Zero Trust: Past, Present, and Future
Prior to the Zero Trust era
Over the last decade, we’ve experienced three megatrends in action: mobile, cloud, and software-as-a-service (SaaS). These megatrends have redefined how we work, conduct business, and consume information. According to Gartner, global end-user spending on public cloud services is expected to exceed $480 billion in 2022 with a year-over-year growth rate of 21.7%. We were already moving away from an 8-hour day, 5-day week in the office, as employees connected to corporate networks from their homes or while traveling with laptops and smartphones. But the pandemic put this movement into overdrive, accelerating the work-from-anywhere trend due to shelter-in-place mandates. Within the tech world, this turned all but the most essential workers into a fully remote workforce overnight.
Meanwhile, the steady increase in hybrid IT environments continues to impose new and complicated IT and security requirements. Where data centers used to operate mission-critical applications and store sensitive data, large-scale corporations are starting to buy into the cloud paradigm. In the interest of lower cost and higher scalability, the trend is to move resources from on-premises hardware to public cloud environments. And, due to faster return on investment and lower total cost of ownership, corporations are opting for SaaS apps over the traditional self-hosted enterprise apps or build-it-yourself solutions.
However, the adoption of mobile, cloud, and SaaS megatrends imposed great challenges to corporate security and user experience:
- Traditional network security infrastructure was based on the castle-and-moat approach, where resources are protected by corporate perimeters with network-security appliances. Protections might include anti-virus software, firewalls, URL filtering, data loss prevention, denial-of-service attack protection, and sandboxing. To accommodate the telecommuting and mobile-work trends, virtual private networks (VPNs) were introduced to form secure channels between corporate networks and their remote workers. However, VPNs would grant users unnecessary access to corporate networks and resources, and users would often experience slow connection issues when too many were attempting to use them at one time.
- When the need to securely access SaaS apps from anywhere arose, the traditional “Band-Aid” approach was to route all traffic to headquarter data centers. From there, resources were accessed from centralized locations. However, due to inefficient traffic routing, limited scaling capability, hidden costs, and suboptimal security, this process would often break down.
- Today, organizations have found that the transition to cloud environments has a low initial setup cost, minimal maintenance requirements, and provides workload scalability and elasticity. However, many resources are segregated by enterprise data centers and public cloud providers. Moreover, cloud-native workloads have proven to be dynamic, ephemeral, and interdependent, requiring cloud-native security protections.
Entering the Zero Trust era
The historical definition of corporate security focused on providing connections, monitoring, and detection using network defense approaches. However, as corporate perimeters became outmoded, this location-based security was no longer effective. Instead, identity began to play a central role in a new, modernized security framework. This identity-centric security framework is called Zero Trust. The Zero Trust concept was designed with the following assumption: “never trust, always verify.” This model replaces the implicit trust once inferred from static location information with explicit trust criteria based on dynamic, contextual data. The sources of contextual data include user identities, application and resource properties, endpoint status, network health, and corporate policies.
Zero trust network access (ZTNA) is a product that provides a secure, private network that is only conditionally accessible to verifiable requests. Zero trust brokers continuously verify identities, contexts, and policies of requests before granting or denying access. ZTNA removes apps from public visibility and significantly reduces surface areas for attacks. ZTNA quickly gained initial traction as a VPN replacement, since ZTNA brings benefits in ease-of-adoption and scalability. Moreover, identity and context-based micro-segmentation provided by ZTNA allows fine-grained security control. The micro-segmentation approach is more effective in preventing lateral movement than traditional network-based segmentation approaches.
As the legacy perimeter model continues to fail modern security needs and performance requirements, more and more corporations are interested in pursuing Zero Trust strategies. In 2019, Gartner combined network connectivity with network security, and coined the secure access service edge (SASE) model. Using this model, corporations can replace their inefficient and unsecured hub-and-spoke network infrastructure by using cloud-based identity-centric network access together with Secure Web Gateway (SWG) and Cloud Access Security Broker (CASB). Or corporations can reduce or replace existing Multi-Protocol Label Switching (MPLS) using identity and access management (IAM), SWG, and CASB on top of Software-defined Wide Area Network (SD-WAN).
