When threat actors log into systems, they don't use their real IP addresses. Instead, they route their traffic through VPNs, proxies, and anonymizing networks. We analyzed a January 2026 data leak from BreachForums — a major English-language cybercrime marketplace — that contained threat actor IP addresses. The analysis can help Okta administrators make evidenced-based decisions about risky login behaviors and how to use controls to limit logins from dodgy virtual private network (VPN) services or anonymizing networks.
IP addresses are key indicators of compromise. Attackers don’t want to use IP addresses that could be potentially linked to their real-world identities if law enforcement obtains warrants or subpoenas that will be honored by service providers. This pushes them to the corners: virtual private network (VPN) services that promise to not retain logs, anonymizing proxies and so-called “bulletproof” networks. The desire to protect their identity extends not only to when they are staging attacks but also when threat actors log into forums and marketplaces used for cybercriminal activity.
Underground forums occasionally experience data breaches, and these leaks are an informative source of open-source intelligence. In January 2026, a dataset from a cybercriminal forum known as BreachForums was publicly released. The data compromised registered users from the forum, including nicknames, hashed passwords, email addresses, and IP addresses, with the data current as of around October 2025.
BreachForums was a mainstay of the English-speaking cybercriminal underground, offering tools and services for fraud and cybercrime, guides, malware and served as an advertising platform for selling data leaks. It was the successor of RaidForums, which was taken offline by law enforcement in April 2022. BreachForums was disrupted by law enforcement at least twice since its first iteration in March 2022.
BreachForums ran on the MyBB open-source forum software on a MySQL database. The user database included many fields, including registered email addresses, hashed passwords, the IP a user registered to the forum and the IP of their last visit. Below is the full list of data fields.
 The full list of data fields from a data leak of the BreachForums cybercrime forum.
The full list of data fields from a data leak of the BreachForums cybercrime forum.
The database contained nearly 324,000 rows. Some 235,208 rows have a “regip” — a field that is short for “registration IP,” which is the date an account was registered — and a “lastip” — a field indicating when someone last logged in — of 127.0.0.9. This IP address is reserved for localhost or loopback routing. This is odd. It could mean the forum was incorrectly configured, which caused the logs to be inaccurate, or may have been intentional. However, more than 88,700 IPs have “lastip” values that are not 127.0.0.9.
We decided to look at these IPs and their corresponding ASNs to understand what services registered BreachForums participants used in order to preserve (or, in some cases, not preserve) their anonymity. The theory: If threat actors trust these networks, these networks may also be favored to launch various identity-centric account takeover attacks.
Underground cantina
All kinds of different personas logged in to BreachForums, and not just cybercriminal actors. Think of it as the online equivalent of the Mos Eisley cantina, the rough-edged alien bar in the original Star Wars film where creatures from around the galaxy mingled. Serious cybercriminals might be sitting at the bar, law enforcement and CTI professionals are lurking in the booths.
This means we can’t say that all of these IPs absolutely belonged to threat actors, as law enforcement and cyber threat intelligence (CTI) researchers may use the same services in order to blend in. Nonetheless, that blend of usage can provide an even higher degree of likelihood that requests coming from these ASNs, IPs and proxies are less likely to be “normal” users, and it’s also less likely that blocking them are going to trigger false positives.
 The BreachForums cybercrime forum hosted a variety of users, from threat actors to law enforcement to cyber threat intelligence professionals.
The BreachForums cybercrime forum hosted a variety of users, from threat actors to law enforcement to cyber threat intelligence professionals.
Top Autonomous System Names (ASNs)
While the list below are the top ASNs seen in the BreachForums data, being included in this list is not intended to impugn the reputation of these companies or organizations. Legitimate services are consistently abused by bad actors. Also, network ranges that are owned by large network providers and data centers may lease a portion of it to smaller providers, such as those providing VPN services or proxies. Small network operators, such as bulletproof hosting providers, frequently shift their network ranges and change connectivity suppliers in an effort to make it more difficult to shut down and shield criminal customers from abuse complaints. Nonetheless, this data can provide a snapshot of activity at a certain point in time.
