Oktane19: The Power of Identity: Delivering End-to-End Identity Access, Governance, and Security
Transcript
Details
Collin Perry: We're talking about The Power of Identity2. And I'm certainly excited to be here. My name is Collin Perry. I lead our SaaS solution group at SailPoint. And joining me is Fiona Cullen all the way from Australia who's going to share her story about using the joint SailPoint and Okta Solutions.
Collin Perry: Today, I know a lot of people that I've spoken to at the show so far have asked me, "Hey, Collin, can you tell me a little bit more about identity governance? How does this fit with Okta? How does it complement everything that we do in Okta today?" And so we're going to spend a good amount of time here at the intro as I kick things off giving you guys a bit of an overview of what identity governance is all about. And then from there, I'll talk a little bit about the solution, some of the key capabilities that SailPoint brings in combination with Okta as well as show you a few screens on the products that it really hits home and hopefully, you guys leave here feeling like you're masters of identity governance. We'll talk about the benefits of the combined solution.
Collin Perry: And then I'll bring Fiona up. And she'll actually share her story of her identity program and everything that she did around initial exploration, discovery, and leading up into her project, and some of the steps along her journey. Lastly, we'll open up for Q&A. But as we kick things off, I'll just open up with a quick commercial.
Commercial: The world's top enterprises are struggling with the same dilemma, how to unify, manage, and automate identity access, security, and governance across a sprawling hybrid IT environment. IT has never been more complex. With the mix of on premises, cloud, and hybrid applications accessed by employees, partners, contractors, and suppliers; providing easy yet secure user access and governance poses a major challenge especially in highly regulated industries. That's why we're excited about The Power of Identity2 in integrated end-to-end identity access and governance solution.
Commercial: The combination of Okta, the leader in identity and access management, with SailPoint, the leader in identity governance, provides enterprise, organizations an end-to-end, best in class, fully integrated solution. Our combined solution is tried and tested to securely and easily govern all users' application and data access throughout the entire user life cycle.
Commercial: Enforced access with single sign-on and adaptive multifactor authentication providing employees simple, secure access enable comprehensive control and visibility of who has access to what from identities, to accounts, to entitlements maintaining a secure user experience; grant and maintain secure access according to established business policies and forcing compliance requirements, and improved productivity while reducing overall IT costs by automating time intensive processes such as onboarding, password resets, and access requests.
Commercial: See why some of the world's leading businesses are turning to Okta and SailPoint to mitigate the risk of a security breach and enforce compliance policies. Visit us online to get started today.
Collin Perry: All right. It doesn't beat that. Tough act to follow here, so see what I can do. I guess just to kick things off, I'll tell you a little bit about identity governance. I thought I'd open with a personal story about my journey in this space and the origin story of identity governance as an industry.
Collin Perry: When I started my career 20 years ago in identity, I was doing consulting for a Big Four firm and really I spent my time out at clients deploying identity solutions of the day focused on automating access, provisioning as we called it at the space at that time. And I worked with a lot of different organizations. And it was great. I really enjoyed that. But unfortunately, shortly following the beginning of my career, we had the WorldCom, Enron scandals, and all the internal control issues that they had. Many of you can relate to this story. But as a result of that, anyone at that time that could spell security all of a sudden had to become an auditor. So I found myself all of a sudden becoming an auditor. Please hold your boos until after the presentation.
Collin Perry: And so at that time, one of my first clients was one of the largest tech companies in the world. And I went out there. Being an identity guy, I thought, "Hey, this is pretty straightforward. Let me pull HR data. Let me look at all the people that have left the company over the last five, ten years. And then let me pull information, and accounts, and access from all these key financial systems and cross reference these lists." And I was intrigued at the time. Having worked in automation space of ... I wonder what I'm going to find? And what I found was that active directory was relatively clean. But I found thousands of people that had left the company that still had access across the other 85 key financial systems that they had at the time, mainframes, directories, databases, platforms, all across the whole space.
Collin Perry: We dug further. We found people who had actually left the company had actually logged in after their employment was ended, access order systems, pricing systems, all kinds of other systems. From an auditor point of view, it was like the ultimate find, right? I was like, "Wow, this the greatest thing ever." But then reality set in. And I was like, "Well, this is actually going to not go over well at all with this account." And sure enough, I found myself in a meeting with the CFO and the CIO essentially in a screaming match about whose fault this was. And in reality, really how the dialogue went was the CFO saying, "Hey, look CIO. These are IT systems. These are 100% your fault. These are IT systems. And this is your responsibility." And CIO's point was, "Hey, look. We have 200,000 people that work at this company. How do I know every single person in finance, in accounting and who these people are and what access they should have across SAP and Orkly business and all these other systems."