Envisioning the Zero Trust era
Zero Trust advancement in the data plane and the control plane
The best way to visualize Zero Trust development and adoption is to explore the ideal Zero Trust architecture. To do so, we can abstract the implementations of a Zero Trust framework to a combination of a data plane and a control plane. The data plane provides access to resources, while the control plane makes continuous, real-time decisions about who or what can access the resources. We’re going to draw an analogy between semiconductor devices and the ideal Zero Trust architecture.
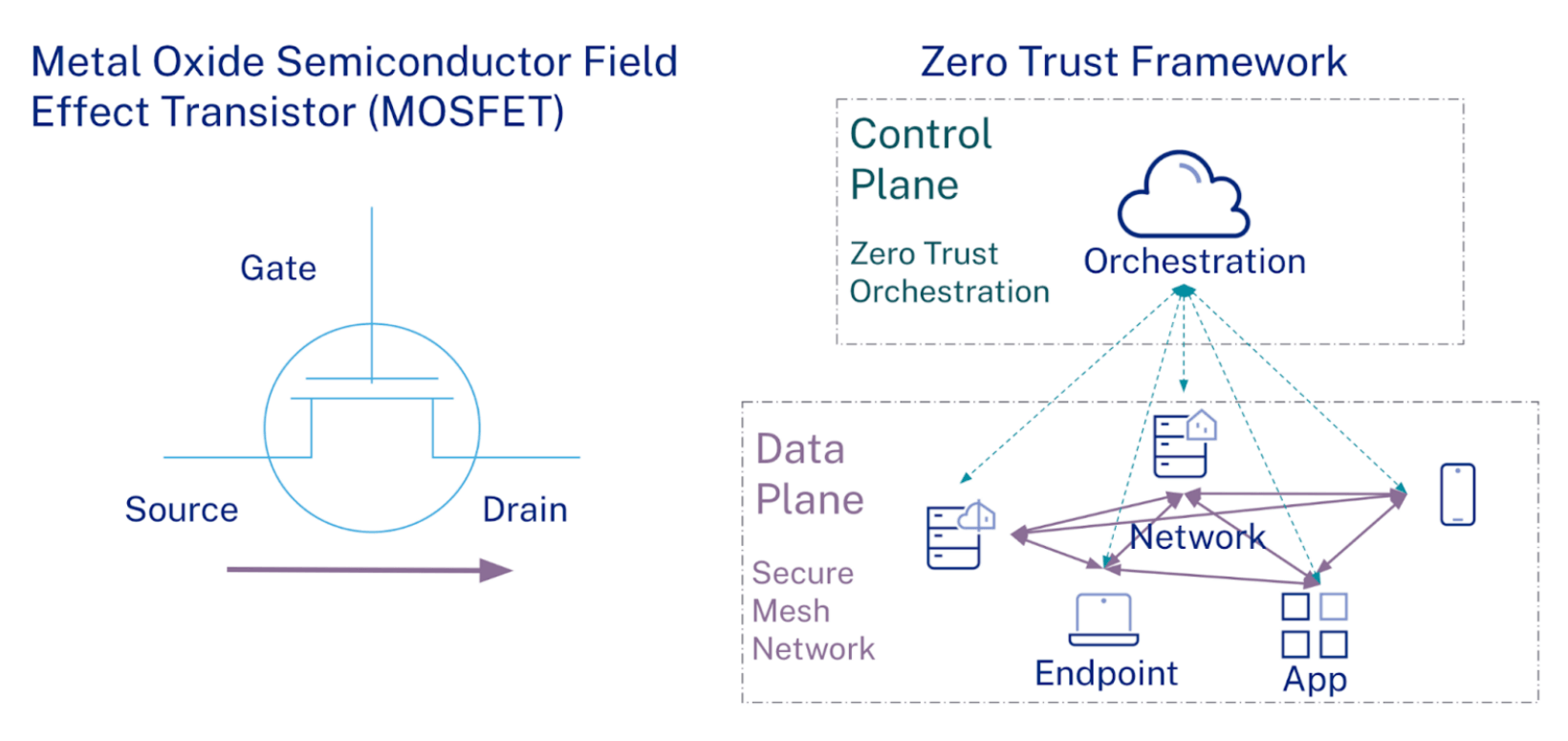
A Metal Oxide Semiconductor Field Effect Transistor (MOSFET) is the basic building block of integrated circuits. A MOSFET has 3 terminals: source, drain, and gate. We control the flow of the MOSFET current by applying a gate voltage. When the gate voltage (i.e., the control plane) is larger than the absolute value of its threshold voltage, the channel between the source and the drain (i.e., the data plane) turns on, and the current flows between them. Conversely, when the gate voltage is smaller than the absolute value of its threshold voltage, the channel turns off and there’s no current flow.