CDNEXT, GB: This ASN (AS212238) run by U.K. based DataCamp Limited, which is a large provider of content delivery network (CDN) and network services, had the most IPs in the BreachForum data. It runs numerous networks in locales around the world including the U.S., the U.K., the Netherlands.
TORSERVERS-NET, DE: This is a small ASN (60729) run by the Association for Digital Fundamental Rights in Germany on 185.220.101.0/24. It consists of relays for The Onion Router, or Tor, which is an anonymity platform that encrypts browsing traffic through networks of relays around the world in order to make it more difficult to figure out a user’s real IP address.
M247, RO: M247 Global is a large hosting and cloud infrastructure provider.
CLOUDFLARNET: Cloudflare is a large CDN and cloud network provider focused on security and performance.
CYBEROLOGY-AS, NL: This ASN (215125) calls itself the Church of Cyberology, which describes itself as “a religious organization that encourages (online) freedom, liberty and privacy.” It runs out of the Netherlands and operates Tor relays on a small IPv4 range, which is 192.42.11.0/24.
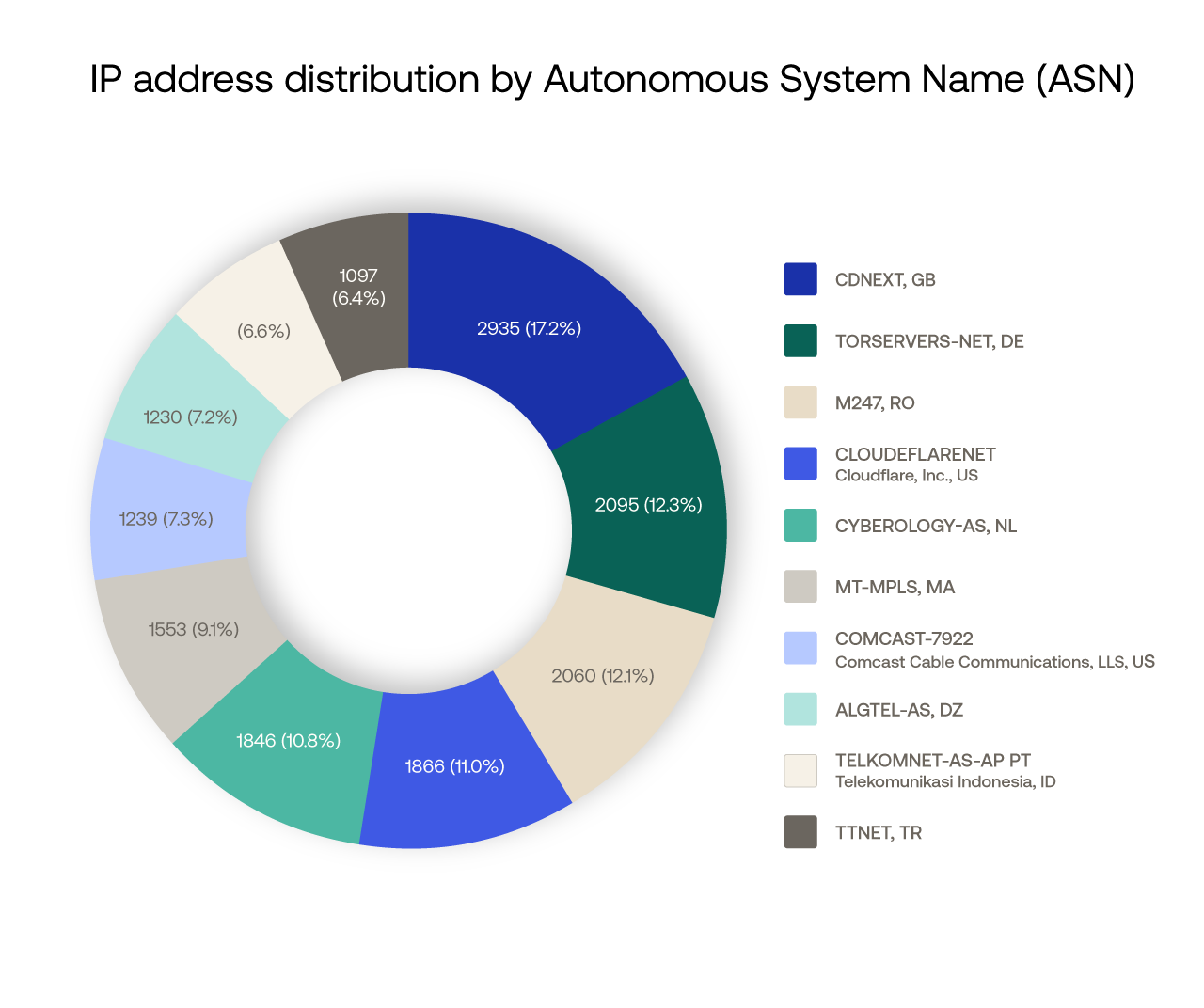 The top 10 ASNs seen in the leaked BreachForums data.
The top 10 ASNs seen in the leaked BreachForums data.
Should requests from networks abused by intrusion actors be subject to more restrictive policies, or even blocked outright?
Mature environments tend to allowlist trusted networks and deny requests from all others, so analyses of IP reputation aren’t required. That being said, it’s not always easy to create a known baseline, particularly in organizations with a large “extended network” of third-party partners or independent agents.
For these organizations, the first step is identifying legitimate sign-ins from these services. Administrators can identify successful sign-ins from any given ASN in Okta Identity Engine using the following query:
