxy, the pyramid of security solutions with features such as ‘Nowhere’ filtering, Malware, or Anti-Malware.
Now, we are probably in the greatest IT shift. That's the Cloud. If you look at Cloud, what does Cloud literally mean? For the first time, we are having to host our applications and data on somebody else's premise. That's precisely what cloud means. Until now, our security practices have been built on the notion that we owned our endpoints, we owned our perimeter, we owned our infrastructure, so we were very much what we were doing as in the infrastructure security. Move to the Cloud, we don't have the luxury anymore. We don't own the infrastructure. Yet, we are responsible for our applications and the data. And this gives us the opportunity to do security right by focusing on the crown jewels], that's the identity and the data. So this gives rise to the new next gen security markets, such as IAM and the CASB with companies like OKTA and McAfee.
And if you look at the Cloud, how does Cloud manifest in any organization? There are three primary manifestations. The first one is Shadow IT. These are the cloud services that your employees and departments bring into the organization, such as personal Dropbox, Google Drive, or Slack, or Evernote or even personal or the developers launching their own inspects on AWS. The second manifestation is the sanctioned cloud services. These are the SaaS services that your organization is bringing to the organization, such as Office 365, Salesforce, Service Now, or Slack, Workday, and this is probably the fastest growing sector. And the third one is the public IAS, AWS Azure, or DCP. Where you host your applications or the data on one of the public cloud providers. And every organization, depending on your maturity, you have different levels of options across these three cloud platform factors. But if you look deeper into the Cloud, and understand the data flows, it's no longer just about not out. It's no longer from users uploading the data to the Cloud services. About 60% of the data transactions within the Cloud are East-West, across the Cloud services. And what that means is, that pretty soon security controls that you've been relying upon, such as Nexum Firewalls or the proxies, they no longer work. They don't provide the controls for your East-West traffic. And this is where the Shared-Responsibility Model comes into play. When I talk to many customers, until about three years ago, Cloud meant, Hell no. We don't want to move to the Cloud for security. Now, we are switching to the other dimension, here I've moved to Office 365 on Amazon that means I get 100% security automatically. This is precisely the incorrect assumption that's causing the majority of the data breaches in the public Cloud or any one of the SaaS services. We need to understand the Shared Security Responsibility Model.
The Cloud provider is responsible for infrastructure security, but we still need to govern our identity, we need to govern our data, we need to provide access controls for your endpoint. The two big pillars in the Shared Responsibility Model are governing the identity and governing the data. If you don't do that, what happens? We are going to be responsible for the majority of the security breaches. In fact, if you look at all the major security breaches in the last one year, they're all about happening in the public cloud. We are not even doing some of the basic things such as configuring the right permissions for S3 buckets. When we go look at some of the public cloud IAS or Office 365, we don't even do the right permissions of setting up the Read Right or understanding your own data flows. And unfortunately in the Cloud, there is no perimeter to protect you. If you don't configure your identity, if you don't configure your data access policies, the data is available worldwide.
At these breaches, to protect our identity and the data, we need a new a security control point and that's the new perimeter that's with identity and the data. So with the right identification governance controls, and the data and the configurations controls with the combination of an IAM solution and McAfee solution, this is how we're going to secure our assets in the public cloud. Whether it's Shadow, Sanctioned, or Public IAS. So with that overview, Kurt, if you could walk us through your Cloud strategy?
Kurt: Yeah. Thank you, Srini that was a great overview and kind of leads into some of the challenges we're all facing right now. So Phillips 66 Cloud strategy, just a couple of introductory slides for who we are. So first I have to show our standard cautionary statement: If there's anything that I say here today that may be forward looking, do not go invest based on that information. Uh, Phillips 66, so who are we? We're a diversified energy manufacturing and logistics company, one of the largest refiners and transportation owners in the nation. Our mission is to provide energy and improve lives. We do this by operating under three main values of safety, honor, and commitment. If you don't know who Phillips 66 is, you may recognize us by some of our other brands: Conoco, 76 for your racing fans in the audience, RedLine lubricants and then also Kendall Motor Oils. And then we deliver this by having a high-performing organization, and this will feed into to some of our discussion in a little bit around what does it take to execute a sound strategy for the Cloud. It's our culture, really building on a culture of 100 years of tradition, that family atmosphere, making sure that everybody's there working together. Our capabilities. We track the top talent from the places that we recruit. We develop, we train, we empower our employees to execute on the things we expect them to execute on. And performance. We really value the way things are done, not just how we do it. One of the things I always like to mention when I'm talking to my group about what we do and how we do it is to mention Bill and Ted. Be excellent to each other. And that's what we focus on.
