Oktane18 Fireside Discussion -- What the Heck is CIAM
Transcript
Details
Speaker 1: Hi, everyone. Thanks for joining this session on What the Heck is CIAM? Now, if you're here, I'm guessing that you maybe know something about what CIAM is, because then otherwise, you probably would have just ignored it and gone to some other session. A raise of hands, who has at least heard of CIAM? Okay. That's good. So most of the audience. CIAM, customer identity and access management. Some say it's consumer identity and access management. Hotly debated in our world of identity management, but we say customer identity because we think about it more broadly than consumers. Let me start by talking a little bit about ... Well, first of all, I have a disclaimer that there's a lot of forward-looking statements and things like that. You can read the fine print, and let me continue.
We'll start off with a quote by Forrester. "Customer identity and access management, if done well, can help business owners increase customers' engagement and brand loyalty while maintaining their security and privacy." So, it's pretty straightforward. It's identity management that's customer-facing. At Okta, we see this as an extension of the core platform that we've built. As you heard from Todd this morning, we have our core technologies around authentication, authorization, user management, data synchronization, and we surface those in both in IT context with our portal and end user experience and for our customer identity context. In the world of customer identity, we've long had a very comprehensive set of APIs that allow you to build custom experiences, and more and more, we're getting into customizable out-of-the-box capabilities, as well, around things like registration and login and MFA and things like that. So really focusing on how do we serve all these markets.
On customer identity, the requirements are ... There are some unique requirements that we are paying attention to. So first of all, personalizing the customer experience, and then, second being speed to market. Now, speed of deployment is always important in identity management. Speed to market can get even more important when it's a customer-facing scenario, because it might be revenue-dependent. It's something that you really need to launch for the business within three months or six months, and you can't handle any delays. Centralizing identity management, and so this is something that we see a lot of companies facing as they've had different app dev efforts within the enterprise go and build different experiences. How do they make that central from a management perspective and have one identity shared service for the enterprise as well as unite the customer experience?
Then, enterprise-grade security. This is sometimes the leading factor around customer identity, where you want to make sure that, as Todd was saying this morning, again, are you hashing your passwords correctly? Are you storing that SQL database correctly and making sure it's impenetrable to hackers and everything? Another big reason why you look to a platform to increase your security.
Around these different areas of requirements, there are some challenges sometimes. Around customer experience, 71% of customers churn due to poor experiences. If you get this wrong, it can have serious business consequences. Around speed to market, a six-month delay is average delay in launching new experiences. Around the cost of not having centralized identity management, there could be a 3X total cost of ownership for fragmented identity solutions. Then, finally, with security, 51% of enterprises suffered at least one breach in the last 12 months. A lot of times, this is for their customer-facing authentication systems and things like that.
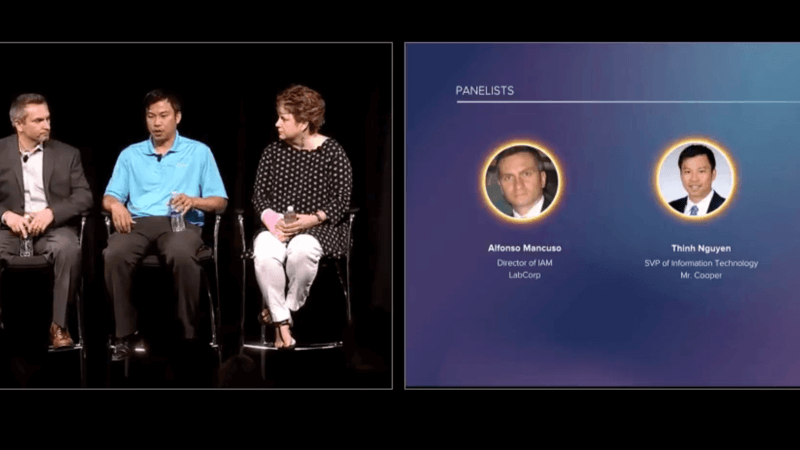
So, a big concern. To tackle and talk about these areas, I want to bring up my esteemed guests here to complete our panel. We've got Alfonso Mancuso, director of identity management at LabCorp; Thinh Nguyen, SVP of information technology at Mr. Cooper; and Tris Lingen CIO at TCF Bank, excuse me. Please go ahead and join me on stage. Did I get everybody's name right?