Two key principles of designing and scaling MOSFETs are to make transport between the source and the drain as frictionless as possible, and to make the gate control as strong as possible. So, how does this apply to Zero Trust? The ideal Zero Trust framework should have the most efficient data plane and the most effective control plane.
The Zero Trust framework is about providing secure, private networks holistically as the data plane. Instead of addressing the people, apps, workloads, and data connections separately, it is more efficient and secure to address them all together in a unified way.

In this scenario, a secure mesh network connects the traffic from any and all resources, devices, and users using any type of network infrastructure. The secure private mesh network would serve as an overlay of the underlying physical network infrastructure, whether it is Broadband, Fiber-optic, 4G, 5G, or WiFi. The secure private mesh network abstracts corporate IT and security panorama away from physical topologies. Based on an organization’s IT and security needs, the mesh network establishes logical relationships among people, applications, and resources using identities, contexts, and policies.
A Zero Trust framework is about providing Zero Trust orchestration as the control plane. The Zero Trust orchestration consists of observing, monitoring, inspecting, analyzing, and action-taking. The interactions between Zero Trust orchestration and secure mesh networks provide feedback loop control.
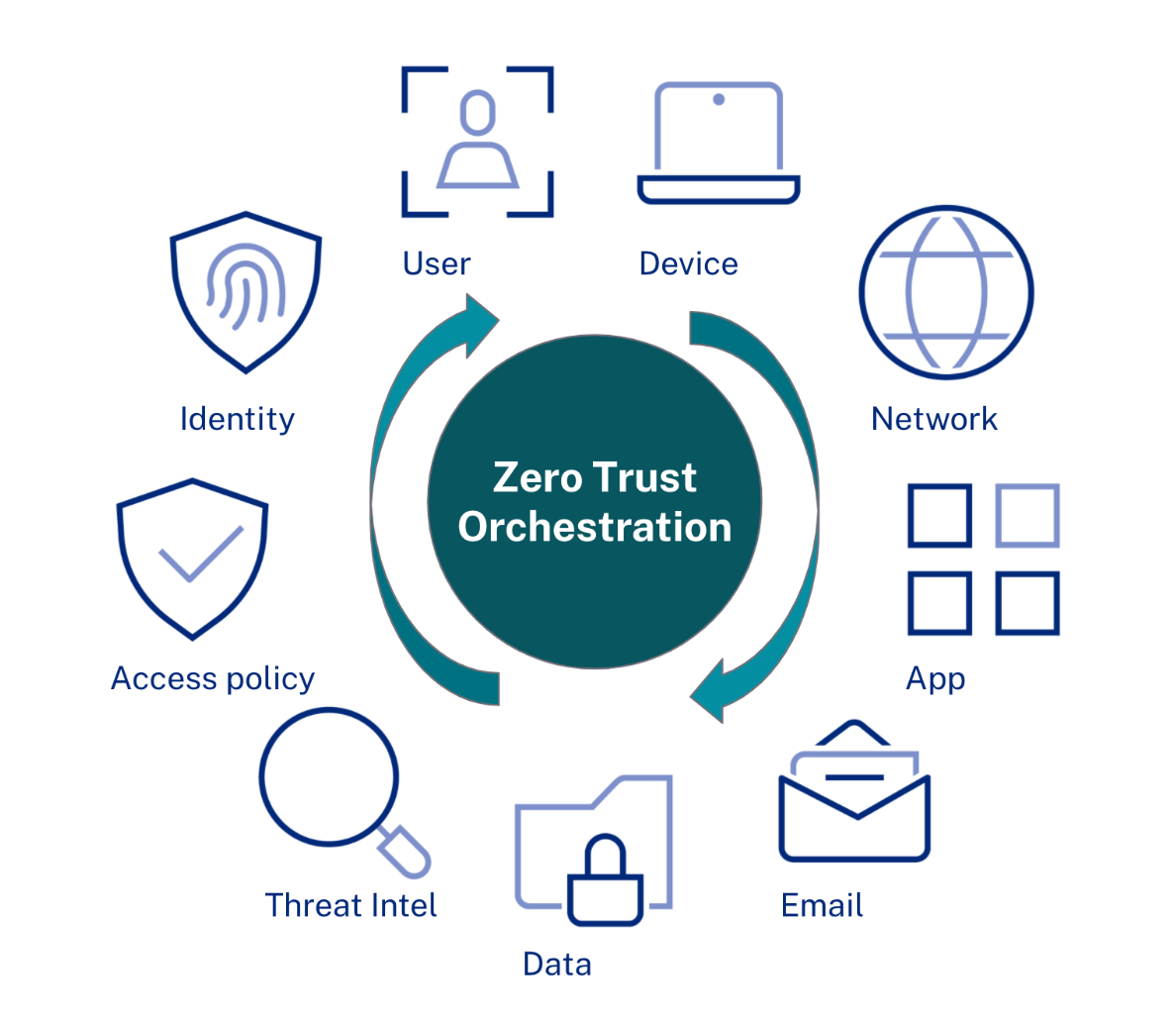
In essence, the three key characteristics of Zero Trust orchestration are integrated, bi-directional, and continuous:
- Integrated: The Zero Trust orchestration integrates a wide variety of security signals, turning them into contextual data. The signals may come from a list of identity types: users, devices, apps, workloads, and data. The signals may come from a list of status data: network traffic, endpoint devices, workloads, apps, and emails. The signals may come from user behavior and threat intelligence. The Zero Trust orchestration also incorporates access policies in the decisions of authentication, authorization, session management, or resource revocation.
- Bi-directional: The Zero Trust orchestration exchanges information bi-directionally with security components: identity providers, networks, endpoints, and apps. It gathers data by listening to event streaming or by correlating historical inputs from the security signals. It then synthesizes the information using machine learning and rule-based approaches. After that, it sends back directions to the security components for action-taking.
- Continuous: The Zero Trust orchestration enables continuous security management. Instead of having security control only at the point of connections or access, the Zero Trust orchestration allows near real-time security enforcement across the entire lifecycle of the connections. For example, when the Zero Trust orchestration detects malicious activities or disabled user accounts, it can immediately request identity providers to revoke refresh tokens or sessions, suggest networks disconnect from resources, and/or ask apps to re-authenticate users.