So commitment to technology. I did pull out one of our slides around one of our primary business units is Research and Design. We are the only downstream industry company with Research and Design organization that's been pioneering innovations for years. How many of you have heard of HDPE? High Density Poly Ethylene? Plastic. Come on, I know more of you have heard of plastic. That was researched and designed and invented in Bartlesville, Oklahoma with Phillips Petroleum Company. So we've been on the tip of the spear for quite some time in innovations. IT has now had that opportunity to lead in innovation for the company.
So, our Cloud strategy. What are we doing and how are we trying to execute it. About a year ago, we put in a plan to execute on this Cloud strategy very aggressively in the next 18-24 months. So we look at the right platform for the job. We're not set on any one item or any one place to put this strategy so we're multi-platform. Multi-leverage. We want to make sure that the tools and security and visibility we have can look across an entire ecosystem of cloud based solutions. Our migration approach. We want to be able to rationalize, standardize, modernize, our current applications that we have, and then we bring on new applications, make sure that they're natively leveraged within the Cloud. We want to be able to offer these as a service to our business. Optimize the operations of those, right size the compute power for what it's being used for, utilize secure and efficient processes that we might now be using today. We want to be able to migrate a lot of our on-premise data infrastructure to be able to minimalize location specific resources and then use the power of the Cloud to provide those across the world. And then again, back to our high performing organization we need to be able to read to our personnel to be able to execute this effectively. And at the center and core of these things are two of the main sponsors here today of Okta and McAfee SkyHigh.
So how does Okta help enable our Cloud infrastructure? Well through productivity, one of our main business units within marketing, our IT operations, and a venture that we're currently getting into with our ERP redesign. They help enable our users to be able to access these services and give us the opportunity to monitor that access and provide the controls necessary through McAfee SkyHigh around each one of these critical functions that our business uses day to day. So how do we govern these things? Srini?
Srini: So this very exciting to me, like, organizations like Phillips 66. You know when I talk to many of the organizations, you know about three years about everybody was very tentative about the Cloud, but now everybody is moving towards the Cloud first, or in fact some of the large organizations are even marching toward Cloud only. So where do you define yourself? Are you Cloud first, Cloud only? Do you have any timeline on when you think you're going to get there?
Kurt: So as I mentioned the timeline is around that 18-24 months to get most of our infrastructure to that Cloud based operations. The goal is Cloud first, I think the long term vision's going to be Cloud-only.
Srini: Excellent. So, what we're going to do now is, you know, like many of you, Phillips 66 also has a plethora of Cloud Service-
Srini: Phillips 66 also has a plethora of cloud services aligning with their cloud first in the cloud only organization. So we're going to go about in some of the best practices on how to govern the cloud usage across the three manifestation. So before I jump into the details, how many cloud services do you think you would have before you marched on this digital transformation?
Kurt: Quite a few more than a hundred. So that's one of the reasons why we brought in Sky-high was to help answer that question for us. And we're focused on the shadow IT portions of what Sky-high can provide and seeing ... My jaw kind of dropped during Todd's presentation earlier when he was talking about Oktaves on-ramp technologies. We were doing this with Sky-high 9, 10 months ago with the data that we're able to pull out of there to determine what are those services that our employees are using? Where do we need to put controls around? How do we answer the question of what are those high risk areas we need to focus more on? What are those applications and services we need to be accepting to? And which ones did we kind of need to continue to monitor for the access controls that we need to put in place?