Tris Lingen: You did, but I'm actually the CISO, not the CIO.
Speaker 1: Oh, you're the CISO. Apologies. Tris is the CISO at TCF. All right, well, thanks for joining us here today. I'm looking forward to this discussion. So let me start off by just asking if you could each describe what were the different identity management challenges that you were facing in terms of customer-facing applications, and what were you trying to solve? Want to get started, Alfonso?
Alfonso Mancuso: Sure. Hello, everyone. Our major challenge in customer-facing identity management with our application base was really not as much to do with the application but the actual customer base. In the life sciences, healthcare, LabCorp is a diagnostic company as well as drug development and does a lot of life sciences work. Our customer base varies. It's not an individual customer. It is a variety of customers, and that customer may, or usually, overlaps from one persona to another. For example, we might have a provider who is also a patient. Making sure that we keep the identities separate is a big challenge, because we don't want Dr. Joe to be able to view patient Joe's information, because the way the identity is leveraged within the various applications changes. We also had challenges with our institutional or our commercial clients, large pharmaceuticals and biotech, and really geared about what their capabilities were. Some have the ability to federate. Others did not. It's a difference in whether we're hosting the identity for them or we're federating with their identity platform and then leveraging and depending on the hygiene of their identity and lifecycle management, which poses a lot of challenges.
Speaker 1: How were things like that handled in the past, like the complexity around a doctor's identity? How did you manage those things?
Alfonso Mancuso: That's a great question. They were specific to each of the applications. We didn't have separate or unified or centralized identity stores. As you pointed out, cost of ownership goes up. User experience adoption suffers.
Speaker 1: Interesting. Thinh, how about at Mr. Cooper?
Thinh Nguyen: For those who doesn't know Mr. Cooper, we're a mortgage service. We're the largest non-bank servicer in the country. We have 4.5 million customers, and we went through a rebranding from Nationstar to Mr. Cooper. For us, it has to do with we didn't have, really, a good way to manage identity. We didn't have SSO. We're launching these digital products to the market that leverages the web and mobile devices. That was a big challenge for us, is making sure it aligns with the brand. Our customers, the 4 million customers, they're already having a hard time managing the largest asset that they own, which is your home. The last thing they want to think about is breach and security and all the transactions that they're doing with us online. A lot of consideration going to that customer experience journey, because they're with us for 30 years.
Speaker 1: It sounds like a lot of what you were trying to tackle was new use cases, how are you doing more modern applications, and things like that?
Thinh Nguyen: Yeah. The mortgage industry is not a sexy business. People don't necessarily transact the same way they do online versus buying things, but people want to use mobile devices. People want to be able to get information anytime, anywhere. When I started, we didn't even have a mobile app. It's a lot of change for people to understand what we're going through. They get it. They know that we want to enable them with all the information that they want, and we're putting stuff out there. The response has been pretty good.
Speaker 1: That's great. It's an interesting example of how these trends are ... Even kind of the most maybe boring companies are getting a lot of excitement out of mobile technology.
Thinh Nguyen: Well, you know, if you looked at just the industry in general, the landscape is changing. Even the demographics. You're getting a lot of Millennials who are starting to own their own homes, and they have a different expectation in terms of interacting with their servicer. They want everything at their fingertips. They're not writing in checks. Everything is digital, so that's our focus. Everything is sort of digital ready, device ready.
Speaker 1: Tris, tell us a little bit about TCF, then. Maybe some similar trends. Maybe some unique things there.
Tris Lingen: Similar to Thinh, TCF Bank is a midsize organization in the Midwest, so we're a $22 ... $22. $22 billion organization. On the retail side, deposit accounts alone are, like, 2 million deposit accounts, so it's a lot of accounts. It's a bank that's been around for a long time, so traditional banking, right? Brick and mortar. As the environment is changing, as people's expectations are changing, we're changing with that, also. We went on this journey a few years ago to really start to understand how do we have one identity for our customers. They were starting to come to us saying, "I do this as a retail. On the retail side, I've got online banking, but on the wholesale side, maybe I'm a small business account, and I want to be able to have one identity with you, TCF, versus multiple." Similar issues that many of you and all of us have had to address here on stage. So started this journey a few years ago to really start putting a partnership in place with an organization that could help us take us to that next level in that next digital banking transformation.