Collin Perry: So in reality, both people had a great perspective on this. Both people were accurate in their assessment. But the reality was that they needed to have a way to empower a manager in accounting and finance and these non-technical positions to be able to actually see what their people had access to across systems. And without that visibility, how can those people truly be accountable for what their people have access to? That was really the origin of identity governance.
Collin Perry: Following that, SailPoint was born. And this is really what this industry is all about. It's all about understanding who currently has access across the organization. And not just understanding that access, that visibility to access just for the sake of IT and all of us in the room, having that visibility; but really then empowering managers and business unit owners and app owners to have that visibility so that they can answer the next question which is really, who should have access? Because these people understand. They have the context. They know who these people are, what job they're doing, and what access that they should have. And then lastly, how is that access being used? Is it being used appropriately? And then being able to take action on that.
Collin Perry: When we begin one of these deployments, we start with this concept of building an identity queue. And really at the origin of this, and a lot of you I think can relate to this from an Okta story, where what we do is we start with this concept of bringing in all kinds of different authoritative sources. So this is going to be one or many HR systems. And typically in a client, this is going to be your HR, your payroll system, your recruiting system. It could be a contractor system as well. A lot of times if there's been a lot of M&A in the organization, it may be 10, 20 different HR systems across all kinds of things, cloud, on-prem, others.
Collin Perry: This gives us the context about who these people are not just their name but also their department, their building, their location, their job function. This stuff is very actionable from an identity point of view. And combined with the second step which is really bringing in all the account and access information from all your on-prem applications, all your cloud applications as well as data looking at who has access to files and shares across the organization. And correlating that back to the identity, we can fill identity cube up with all the context about who these people are and what do they have access to across the business.
Collin Perry: Now, some of you are probably thinking, "Well, hey, what about accounts like root or admin or test123? How do those accounts get correlated?" Well, those accounts, we govern those as well. And that's a really critical piece of this. Typically in that first step and this loading and linking process, we're going to find that we'll maybe hit 80% or 90% correlation. But we'll have a good set of accounts that are these service accounts, application accounts, generic accounts. Ideally, we plug a PAM solution in here to govern some of those admin accounts. But we're going to still govern every single one of those accounts and understand who owns it. And this is going to help us alleviate a lot of the other breaches that we've seen in the industry across retail and higher ed and financial services where one of these accounts was used to breach the organization just because we simply didn't know whether it was appropriate or not. And then with all this information, we can then go and do everything else we do in the solution.
Collin Perry: So at SailPoint, we have an open identity platform. We talk about a number of different services that layer on top of this. And very important, at SailPoint, we're very SaaS focus. So just like Okta, multi-tenet microservice SaaS solution built from the ground up as pure SaaS. This is a big differentiator for us in the industry right now. We layer on all these different services that allow to do a wealth of different things within the solution. In order to show you this, in fact at the bottom of the screen, I'll just mention, from a connectivity point of view, when we talk about integrating with applications, we're not just focused on key financial systems as I mentioned earlier, but key operational systems, high risk systems. Really, some of our large organizations have integrated with thousands of systems. And they're a wealth of things from on-prem, to Cloud, and everything in between. Same thing from a data storage point of view, cloud data storage as well as on-prem as well.
Collin Perry: Now, looking at this and the solution, I wanted to give you guys a bit of a view of what this actually looks like and how it manifests in the solution. Of course, we have the Okta dashboard up here, not the SailPoint solution. But I bring this up to illustrate from the Okta dashboard, we can have tiles that show, "Hey, you requested this additional access." So if the user wants to come in and request some more access on top of what has already been provisioned from a birthright point of view, they can do that. They can come in here and review their people's access, so have a tile for doing that. And even if you're an admin within the organization, you'll be able to go in and access a lot of our great analytics.
Collin Perry: To showcase some of this, I thought we'd first start with some of the analytics on the back end. So a lot of you guys, once you've loaded and built all these identity cubes, you have at your fingertips a full elastic search engine that essentially lets you query anything within your environment. For example, of course with live demos, this is the joys of that. Let me see if my connectivity is still alive here. We could come in and do a search of just a keyword like, "Hey, show me anything related to accounting." Of course, we index all data that we've built across all systems. In this case, I can bring back every identity related to accounting. I can drill into identity cubes and see all this information. I can see all my access, my SAP roles, my AD groups, my IDMI, my Salesforce roles and profiles, all my Fine Grain access across these different systems.