Srini: Excellent. And this is the data from the Sky-high Shadow IT console is about roughly about 1800 cloud services, and this is the cloud situation that every organization is in. So, what was your reaction when you saw 1800 cloud services already being used within Phillips 66? And when I talk to customers everybody is trying to ask this profound question on, what are these cloud services? How do I categorize these cloud services? And what are the right controls? So did you have any methodology or did you come up with any best practices on how to govern this 1800 cloud services?
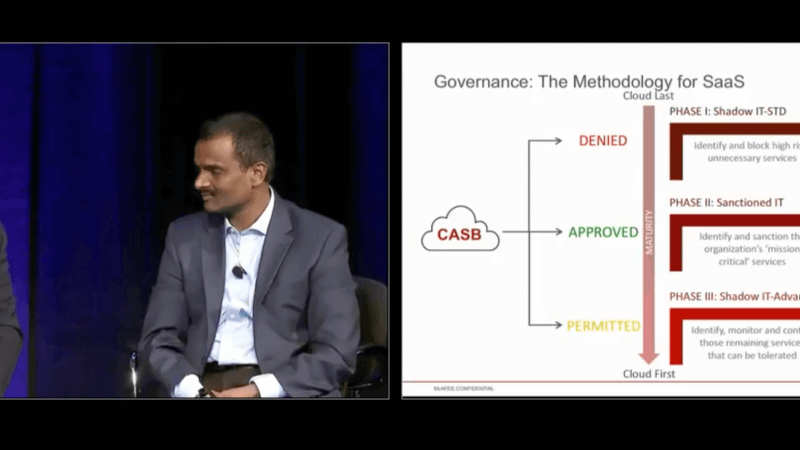
Kurt: So we really started looking at it from more of a risk perspective, like all IT security groups should be, right? So what is the actual risk in place with using some of these services? And then making the determination based on that of, is this something we want to build a block, allow, or permit to be usable within the environment, which we kind of go into here. So really the big question and the big thing we need to solve was the visibility into what is being used, as we've demonstrated, and then start classifying those. We use a governance group that helps with that process, but then also makes a determination on which applications do we want to be able to allow? Which ones do we want to deny? Straight off the bat, the easy solution is denied the higher risk applications, right? But then you get into the more difficult conversations with the business of why are you using this? What do we already have in place that you could use this as an alternative? And if there's nothing there available, how do we help enable you to use this securely?
Srini: Excellent. This to me was the very profound insight on how customers are governing their cloud services. It's no longer just about allow or block. It's about understanding the business context, whether we have standard MSA sign up with this cloud services, and what's the risk that each cloud provider brings to the organization, and then the way they structure this into the three categories suggest what are denied, what we should be going to block, what are approved and what would are permitted. And then providing the right controls without the Capsi. So, explain this slide to me.
Kurt: So the next two slides actually will help walk us through the path of, how do you start classifying these, right? With Okta McAfee working together on the approved apps, you can sanction those as these are explicitly allowed and with that integrate your Okta systems, get your federated solutions, your identities within those. So you have that accessibility and usability for those explicitly allowed services. Then you get to the permitted level of these aren't necessarily bad. However, it's not something that we've corporately or enterprisingly agreed on. This is the solution, but we're not going to block it because we do see some business value, or the business has indicated to us there is value in them using these things and we want to be an enabler for that. And then you get to the easy ones. Now I call it, getting to that deny category should it be the easiest portion, especially when you're going through that first cut of, what are the things that are inherently malicious? You have a lot of your pdf converters, your image converters, your areas where you're uploading files to be shared that is insecure, and you can determine that based on the data that Sky-high puts together for you.
Srini: Excellent, and to me this is very interesting that we are creating the circles of trust. At the deep inner circle is your core business services like Office 365 Salesforce, and then the next trusted circle is the permitted services. The services that Phillips 66 may not own. They don't own, but yet they are useful for the employees or the partners. And then the outer circle is something that we can easily block. And this type of governing or creating circles of trust with the grouping will then allow you to naturally come up with the right type of controls. Like the inner circle, you need to have your own identity or the federated identity. At the permitted circle, it may not be your identity but you still need to provide the SSO controls. And then the outer stuff, which simply should block them. And similarly, same thing on the data side with the Office 365 Salesforce. You need to have even more rigid data security controls because that's your sensitive data, and then at the permitted level it's all about preventing the sensitive data leakage. So this type of structuring, I mean it's very insightful on how our customers are governing their cloud services and then using Okta and McAfee appropriately to provide the right security controls.