Speaker 1: Yeah, interesting. Definitely, as I listen to you guys, there's some common themes that come out, somewhat related to the bullets that I had there at the beginning around customer experience and security. Let's talk about some of those topics one by one. Around customer experience, who is responsible and who owns that in your organization? Who's really thinking about that? How is that managed? Does the identity team manage that, or is there some business partner that you work with that's thinking about that, and how do you partner with them? Can take anybody, or if, Alfonso, you want to kick us off again.
Alfonso Mancuso: Sure. In our organization, it's the business partner, but we work very closely with the various businesses for their customer base to understand not only the needs and requirements from the application team and what sort of services we're offering our customers and how to best suit and meet those needs from an identity and access requirement and also from a security requirement. We also layer that with guidance and governance to make sure that we're doing things not only up to policy but industry standard and really as secure as it needs to be.
Speaker 1: Interesting. So you're working with a business partner on that. Is that similar to Mr. Cooper?
Thinh Nguyen: Yeah. I would say technology, at least my experience, we're probably the worst marketers in any corporation. We tend to execute extremely well given directions and task. I think we're getting better from a user experience perspective of all the methodologies that's out there around design thinking. Historically, we're horrible at that. So we do work with our product marketing team. They're out in the front, center, with the customers. They're talking to them. They're doing interviews. They're doing surveys. They're doing calls. They're doing all kind of sampling, and we feed off of that. We work with them. We sit in with them on these sessions with real customers across all demographics and hear what's going on. So they are driving our product design. They're asking for features that we haven't really thought about for years. I mean, it's a different organization. It doesn't sit in IT. It's marketing, but product management. That's been great for us. Now, we're both accountable for the same goal.
Experience, as much as people talk about that being a buzzword or digital transformation being a phrase that's just been thrown around, if you talk to anybody, even yourself, as to how you interact with all your vendors, all your third-party transactions, you have a certain way of doing things. You want more and more and more. So that framework has really helped us. Having a separate group that really just focus on product design with the customer in mind, I think, has been tremendous for our team.
Speaker 1: How much does product management get involved in the actual selection of the technology and the underlying platform? Or is it more that they're just telling you what kind of experience they want to deliver and then you're really bringing to them the solution?
Thinh Nguyen: So, marketing folks, they are very creative. They are out there. They know what's available, things that we haven't even touched in terms of you talk about social marketing, products that's out there. They know it all. We get involved at certain stages, but they know a lot more than we think. They're out there doing a lot of diligence for us. I think that's helpful. They bring back at least a filtered set of, hey, what about this? What about that? What do you think about this company? It's great, having another arm in terms of technology, from a business perspective. The underlying architecture still kind of needs to be vetted, but I think they're smart folks that are out there.
Speaker 1: Cool. Sounds like you guys have a good partnership there.
Thinh Nguyen: Absolutely. Absolutely.
Speaker 1: Tris, how about how you guys think about customer experience?
Tris Lingen: You know, it's very similar to what Alfonso said and, actually, Thinh, too, in the sense that-
Tris Lingen: ... Alphonso said we're, and actually Thinh too, in the sense that we're working with our business product owners. And so within our organization, we work very closely with those product owners to really understand what their strategy is, what their roadmap is, and how do we help them be successful. Right? One of the things on my team that we talk a lot about is take the word no, out of your vocabulary. It's, "Yes, and how can we help you do it in a way that it is secure? And it is effective to really address what that requirement is." And in many cases for us, it's really reducing that customer friction. Right? As people are trying to change, or as people are requiring, or demanding that they change. They want to be able to interact with us differently. We have to be able to provide that or they're going to find somebody else who will. And so, that's kind of that yes mentality, right? So, how can we do it and do it in a way that really works with the business and helps us really understand things and secure them appropriately?