eventType eq "user.authentication.verify" and securityContext.asNumber eq "[ASNumber]"
To provide additional context, Okta Threat Intelligence performed a quick analysis of success:failure ratios at authentication for each of the top 20 ASNs in the Breached Forum list over the week prior to publication, across all commercial Okta orgs.
The analysis reveals that requests from several of the 20 ASNs most frequently observed in the BreachForums leak fail four to five times more frequently than they succeed.
ASNumber | AS_Org | Authentication Success rate % |
212238 | CDNEXT, GB | 24.09% |
60729 | TORSERVERS-NET, DE | 18.34% |
9009 | M247, RO | 36.09% |
215125 | CYBEROLOGY-AS, NL | 11.52% |
13335 | CLOUDFLARENET - Cloudflare, Inc., US | 82.31% |
36903 | MT-MPLS, MA | 19.61% |
36947 | ALGTEL-AS, DZ | 8.48% |
7922 | COMCAST-7922 - Comcast Cable Communications, LLC, US | 58.71% |
9121 | TTNET, TR | 21.56% |
7713 | TELKOMNET-AS-AP PT Telekomunikasi Indonesia, ID | 33.12% |
36925 | ASMedi, MA | 41.67% |
12735 | ASTURKNET, TR | 35.86% |
7018 | ATT-INTERNET4 - AT&T Enterprises, LLC, US | 72.77% |
55836 | RELIANCEJIO-IN Reliance Jio Infocomm Limited, IN | 70.42% |
8452 | TE-AS TE-AS, EG | 55.03% |
12322 | PROXAD, FR | 82.44% |
208323 | APPLIEDPRIVACY-AS, AT | 31.57% |
16276 | OVH, FR | 59.22% |
3215 | France Telecom - Orange, FR | 82.86% |
210558 | 1337 Services GmbH, DE | 0.36% |
Our methodology compared successful authentication events (user.authentication.verify) with failed authentication events (failed sign-in events, plus those requests Okta identified as threats and blocked at the network edge). It did not differentiate between workforce and customer identity systems. The data does not include requests denied via customer use of Network Zone policies - this would double or triple the number of “failed” requests if it were included.