Kurt: That's right. So just another view of what we just discussed. So what is the approach we should take on doing this based on the maturity level, right? So obviously, when you begin you need to understand what is in use? What is going on in your environment? How do you categorize those? And so, the first one off the bat is that deny level. So what's the higher risk items you need to be able to block and identify based on services? Are the services even necessary? If they're not, and you have a great example here of some of the services that are a bit easier to say, those should be blocked, no brainers. Then you get into your sanctioned IT's, and these are your inner circle of trust. What are the services that you want to be able to provide that ease of access to, but also have the controls around for where people can access them, what data is that they can put into it, and how they are able to share that with people outside of the organization. And then you get into a little bit harder questions to answer and that's when you get into the permitted circle of trust. The shadow IT advanced area where there is business value, the business has indicated there's value to it, but there is still some inherent risk to using some of those because you don't have that relationship with the vendor or it's not a thing you own. It's something that you are utilizing that's already in the cloud environment.
Srini: That's excellent. And for Phillips 66, this is the risk-based priority that they took on the journey. First started the shadow IT, then going into the sanctioned IT, and then advanced shadow IT and iOS. But for other organizations, depending upon how mature you are in terms of using this cloud services, you may start your journey at a different place. Like for example, securing Office 365 might be your entry level point, or securing the perimeter or the public IS could be your entry point. But eventually you will secure all the three different categories of the cloud services, right?
Kurt: That's right. So as we walk through, how do we govern this? So we have to first identify. We've mentioned that a couple times. So when we actually started, the slide that we had up with my dashboard, I think it had around 1800, is actually newer. That's from May 5th, but when we started this back in October it was well over 2000, almost closer to 3000 services that we hadn't yet identified and classified into one of these categories. With our governance group, we understand the risk of each one of these services starting with those high risk ones. And then we need to make some decisions. So the easy decisions are block the malicious, the ones that spread malware easily straight off the bat. Then you have to get into the business critical discussion. So if it's a high risk plus business critical, is there a way that we can use the cloud trust registry? Which of those of you that may be Sky-high customers knows the value in that. Those that aren't, it's a great tool to be able to go look and research services that may be in use to find out what is the risk level? What's given them the score that they're receiving? And then also, how frequently are they being reviewed on those risks? And then that can come to either a block or finding a different solution. If it's high risk plus non-business critical, you kind of go into that same category that we do with the PDF converters and image converters and image storing sites of, just block this service. So those are the easy decisions to make with the governance board. The harder decisions are getting into when you start seeing those business critical applications and you want to empower the business to be able to use those. Identifying what is the correct service they should be using and converting them to that service. So all this is done with a standard security stack powered by Okta who provides that federated identity for us into our approved services. McAfee, which provides the insight and data to make those critical decisions on what we want to be able to allow to use and then empower the business to find acceptable services. And then Check Point is the solution that we use to enforce these policies.
Srini: Excellent. So, Kurt, I'm going to put you on the spot a little bit.
Kurt: Okay.
Srini: So, when you acquired us, you were Sky-high.
Kurt: Yes.
Srini: Now we are McAfee.
Kurt: Great question.
Srinib So how did it change your strategy? How do you feel about Sky-high McAfee?
Kurt: I'm actually really excited about the future of the Sky-high McAfee integration. One of the things that have those, you might have different security products within your stack. It's converting all of that information into one easy to read pane of glass, right? For your security analysts to go see common information across different environments and then convert that into actionable items to take care of can be difficult sometimes, especially when those don't communicate well with each other. But now having McAfee and Sky-high together, we can see from endpoint to network to cloud-based infrastructure, one pane of glass, the entire ecosystem of how our data and users are using the world.