I would also say, and I echo what Thinh had said, is that the reality is for all of us that are in security in this room, there isn't enough of us in any one organization to be able to address all of the security issues. So, one of the things you really need is kind of that federated model where you have the advocates, Whether it be in your business line or your product lines. Where they're helping you think through what are some the roadmap ideas we have and what are some of the technologies that might help us get there. And that they're thinking about security also and that it isn't just an afterthought. And the more we can all do that as a collective whole, the better off we're all going to be because there just isn't enough capacity for all of us to go around.
Speaker 1: It sounds like in all of your organizations customer experience is just widely recognized as something that is important and it's prioritized. Have you ever been in a situation where you've been challenged to kind of show the ROI of a project that was focused on customer experience? Or has it just been just plainly obvious in all of your organizations?
Thinh Nguyen: I'll go first. I think at least for our industry, we do have J.D. Power Score, which is a great indicator of satisfaction from your customers. And you look out there, you know who they are. Right? USAA, Quicken Loans, they do great. And that's specifically, there's a section on just digital experience and customer experience within that score, where it's very material. And so that's one way we show ROI can make customer satisfaction perspective is, "Are we doing the right things based on what our customers are asking?"
From an initiative project execution, obviously you've just got to look at the economics and the investments, and what you're trying to do. But end of the day, a lot of that is soft, so you can't really measure revenue and things like that very accurately. You can try as best you can, but end of the day we do have J.D. Power and that tells a story for us.
Tris Lingen: When I think about that question, I think one of the things I think back to is when we started this journey three years ago, we went into it with an idea that this would be an enterprise solution for us. Right? So, talking about ROI and things like that, it really went into we're going to make this investment in this capability, and in this capability as an enterprise service, and recognize that that is a compatibility that has cost to it, but it has rewards at the end. Right? So, the customer friction is reduced and then we're also secure. I would also say, kind of echoing what Thinh said relative to scores, all of us have in all of our industries, some level of measurement of how satisfied our customers are. Whether it's an individual survey you're doing yourself or just industry trends. We're seeing this in the whole banking industry regardless if it's just more good servicing, or lending, or just banking as a whole. There is a lot of disrupters in the market and banking is shifting very quickly. And so all of us have to react quickly to those changes.
Speaker 1: Yeah, that sounds ...
Alfonso Mancuso: I agree with Tris. We echo a lot of the same sentiments. We may not have an industry score like J.D. Power or anything like that, but through surveys, and other means, we're able to measure customer satisfaction. And that's really the measure of the return on investment. And it is ROI as an investment, not ROC. And that's been the challenge within the business to let them understand. Yes, it's a cost, but you're making an investment. Don't look at it as an expense. Look at it as we're investing in the product to further the customer experience, and then in turn will grow the product line, and the business revenue. At the end of the day, that's all it's about.
Speaker 1: Yeah, that makes sense. I can imagine in some organizations it's a mindset shift to think about it that way. I'm actually going to pause right here on customer experience and see if we have any questions from the audience on this topic. We're going to talk about security and other topics as well, but I thought along the way if you have questions on customer experience, happy to have the panel address your questions.
Anybody? Up in the front here, if you could wait for the mic.
Tris Lingen: Oh great.
Speaker 1: Front row. Oh, we got two people. Oh, okay.
Speaker 2: Hi. We're in the process of operational readiness, and planning, and using embedding Okta in a suite of products. Are any of you doing something along those lines? And if so, can I talk to you afterwards? Because I have a whole series of questions.
Thinh Nguyen: Sure. I'll take that one, too. I didn't get the specifics, but in Okta, obviously, some of the SSO is pretty straightforward. Federation, a little bit trickier, given that you managing kind of a multiple ISPs versus the internet provider, but we do have used cases where we have third party, you call it, tools. Where we embed within our digital platform that requires SSO, embedded with them. So, then that becomes an API conversation where we're doing, the fact that we have the API management piece of it, real time API that now is in Okta to that vendor that is hosted within our framework. I don't know if that's the specific question, but that is another extension of used cases that maybe applicable especially for web and digital platforms where you're not building this from the ground up, you're leveraging a lot of tools in third party integrations with other products, so there's that.