Collin Perry: But I can start doing a lot more elaborate queries like, "Show me everyone that works here today that's active that has access to privileged accounts. Or show me everyone that doesn't work here anymore that's still has an account on some system." Or any kind of other query that I want to do. And then schedule a certification, actually do a review of these people and clean up any data sets that actually need attention by one of the different business unit owners.
Collin Perry: So that point, this concept of an access review to showcase the same type of search functionality. But I was describing at the beginning of this explanation of the CIO, the CFO, the struggle, right? I want to be able to provide managers views like this where a manager can come in and see a person and review their access across all kinds of different systems, being able to approve and revoke that access. And through our deep integration with Okta, actually bring back all the Okta accounts and groups in a two-way integration model to be able to showcase to all these people exactly what they have access to within Okta as well. And on the access side of things, we're showcasing not only the entitlement, but a business-friendly description of what does this access allow you to do within the organization.
Collin Perry: Now, we'll talk a little bit more about life cycle in a little bit. But in combination with life cycle and working in combination with Okta's life cycle, we can do and we can make sure everyone has all the access they need through an onboarding, through a transfer, through a termination, a pre-hire, all these different paradigms from a life cycle management point of view. But there's always a need for people to request more access. And so from the Okta dashboard, they can request more access right here into the SailPoint request interface. They can see all the catalog of systems across cloud and on-prem that they want to request access to. I might want to request more SAP access. And in doing that, I'm not going to just list out 30,000 SAP roles for someone to choose from, but rather, in SailPoint we're modeling that access down to the SAP role or down to the actual deep access model.
Collin Perry: But then when we manifest it in a request UI, we do it in a business-friendly way so that people understand what they're requesting and what that access really means. After this, we go through an approval workflow, whatever is needed for individual things that they're requesting, and then of course, go and fulfill that access on the downstream systems.
Collin Perry: So just a quick commercial on SailPoint. I've been with the company for about 11 years. And in that time, we've grown substantially. Now, we have over 1,200 customers. Initially, 11, 12 years ago, we focused on the heavily regulated industries initially. Those were really the first adopters of identity governance much in the wake of all these internal control issues that we saw in the industry. But nowadays, organizations all the way down to 100 users or even in some cases, less than that, all the way up to the most massive and large companies in the world are adopting identity governance. I'd say is another big difference right are our mission, our investment in SaaS, right? This has been a key focus for us and something that we continue to see very very rapid adoption of.
Collin Perry: Now, on the integration and why we partnered with Okta, this is somewhat of a no-brainer. We have so many customers, joint customers in fact, that after many years of having so many joint customers, customers just told us, "Hey, guys, why are you not combining forces and building a tight integration between this," because I mean you can't have one conversation without the other. You got to have these two things combined. And of course, we've both been a market leaders for a number of years. It just makes perfect sense. And both companies have invested greatly from a product and engineering point of view to really bring together this joint solution.
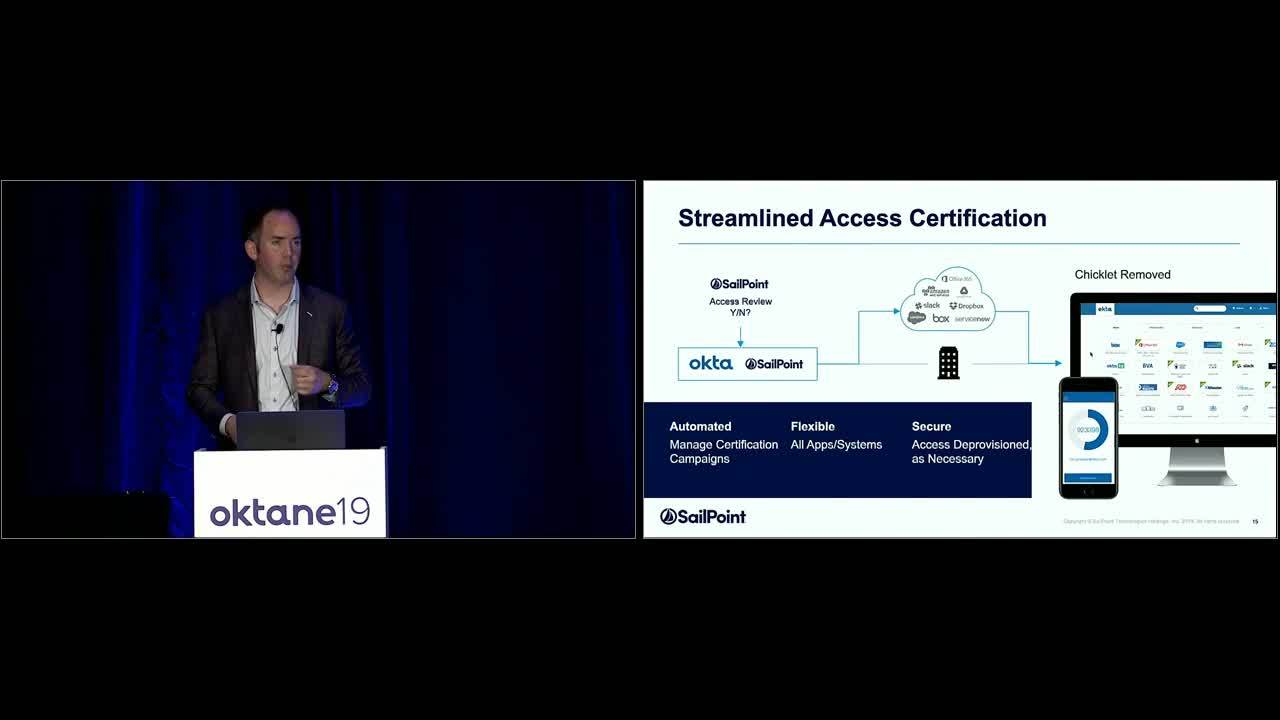
