The State of Zero Trust Security 2023
We surveyed more than 800 decision-makers to learn how organizations worldwide are embracing Zero Trust to keep their people, assets, and infrastructure safe.

Our report finds growing adoption of Zero Trust: 61% of all organizations now have a defined Zero Trust security initiative in place, and another 35% plan to implement one within the next 18 months.
Here’s what else we discovered…

Zero Trust adoption has surged since 2021
Two years ago, our annual survey found that just 24% of respondents had a Zero Trust strategic initiative in place. That figure climbed to 55% last year, and to 61% today.
“Does your organization have a defined Zero Trust security initiative today, or do you plan to implement one within the next 18 months?”

"Organizations around the world are taking tangible steps towards Zero Trust. Identity is critical for keeping these complex, global workforces collaborating securely and productively."
- David Bradbury
Chief Security Officer
Okta

Identity is now mission critical
More and more organizations have come to realize that strong Identity Access Management (IAM) is a fundamental strategy to keep people and assets safe. In fact, 91% of respondents said that Identity is important to their Zero Trust strategy.
Across regions, Identity plays a critical role in powering Zero Trust initiatives. North America leads the way, with nearly two thirds of respondents rating Identity extremely important, and nearly one third deeming it somewhat important.
By the numbers
say Identity is extremely important for Zero Trust
say it’s somewhat important
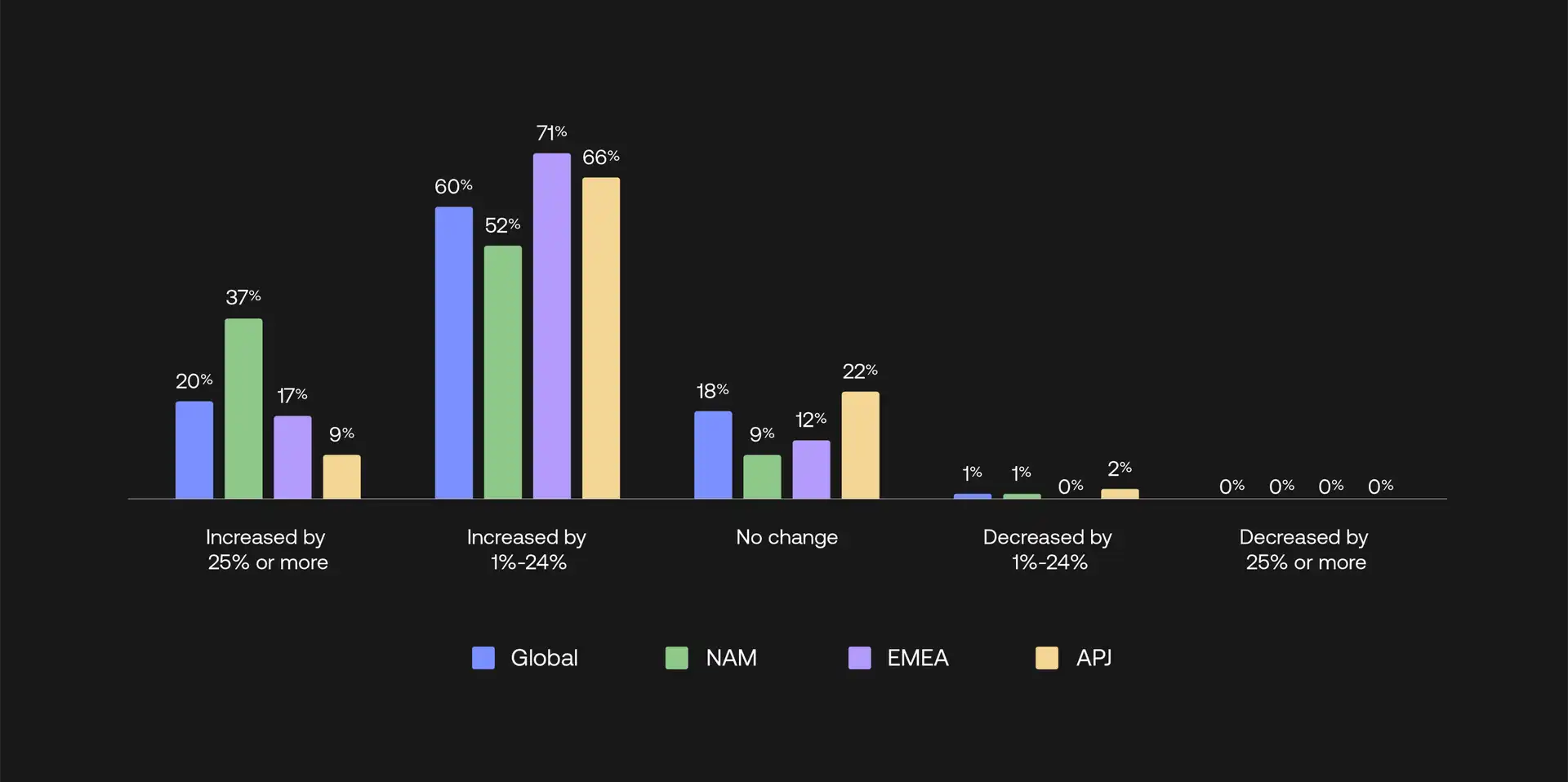
Zero Trust spending is still rising
While budgets are tightening all over the world due to macroeconomic pressures, Zero Trust spending continues to grow. 80% of survey respondents reported that their budgets for Zero Trust security initiatives have increased over the previous year.

Challenges to Zero Trust adoption remain
This year, respondents reported a mix of headwinds when establishing Zero Trust, including cost concerns, technology gaps, and privacy regulations/data security.

FedEx: Connecting 340,000 employees to connect the world
Learn how FedEx verifies thousands of users and devices with a Zero Trust security model.

Discover more Identity insights
Visit our new thought leadership hub for more trends and takeaways from Okta and our customers.