Tris Lingen: We've actually done that, too. We're looking at and have put it in a suite of products. And so, you need to really understand your authentication layer and then the authorization layer, too. Because depending upon what it is that they're trying to do, it'll be a different authorization model potentially from time to time. So, yeah, we can talk about that. I'm actually going to throw my technical team out, but there are several people that are more technical than I, that could help with that conversation if you wanted to have a deeper conversation than I can provide.
Alfonso Mancuso: We, too, have the same. We have a combination of products that we leverage off before. And it's pretty fair split between home grown or internally developed where we're embedding the Okta technology of any leveraging some of the API products and I think it's the log in widget. But also commercial software SAS products where we're federating with the service now. For example, leveraging off as the IdP.
Speaker 3: This question is for Tris. I was curious. You mentioned that you were going through a digital transformation enabling customers to log in and digitally bank. And I think I read online that you're using a third party D3 banking for technology. I was just kind of curious. Did they not offer that this solution is part of their suite and how did you sort of come to Okta? Because I would imagine a lot of these solutions, well, sort of have single sign on embedded or customer identity back sys embedded. And so just kind of curious you're journey and how you found it.
Tris Lingen: Sure. So, you're right. We do use D3 for our online banking platform, which is one piece of our product suites, so it's not all of our product suites. So, to the extent, D3 offered an identity process. The challenge we had with it as an organization with any of them is that you're tied to that vendor then from that relationship. Where, what we wanted was more of a centralized identity management solution that we could plug and play the backsides to it. So just say, right, we decide to get rid of or we decide to switch to a different vendor for whatever the product is. I'm not tied to their identity management solution because as many of you know it's ... Especially in banking, you can ask your customers or you can have your customers make the switch to a new identity and a new identity solution. But if you think you're going to do that on an ongoing basis, that would be considered one of those friction points. And it probably wouldn't go over very well, so we kind of thought through it. That's the reason we went through that Okta. We wanted that ability to be centralized and be able to plug and play in the background.
Thinh Nguyen: I could attribute to that. I mean, at least, for our tech stat or platform, we take the headless approach. Meaning we're not going to be tied to a specific product and that's a big part of any diligent is, is it embedded in their product and you live and die with it? Or do you have flexibility to plug and play, switch, or add on or write on top of the SDK. So the headless model works extremely well because that's kind of what Okta focuses on. It's like you don't really need all that finance stuff, you can write everything back in through APIs, especially with all the newer stuff that's coming out. So, I think that's a consideration, too, especially if you want to maintain control of your product, which is what we do.
Tris Lingen: We've done something similar, taking a similar approach and we advocate the labor of extraction between what we offer from an application perspective and also consumer products. It does change. Right? Things can. And there's history of switching from one product off to another. Building an extraction layer with rich APIs that Okta offers and a lot of the other SAS offerings and the software space, allows us to do that. And again, we're not tied, not married to one particular vendor. We have that flexibility and can be a little bit more nimble in switching.
Speaker 1: That's interesting how each of you talked about that theme of, sort of, independence of the identity layer, but then the thing that variable is to what extent do you custom build on top of that versus use some out of the box tooling. And that is a trade off a little bit with speed versus control and a more ownership over that layer as you were talking about that extraction layer. So, that was kind of an interesting theme there.
Another questions in the back.
Palak: Hi. My name is [Palak 00:26:49]. I just wanted to ask from your experience of implementing more of a centralized identity solution for your customers. Obviously, a couple of key benefits, the user experience improves a lot and the operation and efficiency that people running the IT organization do see. Anything outside of that either you were kind of expecting that you will get in terms of benefits of having a single identity layer or a unified identity layer? Or were there other benefits that you discovered after, actually, you put in the identity platform in place and how it is serving you in terms of more than just recognizing an authentication layer or an identity layer. So, yes. Just to sum up my question, it's basically, what are some of the other benefits that you probably did not see coming, but you did get some benefits, if at all? And just outside of customer experience and the operation and efficiency, what was other key benefits of having a core identity layer or authentication layer?
Alfonso Mancuso: Okay. I could take that one. The biggest benefit is a single unified platform for managing that identify from the attributes using universal directory and the APIs in plugging into the various applications. One of the main benefits we've seen leveraging the Okta APIs is a rich registration experience that the user can do for self-service. There are tradeoffs because a lot of the challenges internally are adoption. Especially with more of a legacy applications than maybe using that are not on Okta or using different identity stores. And the migration path to get to a central identity, and then when you're there ensuring that it's a central identity, not that application A has its own registration path and application B has its own unique registration path and you wind up with two user accounts that either conflict or completely independent. And that doesn't really bode well for the user experience.