Srini: Excellent. I think this is our combined vision at McAfee and Sky-high. As you are moving to more of a cloud first or cloud only organization, the two places where your enterprise data is going to live are in the end point or in the cloud. So our combined vision in being part of the McAfee is to provide the device to cloud end to end security with our partnership with Okta. So we're very excited about our opportunity being inside McAfee to help customers like Phillips 66 on how we can secure end to end data both on the device and the cloud. So thank you Kurt, it's wonderful insight and I hope we can help you more, get you there faster on the cloud only state. So what I thought I'll do is share some of the other use cases in addition to securing the identity and the visibility, and what are some of the best practices in Office 365 and some of the public cloud.
So if you look at the Office 365, many of you are using Office 365. There's SharePoint, there's email, there's OneDrive. But if you look at it, when people are sharing documents from SharePoint or OneDrive, is it going through your parameter or is it going through any one of the network device? Nope. About many of the data transactions that are happening from within Office 365 are bypassing your traditional network security controls. So you need a Caspy with the new architecture that is much more relying on the API's connecting to your Office 365 to secure all the data flows. So looking at all the use cases that customers are using on Office 365, the first and foremost use case is to provide secure collaboration controls for all the data exchanges that are happening from within your SharePoint or OneDrive. That's the dominant use case that I see across all the customers. And the second one is to understand your data, and how do you make sure that your employees are not putting any one of your internal sensitive data onto one of your SharePoint public sites? So again, watching transactions, watching the data and classifying them to make sure that it's only going to the legitimate places on the SharePoint is the second dominant use case.
And the third one. Going back to our vision, what Kurt said about the device to the cloud security. While we secure all the data in their Office 365, where's the biggest exfiltration vector? Your employees downloading the data from your SharePoint onto their personal devices. So to be able to understand the context of the device and providing the appropriate level of control, whether it's only a read-only access into the Office 365 or even putting a DRM wrapper so that the data, even if it comes to an unmanaged device, it still stays secure. And the last, the next one is about when you look at the Office 365 ... In fact, one of the major attacks on the Office 365 last year was launched by AI bots. We call that a knock-knock brute force attack where the AI bots are using NLP technologies to guess the email addresses of the executive admins. It's machines that are trying to profile the identities of users and trying to brute force them into your Office 365. And we see many of these attacks are being launched against Office 365. So investing in UBA to understand activities and monitoring and having a threat protection engine is another biggest use case. And to be able to, on Office 365, there are about 800 different activities that your users and admins can perform to be able to have rich audit trail of all the activities.
Srini: To be able to have rich audit trail of all the activities, so that you can help and talk incident response is another dominant use case. And last couple of one are more about while you want your employees to access Phillips 66 or your own corporate instance, you also want to be able to block access to the personal Office 365 instances. That's part of the governance of the health of your Office 365. The last but not last, and something comes up in rare occasions, is also providing an additional malware.
So are you're walking on the journey of your own Office 365, as Kurt said, start with getting the visibility, then provide the identity controls with, you know solutions like Okta, then solve some of the other use cases on securing your data and the usage with a CASB. Then, we talked about SaaS and Office 365 and other SaaS solutions. What about public clouds? So public cloud is one of the fastest in a growing segment right now. And we're all getting so much comfortable with the economics of, you whether it's Amazon or Azure or the Google Cloud. In fact, some of the organizations that I talk to, they're moving about 50 applications a day to AWS. On average, organizations have about 500 applications hosted on one of the public clouds. But the public clouds are probably even more difficult to secure, because you own a bigger responsibility in the public cloud compared to a SaaS. Here you are responsible for even the configuration. You just moved your data to a street, and if you don't secure those S3 buckets with the right read/write permissions, forget about all the DLP and all the security controls. So you have a bigger role to play in securing your applications and the data on public clouds.