Collin Perry: I did want to mention ... You saw the marketing promo video, this partnership is not just about marketing and a bunch of videos and stuff. We actually have a deep connector and integration that allows us to interface via Okta's API to the back end accounts and group model, and interact with that, and really layer in a full governance model on top of that. And this is really where the magic begins because when you think of Okta connecting everything, and really showcasing for an end user, and being that end user experience; when you combine that with everything that we do on the back end governance side of things, this is really a perfect combination. And we layer in the capabilities. You have all the SSO, MFA, the B2C, the password reset side of things on Okta, all the governance access request certification, separation of duties, and then full life cycle management that's really delivered by the joint solution combining our life cycle capabilities to provide that full end and governance life cycle and single sign on.
Collin Perry: So I thought I'd conclude here with a couple use cases. The first is really this concept of a system of record coming into the joint SailPoint-Okta solution, and then fulfilling and provisioning all the access people need for their day one on the job. This is really really important. We're doing a lot of really new things in this space. Importantly, I'd just mention a couple details on this. First of all, the system of record could be workday, could be SAPHR, Oracle PeopleSoft, could be any number of HR systems large or small. Also, we find a lot of organizations maybe built their own HR system, maybe it's on a mainframe even. No problem, right? We interact with all those different HR systems. We bring in those identities. We can even interact with a recruiting system to get into a pre-hire type paradigm.
Collin Perry: And in combination with Okta, have a really sleek user experience, so people completing their security awareness training, background check via the Okta dashboard ahead of starting at the company, and then go through all the other provisioning operations we need to do to create all their cloud access that they need as well as all their on-prem access across mainframes and directories and databases etc. And then of course, day one, they can come in. They can set their own password. They can get secure access and see exactly what they have access to via the Okta dashboard, and of course, layer in adaptive MFA so that they have that strong authentication paradigm happening as well.
Collin Perry: The second use case is really all about requesting access as I showed you. So the user can come in. They can go through the flow. On their Okta dashboard, if you choose to give this function to someone, they can go and have access to the request catalog and SailPoint. Now, a lot of organizations choose to do that through ServiceNow which is fantastic. We have a deep integration with ServiceNow as well. So you can use essentially what we call our request catalog integration of ServiceNow, so via API. You can have it in the ServiceNow surface of a full request catalog at your fingertips as well. Again, full approval workflow, and then the ability to fulfill all that access across different systems not just via connectors, and not just using a combination of SailPoint and Okta connectivity, but also being able to create tickets in ServiceNow for manual fulfillment in some systems, cases, or doing other type of manual operations.
Collin Perry: And then lastly, this review concept, probably the most important internal control in any organization these days. And I thoroughly believe that because at the end of the day, if you can provide that visibility to a manager or any individual in the organization to see what their people have access to, it is literally the catchall control, right? It will catch separation of duty issues. It will catch people that have accumulated access over time. It will catch service accounts that people shouldn't have access to. It will catch people that have access to CyberArk or PAM accounts that they shouldn't have anymore. Not just in IT, but maybe it's access to the corporate Twitter account that is managed. And maybe they've moved away from marketing, they moved into finance for example. So all those types of issues are captured within this review process. And fundamentally, it's just a fantastic data cleanup process that will allow the organization to really remove a lot of access from users.
Collin Perry: So with that quick intro, I'm going to pass it over to Fiona and have her tell us about her journey at Orora group. Thank you.