Speaker 1: Anyone else have a comment on that one?
Tris Lingen: Yeah, I'll comment on this one. And this probably kind of coming at it from a slightly different angle. I think one of the values that people underestimate is the amount of partnership you get with working with an organization like Okta. It isn't just that they've got great product. Right? But they're also deep in knowledge and understanding of what some of the challenges to different industries are and how to solve for the problem. Right? So, there's that. And just even looking at like a conference like this, with the 4,000 people that are here. It's the depth of the network that you can also have when you're working with an organization like that. I think that's a soft win that people underestimate and they focus a lot on what the technology layer is and I think some of those other pieces are just as important.
Speaker 1: It makes sense. So let's switch gears a little bit in the remaining time we have here and we'll get a little bit more Q&A at the end. But I do want to make sure we hit on security, in particular, and the security considerations as you are thinking about the customer identity platform from both ...
Speaker 1: ... as you're thinking about a customer identity platform, from both the perspective of how are you improving security for the user as well as securing your environment and making sure it's a secure environment that's protected against potential attacks and things like that? Tris, why don't you start us off on this one, given that you're CISO over at TCF?
Tris Lingen: Yeah, okay. Obviously, in banking, we take security very serious, and our customers' data and our relationship with them is very serious. So as we were looking at this and understanding what the requirements from the business were, we really wanted ... Again, I'm going to go back to the partnership word. We really wanted a partner that we could work with that would help us on this journey in understanding where we needed to go, where we needed to be nimble, where we needed to think differently in a way that we maybe couldn't as quickly in a legacy shop like what we have, right? That was one of our big pieces for really working with Okta, was ... Believe me, we went through the whole RFP process. We actually had a different journey along the way relative to that. It was really important to work with somebody who if there were, as with any large implementation, bumps, how do you fail forward? That you're not just paralyzed and the companies that you're working with are really understanding what your requirements are, and how do they take themselves forward with those? That was important to us, and I think that that's what helped drive us to Okta for this particular business purpose.
Speaker 1: That makes sense. It goes beyond just a checklist of different protocols ...
Tris Lingen: Exactly.
Speaker 1: ... that you support, right?
Tris Lingen: Right.
Speaker 1: Alfonso or Thinh, any other thoughts on securing?
Thinh Nguyen: I mean, we spent, I think, close to seven months with deciding what's the right play. That's not just demos or sales pitches and let's go. I mean, it's architecture team, info team actually kind of pulling the covers out and looking at how the code is being written. The transparency of how to protect us as a customer, as we onboard, the integration, the capabilities, all the features. I mean, we went to that extent because as we went through the analysis two years ago, one of our other considerations, they got breached. Not good, right, when it comes to this platform, at least for us. 4 million customers. We're not going to have that situation. For us, it's huge. Deep dive. Ask the questions. Get comfortable. That's just the product set. For us in terms of building the brand, when they see that they're logging in with Okta and at this ... Two years ago, it's different now, the brand of Okta is out there. They know other big companies are using it, and they feel a lot more comfortable, and they know that they're safe. That perception alone, it's going to help your product.
Alfonso Mancuso: I mean, it's all about security, right? We're securing all the different layers. It's not only the applications, the customer and patient data that's contained within them, but it's protecting the brand, the company's reputation. From an IM perspective, it's securing and protecting the identity. My CISO is quick to remind me that all breaches are access-related issues. Now, that puts an extra stress on me, but he's right. It's about who can have and who has access to what. Unless that layer of security is done correctly, then we're introducing unnecessary risk, not only to the customer. Especially in the healthcare industry, that could have pretty serious consequences.
Speaker 1: Do you find that security from an identity management and authentication, is it top-of-mind for your developers? Or is it something that you, as the identity team, kind of have to go and push the agenda around? Developers mainly thinking about code vulnerabilities and things like that?