So I'm going to share some of the other best practices on, as you are taking on the journey in AWS or Azure or the Google Cloud. The first and foremost layer of security is about doing a configuration and the privileged user audit. This is extremely, extremely important. There are CIS benchmark levels that you can use to measure the compliance, whether it's a level one or a level three, and this is extremely important use case. This is almost like locking your front door for your public cloud applications. Then the second one is either doing advanced UBA. You want to be able ingest all the CloudTrail logs to be able to make sure that you have the right user behaviors, or the admin behaviors, accessing your applications on these instances. The third one and the fourth one are things like, not only you have to do the UBA and provide the conditional access control, but you also want to be able to extend the same controls like you have in Office 365 to your own applications. Doing DLP on your S3 buckets. If you don't know what sensitive data is going into your S3 buckets, you may not provide the right level of security permissions.
Then there are a couple of other advanced use cases that we are seeing as you are using containers and so on, so forth, which is the container discovery and the micro segmentation and providing east-west network security controls. They're some of the advanced security use cases that you should consider, but these are the four that many of our customers are starting with. Starting with the configuration audit, and then providing the data controls and the UBA and the privileged user audit. So how do we bring it all together? I know we talked about a lot of use cases. For me, cloud security is so simple to start with. There are only three things that you need to focus on. Get visibility of all the cloud manifestations, whether they're shadow, sanctioned, or IAS, and start the governance process. The second one is secure your identity with a solution like Okta. And the third step, then get control and govern your usage of the data. So it comes down to three things: visibility, identity, data. That's how we can all get very secure in the cloud, and choosing a solution that's built for the cloud and in the cloud, like Okta and McAfee, is the right form factor for us to dig the germ in together. A couple of questions? So, if you are interested in talking to any one of us, taking a shadow ID audit or public cloud audit or Office 365, talk to any one of us and we can get started on a POC. So, Kurt, any other closing thoughts from you?
Kurt: I thought that was a great point you had there at the end around engaging with Sky-high to do the audit, to come in and do it. I think that's very eye-opening for a lot of corporations that haven't really looked into this space yet to see what are those services that are being used. It'll make you start questioning what you know about your operating environments.
Srini: Excellent. So we do have a couple of things. One is we have a raffle coming up, and we also have some time for Q & A. Any questions from anyone for Kurt or me?
Speaker 1: We do have a mic, so I'll be the running mic for you.
Kurt: There's one right there.
Speaker 1: So you don't have to repeat the question.
Speaker 2: Thank you. Thanks for your presentation today. Maybe more of a question for Kurt. As you were rolling out making this transformation and doing your roll out with the Okta and the McAfee/Sky-high integration, what were some of the technical or maybe feature/quality issues you may have encountered at a high level?
Kurt: Right. So, is that for more Okta or Sky-high, because we did it in two separate roll outs?
Speaker 2: My interest is probably a little bit more towards Okta.
Kurt: Towards Okta? So when we rolled that out around two years ago, we had developed entirely in-house SSOs. Being able to pull those apart, figure out how they were working, especially with some of our older legacy applications or more historic applications that we had, even within house, to be able to do that single sign-on, seemed to be a little bit of a challenge. But the Okta Professional Services were great in helping us take care of those issues that we experienced. Once we started getting into more of the cloud-based, standard applications, it was a breeze. That Okta application portfolio that they talked about at the keynote earlier is really streamlined to be able to tie your federation into that, get your old app information that you need, and then be able to get whatever customer or whatever service you're wanting to use federated nice and easily. So, I will say on one of the slides earlier we had standardization. The more standardized you can get with all these services, the easier all of this is going to be. Any customization we found that we had done previously in legacy environments presents challenges. So, the more standard you can get things out of the box, the easier all this integration becomes.
Speaker 1: Question back here.
Speaker 3: Quick question for you. So we use Okta. We integrate with SAML for tons of apps, right? So if you want to hook in Okta to use a CASB, do you have to rehook your apps that you already have federated through the CASB, in order for the traffic to flow through that way? Because I think that would be an issue, given the number of apps you have, right?
Kurt: So-
Srini: Go ahead.
Kurt: Thanks, Srini. We actually don't have them completely integrated together. Okta and Sky-high are not integrated together. We use the information that we're getting out of Sky-high to make the decisions on what are those services that we want to begin federating. But we are not using it at complete integration right now. I think Srini had something around that as well.