Fiona Cullen: Thank you. Thank you, Collin. Good afternoon. My name is Fiona Cullen. I am the IT service manager for identity and access management at the Orora Group. I've been with Orora for four years now. I'm based in Melbourne, Australia. And my background is predominantly SAP application, security, and compliance. Prior to this role, I was based in London and working with IBM and Shell doing global SAP rollouts. So that's put me in a good position for this position in identity.
Fiona Cullen: So just to explain a little bit about the Orora Group. We're a manufacturing company producing packaging and visual communications solutions. Some of the products that we manufacture include glass bottles, aluminum cans, closure and caps for bottles and cans, flexible packaging, recycling paper, boxes and cartons, and point of purchase displays. Orora at a glance. So Orora has a presence in seven countries with around 6,800 team members and 54,000 shareholders. The main presence is in Australia, New Zealand, and the United States. But we also have operations in Mexico, Canada, the UK, and China. We have 43 manufacturing plants as well as 91 distribution sites.
Fiona Cullen: So just moving on to explain a little bit further about the Orora Australasia business. We have two major businesses, the beverage business group and the fiber business group. Our beverage group is divided into three divisions. So it's the manufacturing of aluminum cans as well as glass bottles. We produce over a billion glass bottles each year as well as cans enclosures, wine and plastic caps enclosures for leading beverage companies such as Coca Cola. Our fiber business is divided into three divisions. So we provide packaging solutions for the food, beverage, and industrial manufacturers. We produce recycled paper carton board with over 400,000 tons produced at our world-class paper mill each year in Sydney. And then packaging and distribution. So we produce custom-printed cartons, bags, and sacks for boxes and industrial packaging consumables.
Fiona Cullen: The Orora North America business consists of two business groups, Orora packaging solution which is a market leader in customized packaging and supply chain optimization serving diverse customers in the food, beverage, technology, healthcare, automotive, industrial, and agricultural markets. And then we have Orora Visual which is an innovative leader in the U.S. point of purchase and visual communications market.
Fiona Cullen: So moving on to our identity journey at Orora and the why, why we partnered with SailPoint and Okta. Orora faces many of the challenges that you're probably all too familiar with. We have multiple user accounts across multiple systems. How many? We don't know yet. We've got almost 600 IT systems. We've got a history of relaxed security control. So over 9,000 user IDs with only 6,800 employees and team members. So John who might've been with the business for the ten years has had four different roles. He's retained all of his access for all of those roles across each transfer. Then Mary comes along and her account is copied from John. So it just goes on and on and on.
Fiona Cullen: So we also have 4,000 calls to our service desk each year for password resets. We've got an incomplete termination process. It's extremely manual reliant on people to raise forms, to remember to raise forms. It's a complex process and only covers a selection of applications. So it's very incomplete. In Orora Australasia, we have ERP systems. And we do require governance and controls for all of those systems. But it's very difficult to implement manual processes around those. We've got account administration being handled by people who've got 25+ years of experience. And we also have a very slow onboarding process. So that's something that ultimately does frustrates hiring managers and end users as well.
Fiona Cullen: Some of our drivers for our identity project would be ... We're embarking upon a digital transformation program at Orora Australasia. So we want identity governance and access management to build a foundation for the new technology landscape. We wanted a platform agnostics solution that will embed access management and governance from the very beginning. And the business also wants this. Each year, we conduct an IT customer satisfaction survey. And one of the main things that comes is the dissatisfaction with the access request process, how long it takes, how people don't know what to request. And one of the main things that we see coming up is that people just want to be able to get the access for their job. So whether it's a job catalog or whether it's HR driven positioned based access, this is what the business wants. So we're listening.
Fiona Cullen: And we also want to reassign those skilled resources out of account administration and supporting our digital transformation with value add tasks. So in terms of the business case and selling the value of identity, and access management, and governance, the one thing that I really focused on at Orora was making it about the business. Nobody likes passwords including your CEO or executive sponsors. So when you're selling something like password self-service or single sign on, it really does make sense. We also highlighted the fact that this technology empowers end users and increases productivity. And one key thing that really struck a chord was using the HR system as a master data source. So we've recently implemented SAP SuccessFactors globally. And that was a fantastic starting point. It made a lot of sense to everybody involved in this project that we are going to be using the HR system as a source.
Fiona Cullen: I also highlighted the amount of time that's manually spent on processes such as account administration and manual controls as well. So Collin mentioned user access reviews. And if we just take in our case SAP for example, every quarter, we're spending probably about two weeks worth of effort to gather spreadsheets together, send them out, email, and try and make sense of some of those. And in some cases, it's even handwritten. So that was one of the key things that really appealed to us the IdentityNow product.