How Zero Trust and identity work together
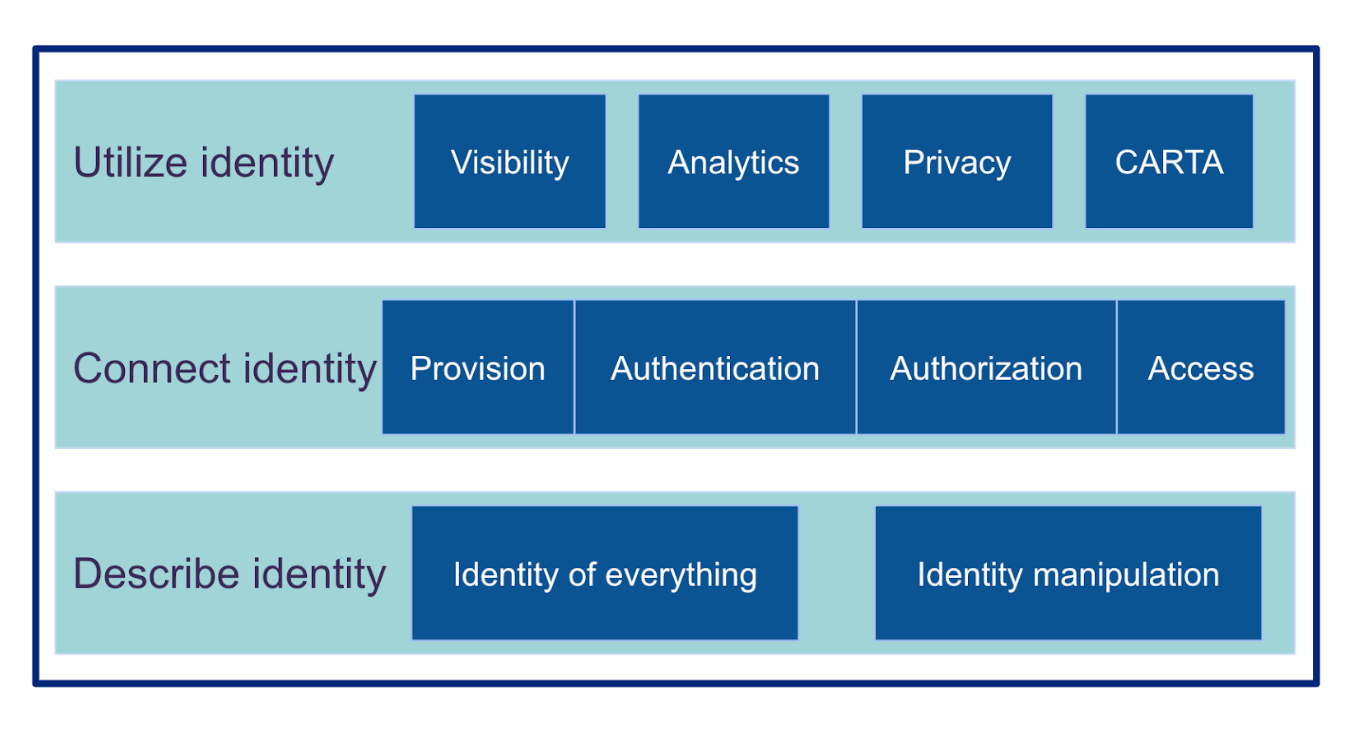
Identity is the cornerstone of the Zero Trust framework. We need identities to describe, control, and manage almost everything: employees, customers, contractors, on-premises apps, SasS apps, APIs, servers, virtual machines, containers, serverless, internet of things (IoTs), bots, data sets, or even non-fungible tokens (NFTs). IAM, privileged access management (PAM), identity governance and administration (IGA), and identity proofing are ways to make connections among these identities. Zero trust security is one of the best examples of utilizing identity to achieve a better user experience and a stronger security posture.
A call for collaboration within the security industry
From both internal R&D and M&A perspectives, Zero Trust has attracted a flux of investments within the security industry. As a result, dozens of companies have recently introduced Zero Trust offerings. Zero Trust is a modern way to design enterprise security, and its adoption could drive industry consolidation. However, no providers, not even the most powerful security platform vendors, can offer a complete suite of Zero Trust products by themselves. This is because in cybersecurity, good enough is not enough, and it’s extremely risky to put all your eggs in one basket when building security infrastructure. A better way? Build deep, strategic relationships with a handful of security companies and implement best-of-breed products to guard against future cyber attacks. It’s also a good idea to separate security providers from app providers to preserve an additional layer of protection.
Our security industry suffers from a lot of fragmentation, and we need to think more about collaboration. In doing so, we become technology enablers, allowing everyone and every organization to safely use any technology, anywhere. Collaboration becomes even more crucial in the Zero Trust era. We are seeing early explorations in sharing security signals, such as OpenID Foundation’s Shared Signals and Events working group. We expect more joint effort across our security industry.
For more facets of Zero Trust, check out the Okta blog for our library of content around Zero Trust.