The Production Line: The LDAP Interface
For our third edition of The Production Line, we’re looking at something old, made new again with the LDAP Interface. In essence, it’s a hybrid IT game changer. If this sounds like hyperbole, note this customer quote: “[with the LDAP interface] we could finally get rid of our Lotus Notes server.” And although it spent some time cooking in Early Availability (EA), it’s now out in Generally Availability (GA) with a host of new benefits under its hood that you may not know about.
What is the LDAP Interface?
Before the introduction of the Okta LDAP Interface, organizations using LDAP or Active Directory (AD) servers relied on the Okta LDAP agent to authenticate users against their on-premises directory. This was great for maintaining a hybrid environment, but still forced organizations to keep one foot in the on-premises world. The LDAP interface allows orgs to migrate certain apps off of legacy LDAP or AD servers and onto Okta—for a full-cloud experience.
Under the hood, the LDAP Interface is a cloud proxy that consumes LDAP commands and translates them to Okta API calls, providing a straightforward path to authenticate legacy LDAP apps in the cloud. It allows every LDAP resource (policies, users, or apps) to be centralized and managed within Okta. It even provides an extra layer of security by adding seamless MFA to your LDAP apps with Okta Verify Push and TOTP. Essentially, you can drop your LDAP agent and connect LDAP apps to Okta Universal Directory without installing and maintaining your LDAP servers.
Authentication + app agnostic
The LDAP protocol itself is not new, and there are certain functions you might expect from it, with or without cloud functionality. The most obvious one is authentication, but the LDAP Interface extends beyond this by adding MFA to protect LDAP resources, something that couldn’t be done easily before. When surveyed, one customer illustrated the authentication possibilities beautifully:
"[We] immediately jumped on board with the use of the LDAP interface to enable our business intelligence team to deploy an analytics platform (KNIME) into AWS and allow it to SECURELY and EASILY communicate to our internal Active Directory identities via Okta. The magic here is we were able to leverage MFA into the auth workflow thanks to Okta. We would normally never expose LDAP external to our network in this way but we can now thanks to Okta."
The second benefit is the core of what Okta is known for: the freedom of best of breed apps. We’ve captured a lot of feedback on this effect:
– “It is the source of truth for any pieces not directly tracked by our workforce application (ADP).”
– “It allows us to easily assign Macs to our employees in Jamf.”
– “It allows SaaS vendors that do not support SAML or OID authentication to be able to integrate with SSO for our identities.”
Big moves from EA to GA
Perhaps you were an EA user, so you’re well aware of the benefits of the LDAP Interface. Please note that the jump from EA to GA included major improvements such as compound search with wildcard support, syslog reporting, and configurable pagination size.
But we’re not done, so keep monitoring the Okta Product Roadmap, as future plans include multiple LDAP Interface instances, per-instance sign-on policies (including network zones!), and custom schema support (e.g., POSIX).
A few last words
Although we’re always looking for ways to improve, user reaction to LDAP Interface has been positive, varied, and worth quoting for all the ways customers are seeing value:
– “I think it would have been really useful for a previous client since they had a lot of apps that authenticated through LDAP only.”
– “We connected a SaaS solution to Okta LDAP instead of poking inbound holes in our firewall to accommodate it.”
– “It adds huge value for us as it allows automation of onboarding new user accounts.”
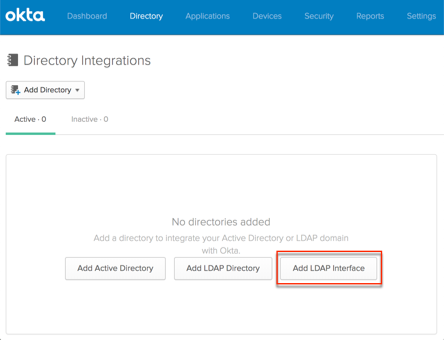
This is the first GA feature we’ve profiled in The Production Line series, so you have the power to deploy today. Didn’t know the LDAP Interface existed? Learn how to implement the feature right here: Connecting to Okta using the LDAP Interface.
Missed a previous post? Read them all: Meet Our New Product Series: The Production Line Automations