Fiona Cullen: So in terms of cost, obviously we need to mention that. In a business case, the increased efficiency saves money. And also increased visibility of users saves money as well. So we're no longer going to be paying license fees for those people who left ten years ago. And one thing that I did with the business case was I packaged access management and governance together. I didn't separate them in terms of functionality because for me, you can't really have one without the other. So putting that together in the same business case really made sense rather than requesting one portion then going back later to ask for more funding for another. So to me, it was just one solution.
Fiona Cullen: In terms of product selection, we did look at Microsoft Azure ID, obviously Okta and SailPoint IdentityNow, and SAP GSC Access Control. We conducted a really successful proof of concept last year with Okta and SailPoint. We connected some of our key applications such as SAP, ServiceNow, Active Directory, and our newly implemented SuccessFactors HR system. We did in fact request a proof of concept with Microsoft Azure ID, but we were told that that was going to take us 12-16 weeks to configure and with less application scope as well. So we had Okta and IdentityNow set up in two days, and that made our final product selection process really easy.
Fiona Cullen: A business wants scalable solutions, automation, and visibility of everything. And Okta and SailPoint offers that. User access reviews are integral for our business. IdentityNow provides this solution through the access certification tool. Just last week, we had one of our audits. We do have many. And there were an additional ten systems added to the scope, just came from nowhere. So I've already got application owners asking me if we can connect their systems to SailPoint for the user access reviews. And that's before we've even gone live.
Fiona Cullen: So Orora Australasia has IT principles that include cloud first and buy not build. So that was why we went with these cloud based solutions. And I have to say we just received the most fantastic service from Okta and SailPoint during the entire journey. No question went unanswered. And I had many questions.
Fiona Cullen: So the journey from here. We are in implementation mode at the moment. We've got our preview systems or sandbox systems up and running. We've connected to Active Directory, to SuccessFactors as well. We set up a couple of applications for single sign-on. And it's really incredible how rapidly that can progress. It's very very exciting. So we've got our first go live in May which will include single sign-on and multifactor authentication for a number of our key cloud applications as well as password management, and synchronization, and connecting to our HR master source. Then we have phase roll outs through to the end of July which will include ... We use the provisioning process, user access reviews as well as single sign on for SAP. And once we've gathered all of our information, we can then start to correlate accounts and really get rid of those orphaned accounts that are no longer required.
Fiona Cullen: And I have to say that we're very excited. It's the first IT project that I've seen at my time at Orora that everybody's excited no matter what area of IT that they work in. They've been involved with workshops and demonstrations and are very excited about what's to come. And with that, thank you. And any questions?
Moderator: We have a question here.
Speaker 5: Hi, you mentioned integrating with multiple ERPs and I assume many are legacy. And I want to know about ... Do you layer IdentityNow on top of the existing roles? Or was this also in contrary with the role cleanup within the ERPs?
Fiona Cullen: It definitely does need to be some role cleanup. I think we're going to probably start with cleanup of birthright access so we can get up and running and get people started with the basics. And then because we are embarking on this transformation project, we don't know how much longer we'll have our existing ERP systems for. It could be replaced with SAP. So we have to take all of that into consideration and weigh up whether we spend six months cleaning up our roles or whether we just start with the birthright access and then wait and see what happens with the transformation.
Moderator: Question?
Speaker 6: Yeah, so we're currently on the beginning of this journey. We've had some small successes implementing Microsoft Identity Manager, some custom coding stuff to do some of this stuff. And we're looking at taking it to the next level. We have a lot of custom stuff like AS400, ERP custom applications that are homegrown, things like that as well as a lot of active directory distribution groups that are managed based on attributes from HR and active directory. Wondering if you guys had a similar experience with that stuff? And on the way to getting into SailPoint and Okta, what you guys did to overcome some of that stuff and get that more integrated into the identity platform.
Fiona Cullen: Well, I think for now, we're just starting with key applications. And like I said, we're going for the digital transformation process. So a lot of those legacy systems maybe replaced in the future. But we're just focusing mainly on the financial ERP systems at the moment.
Speaker 6: Gotcha.
Collin Perry: I'll add another because you're transitioning. So we do find Microsoft Identity Manager in place in a lot of places. It's extremely pervasive. Probably, if we did a show of hands there's probably half the room has used MIM in some way or FIM. Certainly, MIM for AD or some basic use cases, it can accomplish some of those things. But especially given the fact that that product has had so little evolution or so little advancement over the last ten years even. I would argue, investment there, I'd put at a very minimal level. And especially for advance use cases, a lot of those things are custom within MIM. And so I would really caution or look to some of the combined solutions. So ...
