SecurityInsights: Protection at the Admin, User, and Network levels
Modern organizations are adopting new technologies more rapidly than ever before, and their increasingly mobile workforces — which include not only employees, but external contractors and partners — have expanded far beyond office walls.
Today’s organizations face progressively complex security challenges, and must maintain a posture that offers robust protection at scale without slowing down dynamic, global workforces. To address these challenges, today at Okta Showcase, we are excited to introduce a new family of features that provides customers with personalized security detection and remediation capabilities at the end user, administrator, and customer network level: Okta SecurityInsights.
Collectively, SecurityInsights enables enterprises to take meaningful action across their organizations to improve security. In this post, I’ll break down how each piece of the SecurityInsights trinity will help keep our customers secure in the face of this dynamic threat landscape.
1. HealthInsight: Evolving in pace with the threat landscape
When implementing security policies across an organization, administrators want to adhere to industry best practices. But that’s not as easy as it may seem: the threat landscape isn’t static — it’s changing day by day. Best practices for security configurations, including password policies and multi-factor authentication (MFA) requirements, shift as new threat vectors have emerged. And these standards will undoubtedly continue to evolve in the coming years (if not months or weeks).
To address this shifting threat landscape, we are excited to introduce Okta HealthInsight — a dashboard available to Okta admins that continuously monitors their organization’s security policies and settings within Okta, offering personalized recommendations on how they can adjust their configurations to enhance their security posture.
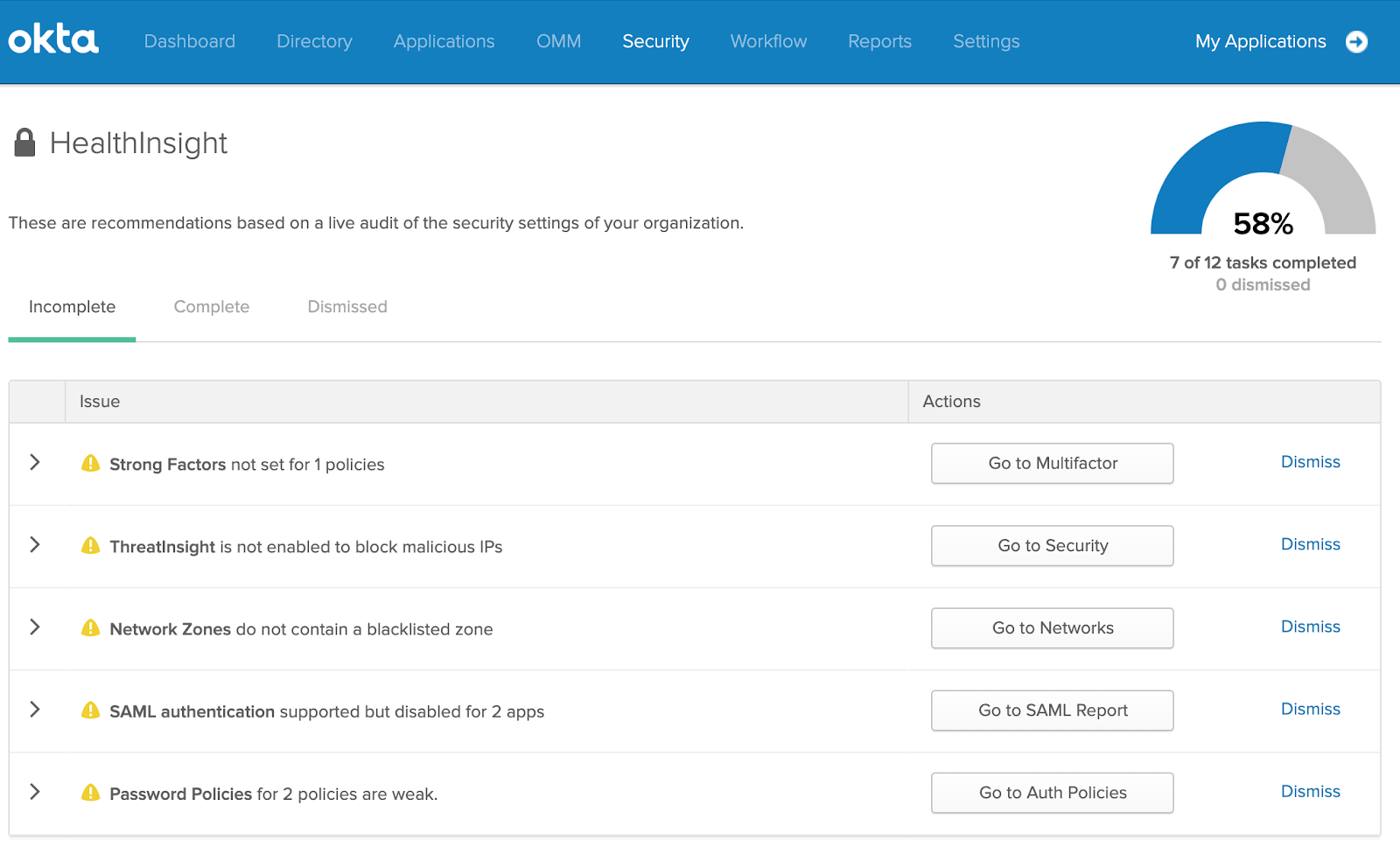
Our experience working with thousands of global customers — and the insights gathered from that work — informed the development of the security best practices within this feature, which include recommendations for password policies, MFA factor enrollment, setting up notifications for anomalous activity, and more. Like the threat landscape itself, HealthInsight is dynamic, and will evolve over time to keep pace with the needs of our customers.