Srini: So we have many customers. One of the interesting things, or the valuable things about Okta and Sky-high is the CASBs directly hook into your Okta solution so that as soon as the authentication happens, the Okta SAML seamlessly redirects the user session to the CASB for the data control and the UBA and other use cases. So this is one of the benefits of how we can combine IAM and the CASB together, to get the complete security. Otherwise, the alternate choices are how do you route the traffic to a CASB? You have to either put an agent or you have to do very unnatural things that causes friction and that doesn't work across unmanaged devices and so on, so forth. So, one of the exciting things that we have done together is by this integration between Okta and Sky-high, so that in an IAM session seamlessly get redirected to the CASB for providing data use cases. And that works for Salesforce and some of these other applications, or the applications that you develop on your own that you host on public clouds.
Kurt: And that integration is on our roadmap.
Srini: Then there are a couple of other integration points that we also built. We can also ingest the logs from Okta to provide a more advanced UBA level. Because at the end of the day, you need to bring all these different insights, from the Okta and the CASB, so that you get the richer insights to detect advanced threats and so on, so forth. So that's also another integration to be built using our CASB Connect, and that's also something for you to do.
Speaker 3: That's what we use the SAML, and we test on the last possible. So, it sounds like the same thing.
Srini: That's the ultimate place where you're going to do all the correlation, and there are some other insights that we can provide and then we can also feed that to your SAML. Any other questions?
Speaker 1: One back here.
Speaker 4: Thanks for this presentation. I can understand that the company we're talking about here is rather huge. Do you think this set of solutions is also eligible and relevant to small-size companies?
Kurt: Yeah, you know, I wouldn't call us huge. We are large in the sense of assets, but as far as employee base, we're still under the 15,000 mark. So as far as those massive 100,000 people companies, we're not at that size. So yes, I think that there are solutions that McAfee and Sky-high can offer to the smaller businesses, to those enterprises, to be able to get a grip on what is being used in your separate business units.
Srini: And the interesting thing is, if you look at the cloud, cloud is the greatest equalizer force across small and big corporations. It doesn't really matter whether you're ... Office 365, whether you're a small customer or a large customer. So that's one of the decisions that you need to make in choosing a partner to work with, whether they're cloud-native. So if the solution is built like an appliance or some other extensive, requires a lot of professional services, then that may not work for smaller organizations. Any cloud-native solutions, like Okta or McAfee, can easily scale and provide that frictionless user experience. So, if you want to take on the journey with us, please join us, and we'll be glad to help you on some of these use cases. Any other questions?
Speaker 1: Questions? Oh, right here.
Speaker 5: How does Sky-high determine whether an old device is trusted or is a personally-assigned device?
Srini: So that's a good question. One of the use cases that we talked about was on the contextual access control for in-office facing to the public clouds. So the question is about how do you determine the context of whether there is a corporate device or an unmanaged device? So there are many different ways, but the most widely used one is relying on your device identity. It could be like a certification that you provision on your PCs or on the mobile devices if you have an MDM that also presents a certificate. So relying on the time of the authentication process, you don't need to be a full agent out on the traffic, but just at the closed-session level, you should be able to figure out the identity of the device based on whether it's presenting a proper certificate or not. So that's probably the most widely used. There are other different means, but that's what I recommend that you rely on. It seamlessly plugs into your existing mechanism for both PCs and the endpoints.
Speaker 5: Well, thank you very much.
Speaker 1: We're going to close our session now. Just a final reminder to fill out your surveys, drop them off back here on the table. We do have extras if you did not get one. There's a chance to win a $100 Amazon-
Srini: Kurt, thank you so much.
Kurt: Thank you.
Srini: And thank you for sharing the journey, and thank you all.
As a 100 year old company, Phillips 66 is leveraging cloud to accelerate their business and drive competitive advantage for the future. But with stringent security and compliance requirements, they’ve had to build a modern security stack to standardize their IT offerings in the cloud and protect their data. In this session, Kurt Haberstroh of Phillips 66 and Srini Gurrapu of McAfee, will pop the hood and show you how an integrated IAM + CASB approach supports data security requirements around access management and cloud usage for both SaaS and IaaS.