Collin Perry: Yeah, custom ERP. That's what your-
Speaker 6: We have a very custom ERP system that's very specific to the equipment renal industry.
Collin Perry: Okay.
Speaker 6: So it's called WIN. I'm sure no one in this room has ever heard of it. But it runs on an AS400, and it's going to be some sort of custom API integration and provision into that system which MIM can't do today. So that process of managing our ERP is still all manual. We have three guys that that's all they do all day is provision into that system.
Collin Perry: Feel free to come up afterwards because AS400 IDMI is really common platform for us to integrate with and applications running on top. So happy to talk you through that. Thank you.
Speaker 7: So you're in the middle of ... I'm right here.
Fiona Cullen: The bright lights, I can't see.
Speaker 7: So you're in the middle of implementing this now, correct?
Fiona Cullen: We're just starting now. So we've connected our sandbox systems and in the process of getting started with the production system. So we're just getting started.
Speaker 7: How are you managing the change specifically with your source of truth assuming it is your HR system?
Fiona Cullen: Well, once we do integrate and fall all those identities in, then we need to obviously correlate accounts. And we will use the SailPoint IdentityNow access certification process to weed out all of those user accounts that are not recognized anymore.
Speaker 7: But specifically, are you allowing your HR department? Because we're at the same threshold where you are right now during implementation, same products. Are you allowing your HR department to enable accounts and de-provision accounts?
Fiona Cullen: The HR department? No.
Speaker 7: Okay. So as an employee ... Okay. And also, how do you deal with contractors?
Fiona Cullen: Good question. So our contractors are not currently in our SuccessFactors HR system. So they will be in that system probably in January next year. So at the moment, we just have to deal with user access reviews to try and establish who all of the current contractors are. And then once we're very rigorous with the access certification, hopefully, we can manage contractors that way. But currently, they're not included in our HR system but will in the future.
Speaker 7: Will you be doing the flat-file upload.
Fiona Cullen: Yup. We maintain contractors in ServiceNow. And we'll be doing the flat-file upload.
Speaker 8: I heard you say that you guys are going to clean up some of your birthright roles. Can you talk about some of the debates you had when you were trying to figure out what you were committed to cleaning up with your roles?
Fiona Cullen: So we haven't really started the role cleanup process as yet. But we will be doing that over the coming months. But we have to work with the business to establish what people need on day one to get started. And then we'll have some people like business analysts who work directly with the business to start building up those enterprise based roles.
Speaker 8: The process of determining that you will do the roles later, how did you lead to that?
Fiona Cullen: Well, we'll do it concurrently. We already have some birthright access setup in the systems anywyay. So we're going to start with that. And then concurrently, we'll develop that further.
Speaker 9: My question is directed more towards the integration between SailPoint and Okta. So when you aggregate from Okta the accounts, what do you bring as entitlements into SailPoint? Is it the groups? Is it the apps on Okta? So that's one. And the second one is so for some applications, Okta might be able to handle the user access and management on those applications. For example, SalesForce, right? So Okta can provision accounts with the specific permissions and roles onto SalesForce whereas SailPoint can do the same. So what are your recommendations in that case? How do you provision? Or what's the best practice that you'd recommend to provision accounts onto this? And finally, is there parity between IdentityNow and IdentityIQ with respect to the Okta integration?
Collin Perry: Fiona, do you want me to take this one?
Fiona Cullen: Yes, please.
Collin Perry: If you want to take a crack at the three-part question, feel free to ... No, I'll talk about it. So the first part of your question is ... So the connector we wrote integrates for you the Okta API, and it brings back accounts. And then it brings back the Okta groups as well as technically we're bringing back the entitlement model of apps on dashboards as well. So we do get down to that layer. Now, this is a constantly evolving integration, so we're looking to get deeper and do even more fancy integrations. But it's two-way integration at that level of objects that we're interacting with on the end system, right? So that's the first part of your question.
Collin Perry: The second part on what's the right approach from a life cycle point of view? It really depends. So we wrote an integration whitepaper about this. But essentially, the net of it is because we have the ability to instrument change in Okta and we could leverage all of Okta's connectivity in combination with SailPoint's connectivity, in SailPoint typically we define life cycle states. And then we also define roles. And we have a multilevel construct with roles as well. And so that allows us to set up a governance foundation of what people should have access to, but then track that from how they got the access, and what the approval model was from a request point of view, and all those kinds of paradigms. Now, that's in combination with Okta's LCM. So if Okta's got some really cool connectivity downstream for different types of things, you get the power of both using the joint solution. And it's all done through that integration. So it's a tight integration tracking everything and making sure that everything goes exactly the way you want it.