The result: Customers get specific, personalized, actionable administrative recommendations to help them stay ahead of the curve of shifting security threats.
2. UserInsight: Turning targets into first responders
Signing in from a new client, enrolling a new MFA factor, and resetting a factor are fairly uncommon actions for a user, and can sometimes indicate foul play by a bad actor. But with millions of log entries in an organization’s SIEM solutions, it’s impossible for security teams to monitor and respond to every potential issue.
But now, thanks to UserInsight, users can share that responsibility. UserInsight’s suspicious activity reporting alerts end users to potential anomalous or suspicious activity within their account, including logins from new devices and the enrollment or resetting of authentication factors. After being notified, end users have the ability to report the activity to their admins, kicking off automated incident response workflows.
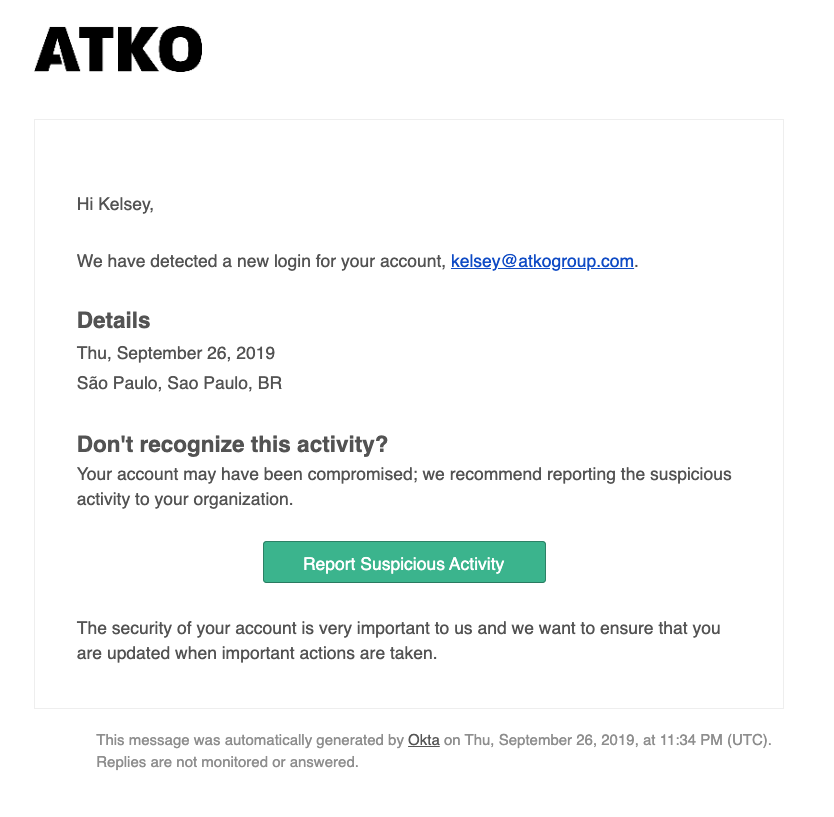
Using Okta Hooks or our Workflows product, Okta can also automate certain actions in incident response tools like quarantining a user, thereby preventing access to apps with sensitive data until identity verification can be confirmed through biometrics and/or Okta Verify, our mobile authenticator. Or admins can automatically notify SecOps teams of potential account compromises through integrations with digital operations platforms like PagerDuty.
The result: Would-be targets become first responders in identifying and addressing attacks against our customers’ userbases.
3. ThreatInsight: Automated threat detection and prevention
Today’s workforces are no longer confined to office walls — external employees, contractors, and partners access organizational data from a variety of locations and networks. This sprawling workforce means that users — and bad actors — frequently attempt to access organizational resources from different locations. As a result, many organizations face the challenge of blocking login attempts from suspicious IPs without locking out legitimate employees.
*ThreatInsight, which we introduced at Oktane18, addresses this challenge in a few ways with an emphasis on maximizing security while minimizing impact on legitimate user access.