VPN and Proxy Usage
Threat actors who logged into BreachForums used IPs that belonged to a mix of virtual private network (VPN) and proxy services as well as private one. Although about 75% of the BreachForums IPs are not publicly routeable, more than 35,000 IPs could be enriched. Unsurprisingly, IPs linked to The Onion Router (Tor) anonymizing system comprised more than 42% of the top 10 services. The second most seen service was Mullvad VPN followed by Proton VPN and Nord VPN. Residential proxy services, which are often used to avoid triggering geolocation restrictions and for attacks such as credential stuffing, did not meaningfully appear in the results. Below is a chart showing the top 10 VPN and Proxy services used.
Top 10 VPN and Proxy Services Used
Rank | Operator | Percentage |
|---|---|---|
1 | TOR_PROXY | 42.7 |
2 | MULLVAD_VPN | 13.3 |
3 | PROTON_VPN | 12 |
4 | NORD_VPN | 9.4 |
5 | WARP_VPN | 7.3 |
6 | OXYLABS_PROXY | 5.6 |
7 | ICLOUD_RELAY_PROXY | 3 |
8 | EXPRESS_VPN | 2.7 |
9 | OPERA_VPN | 2.5 |
10 | SURFSHARK_VPN | 2.4 |
Top Email Address Domains
Online service providers typically send an email to the address of newly registered users in order to confirm the address. BreachForums did not do this. This means that the email addresses in the database may not even exist with a service provider. There are advantages to not being required to provide a real email address on cybercrime forums. If the email doesn’t exist, its service provider won’t be able to provide law enforcement data or metadata related to it. It is also possible that BreachForums registrants used other people’s email addresses as a diversion tactic.
The BreachForums data contains 323,986 rows. About 27,000 rows contain invalid email addresses, no email address or email addresses such as null@null.com. Overwhelmingly, BreachForums registrants used Gmail addresses — about 81% of the total. About 14.3% of the email addresses had domains linked to Protonmail, the privacy-centric encrypted email service. The third most common at around 1.6% was Onionmail.org, which uses the Tor network and does not retain personal data or IP addresses. The fourth most common were addresses with Cock.li, which had about 100 more accounts than the number five domain, which was Yahoo.
 Gmail was the top email domain used by threat actors to register on BreachForums, however, the forum did not verify email accounts.
Gmail was the top email domain used by threat actors to register on BreachForums, however, the forum did not verify email accounts.
We ran a sample of 16,044 email addresses through Have I Been Pwned, the data breach notification service, to see where else the same addresses may have been leaked before. This doesn’t mean that the email addresses have actually been registered, but if an email address appears in another breach, it may be more probable that the email address exists.
Of the 16,044 email addresses in our sample, 10,200 email addresses appear only in the "BreachForums2025" data, and 7,515 are Gmail addresses. This suggests that BreachForum registrants heeded the advice of one of its administrators, who advocated use of “disposable” email addresses, or those used for a single purpose and not for other accounts. The remaining 5,844 accounts appeared across other large data breaches related to information stealing (infostealer) malware logs.