Collin Perry: Technically speaking, I need to give you one more data point since you sound like you're a technical individual is that you actually really have two layers of security as well because in SailPoint, we're controlling Fine Grain to access on the end system and really controlling. Should we disable it? Should we delete it? Does it support a lock unlock construct? All kinds of other types of operations. But in addition, we're also controlling tiles on the Okta dashboard and in combination with Okta policy and everything on that. So the nice thing is you actually control both paradigms, so the authentication paradigm as well as the access paradigm from a SailPoint perspective.
Collin Perry: And then your last question on IdentityNow and IdentityIQ from a functional parity point of view. So just for everyone's benefit because a lot of people may not understand that question. At SailPoint we have two core platforms. We called a platform called IdentityIQ which is a traditional software solution. It can be provided in the cloud as a hosted solution or on-prem. You can manage it yourself or put it up in your own cloud. And then we have IdentityNow which is a true multi-tenet microservice SaaS solution.
Collin Perry: They both solve the same paradigms from a business problem point of view. But they're really designed for two distinctly different organizations and makeups. A lot of organizations that favor the on-rails, we want the solution to tell us best practices, and I want to be able to operate with maybe a lower TCO and more configuration, less customization; that's IdentityNow.
Collin Perry: And then IdentityIQ has got a little bit more horsepower as far as more customization and more ability to configure because as a hosted solution, you have that configuration. So there's pros and cons in both. But we find that really 99% of the time, an organization is a perfect fit for one or the other. There's not a lot of competition or overlap from that perspective. So they solve the same problems. But when you look at the solutions, they're not the same at all. And they're not designed to be the same. So I can go to a much greater depth if you want at another.
Speaker 9: The Okta integration.
Collin Perry: Oh okay. The Okta integration. Sorry yeah. So maybe I didn't answer the question properly then. My apologies. The integration is exactly the same. In fact, both platforms use the exact same connectivity layer. So they both have that same Okta connector. Yup. Thank you.
Moderator: I think we have time for just one more question before we wrap up the session.
Speaker 10: This is a combined question. You mentioned contractor IDs. This is more for SailPoint. What do you find the industry is doing to manage contractor IDs because of many organizations of course as your client mentioned that you're storing an HR system. Are they moving towards more of course using a directory like Okta? Or are they storing the contractor IDs outside? And then how are you handling the conversion process?
Collin Perry: Yeah. I don't know if you wanted to ... But yeah, so I mean in SailPoint, we have a contractor management module. And we find it's very common. It's 50% of conversations or something. People don't have a contractor management solution today. There are solutions off the shelves certainly. And some organizations do use that. But there's a mass amount of organizations that haven't found a great solution. So we have a contractor management module that essentially allows you to manage that whole paradigm. I would say it can work in concert with Okta. But really in SailPoint, we have the ability to create an identity, manage, and all the different attributes you want to manage, go through an approval workflow, have certain people in the organization be able to create the contractors if you want to allow them to do that. Still go through HR so that can be part of that process and see that contractor being created.
Collin Perry: And then to your question on merging and what happens in that contractor life cycle, there's a lot of paradigms there. Sunrise, sunset, temporary work type scenarios is all accounted for. We see that very heavily in the healthcare space especially with nurses and stuff that come in that maybe work for two days, then they leave. So we need to terminate them. But then they come back. Next week, they work for another two days. So we handle all those paradigms. And if they become a full-time employee at some point, that concept of the identity queue I've described in my presentation, we can merge that contractor. Essentially, they have a cube. They're going to change their cube into an employee cube. And then we handle that paradigm.
Collin Perry: The nice thing about the integration is we can then make that work very seamless with Okta so that as their access needs to change or maybe they're allowed to do different things, or maybe they're required to go through more pre-reqs like a security awareness training or a background check or some sort of safety training before they can really get access to their employee access, you can instrument all that type of flow through the combined integration as well, so a lot of advanced use cases there.
Moderator: With that, we will need to wrap up the Q&A. So thanks to our speakers. And thank you to all the attendees for the engaging discussion.
Collin Perry: Thank you.
Today’s modern enterprise leaves IT professionals wondering how to empower users while securing their application access. To help ensure a secure and compliant environment, organizations are looking to harness the power of an identity platform to better enable users and govern access to all applications and data across their hybrid IT infrastructure. Attend this session and learn how integrating Okta Identity Cloud with SailPoint Identity Governance, will ensure your organization can securely and effectively authenticate, provision, and govern access to all applications and data across the hybrid cloud and on-premises enterprise.