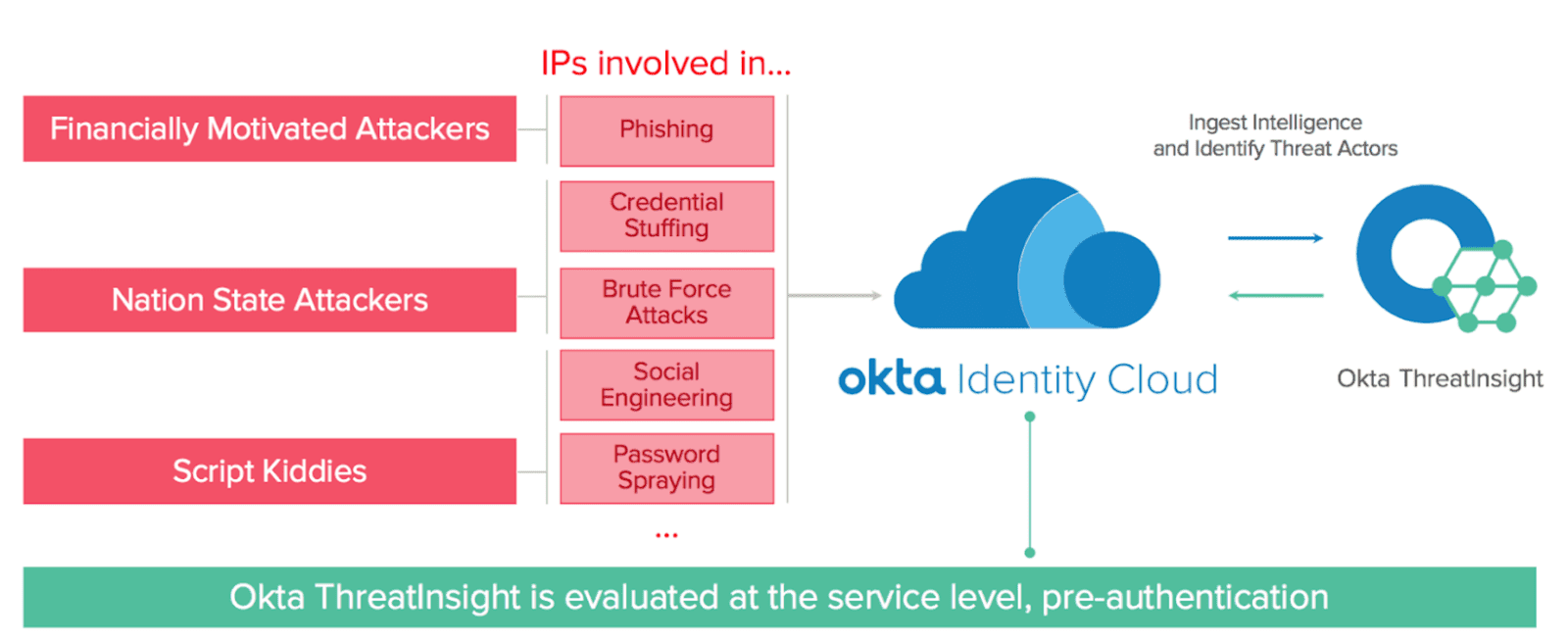
The Okta security team actively seeks out and blocks malicious IP addresses causing identity attacks on multiple Okta orgs, or hundreds of users within one Okta org. These IPs are blocked at the router level, with rate limits applied so as to avoid locking out legitimate users.
In addition, ThreatInsight helps customers make informed blocking decisions. We recognize that for every malicious login event captured by our service, we see many more suspicious events coming from IP addresses that we can’t confirm to be malicious with 100% certainty. There could be a legitimate use case for multiple failed logins depending on the scenario, such as when a hotel hosts a large conference, in which case blocking those IP addresses could actually block legitimate authentication attempts.
So, looking across all authentications across Okta’s vast network of customers, ThreatInsight collects and analyzes metadata and behavioral signals to reveal risks from suspicious IP addresses that could otherwise go unnoticed. When Okta sees large-scale identity attacks like a DDoS, password spraying, high rate of login failure etc., those IPs are added to the ThreatInsight pool, and customers can choose to block access from those IP addresses (only requests to the API endpoints covered by ThreatInsight, /authn and /ws-fed active and passive, are being blocked by ThreatInsight).
The result: Customers receive extra layers of protection from potentially harmful network sources through a proactive and adaptive approach — all with a minimal impact upon user productivity.
Learn more
Okta SecurityInsights features are available today to all customers. Tune in to the Okta Showcase to learn more about upcoming innovations from Okta, or learn more about SecurityInsights and each its elements of by following the links below.
SecurityInsights
ThreatInsight
HealthInsight
UserInsight
*Okta ThreatInsight is just one tool in the security toolbox. It cannot guarantee 100% malicious IP address detection or 100% threat detection. Okta ThreatInsight covers and blocks certain malicious traffic to the following endpoints – api/v1/authn, app/office365/{key}/sso/wsfed/active, and wsfed/passive. Please note, per our Master Subscription Agreement, endpoints are considered Free Trial Services.