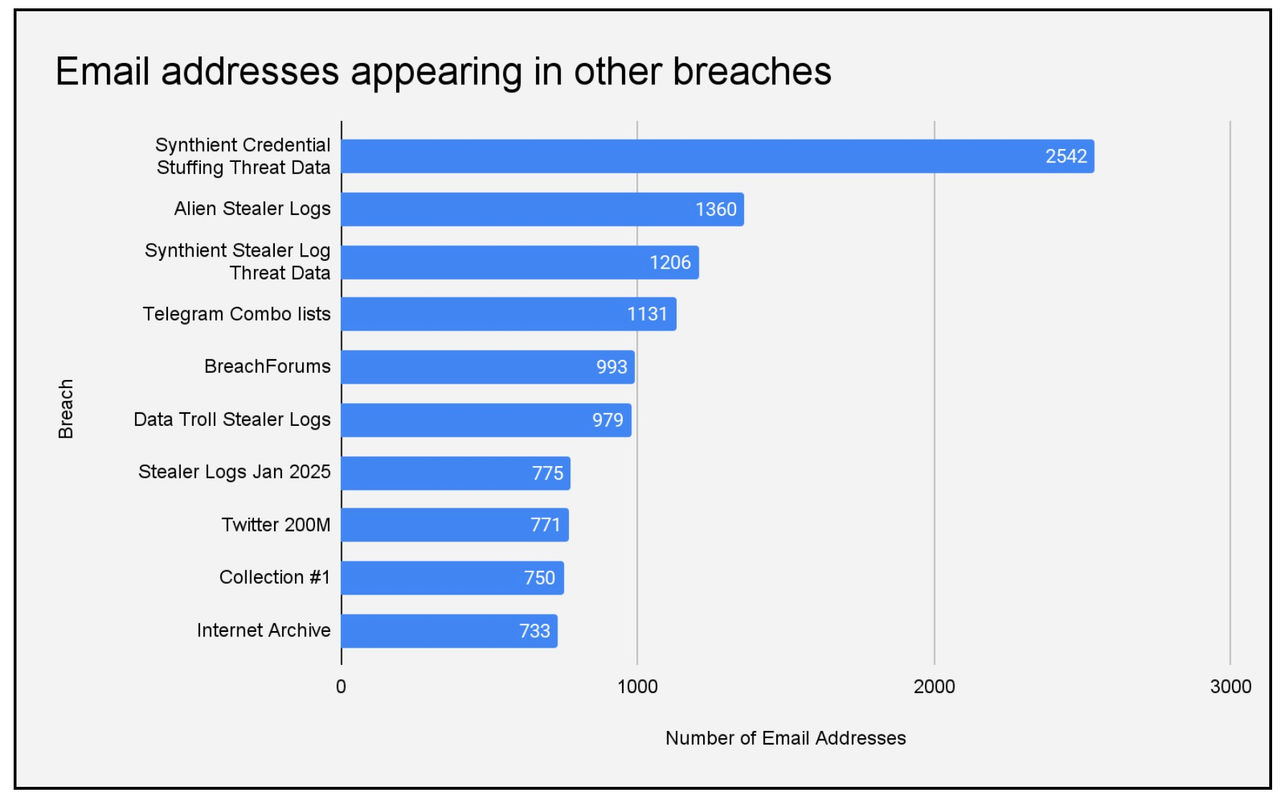 This chart shows BreachForums email addresses that the Have I Been Pwned data breach notification service showed appeared in other breaches.
This chart shows BreachForums email addresses that the Have I Been Pwned data breach notification service showed appeared in other breaches.
Conclusion
The BreachForums data provides insights into the choices made by threat actors when logging into a criminal forum. Presumably, most of those users were making choices that reflected a degree of awareness of their own operational security.
Usage of VPNs and anonymizing networks does not imply that all of those users are engaged in shady activity. However, these are the types of networks are typically used by those seeking to hijack accounts with stolen credentials sourced from underground markets and via malware campaigns. By understanding broad trends around attacker use of VPNs, proxies and other service providers that don't respond to abuse reports, defenders can make informed decisions to deflect identity-centric attacks.
Recommendations
With Okta’s Adaptive MFA, administrators have visibility into risk signals by comparing a login event with a previous one, such as whether the user is using the same IP address, location, or device. If the pattern varies on the user’s previous history, the user can be prompted for another authentication factor.
Okta customers can also block proxies, virtual private networks (VPNs) and other anonymizing networks using Enhanced Dynamic Zones. Using these controls, it is possible to block all requests at the network edge before the user reaches the sign-in page.
Auth0 customers can set Tenant Access Control Lists to manage traffic, or can limit logins from certain IP addresses using Auth0 Actions.