Alfonso Mancuso: It depends on the developer, and I would question whether they're even thinking about code vulnerabilities to think with. It's a combination, right? It's really a maturation process. Everyone has to be security professional nowadays, from the developer, to the administrator, to the infrastructure architect, to the security engineer. Especially the security engineer.
Speaker 1: Any other things on that?
Tris Lingen: I would agree. I mean, again, it kind of goes back to what I said earlier. Nobody has that large of a security staff that they can be involved in every security decision. So the more you can have your advocates in your development teams and your infrastructure teams and all of the layers, it's very important. One of our number one jobs, at least in my team, is really being that prophet out there, saying this is the goodness that comes from doing this, and helping them learn that or understand that. Then, echo what some of those thoughts are.
Speaker 1: We'll open it back up to the audience. Any other questions for the panel here on security or any topic?
Speaker 4: Thank you. In terms of the unified customer profile that identity management we are doing ... I'm from Nordstrom, and I have a use case. In terms of how well Okta's user model lends to a user as a shopper and a user as a supplier admin managing the stuff, if we were to have a single user for this and have a unified user experience, how well does Okta's user model link to it, in your experience, if you have dealt with?
Alfonso Mancuso: That's a tough one. We were able to get around some of those challenges by defining what our security boundary was, and we wound up implementing separate Okta orgs for patients versus non-patients. Now, we extensively thought about combining and going to one org. The overhead's less. A lot easier to manage. However, we realize that the true boundary is that organization. Now, that doesn't mean that it can't be done within the org. It really depends on what the identity is. In the example you give, the shopper versus the buyer, I look at those as the individual consumer versus the institutional. More times than not, the institutional is not going to have an identifier that is personalized to them. It may be issued by their company. In that case, they can coexist in one org. In our case, the challenge was that the provider or the doctor could be a small practitioner. He or she, they don't separate their personal email address from their work email address. They don't have the extensive capabilities as a corporate customer would have. We felt that the risk was too high in keeping the email address as the identifier common across the two, and the resolution was to separate the orgs.
Speaker 1: Any other thoughts on that one, or should we get another question? Good question. Yeah, I'll comment on that, as well, this question of what is your boundary around an identity is an important one around how you architect on Okta. We work with customers around different architectures on Okta. Alfonso mentioned having a separate org. It's generally something that we'll do in more complex scenarios. If you didn't know that that was a possibility, that's something that you can use Okta in that way, and we have different ways of connecting the orgs and things like that.
Speaker 4: In that scenario, does that count as a unified customer?
Speaker 1: Well, you can unify the experience of the user. I don't know if you want to elaborate.
Alfonso Mancuso: You can. The question you need to ask is, is it a unified identity? Just because it's the same person ... My email at work is different than my email at home, or my identity at home is different than my identity at work. I don't mix the two. That's really the question. Again, that's why it's difficult to answer. We did go down the path of one single org. We felt, even with the application development teams, there would be too many hoops to traverse in order to accomplish what we wanted. At that point, it's not as secure as just splitting the baby in half, and that's what we wound up doing.
Speaker 1: Any other questions? Well, any final closing thoughts on customer identity and access management, what it means to you and your organization?
Tris Lingen: I'm going to do kind of a ... It's going to sound like a plug, actually. When we started this journey with Okta, like I said earlier, there was some learning curves for both our organization and Okta. I really have seen that Okta and us together have failed forward. I think that that's a really important thing to understand, that this organization is growing along with all of its customers in this space as it continues to morph very quickly. I think that that's very important.
Thinh Nguyen: I would say we all have to take risks and make bets, and that's part of our job. It's no longer try and do it ourselves. It's all about the innovation is really not from the ground up. It's identifying the right set of tools that's going to enable your business partners to succeed and the company to succeed. I would say when you go through this process, especially for prospective, spend the time upfront. Get all the answers out there. Ask all the questions. Part of our learning was we thought we were pretty smart ourselves when we started the process, but we did a few things the wrong way, because we didn't consult. You really need to rely on the Okta team to help you design it the right way for your use cases. They're going to be there every step of the way, at least from our experience. We had a big launch day. I mean, 2 million customers on one day to turn over a digital platform. I mean, it was tremendous, right? The thought of our command center seeing just issues. It was non-event, right? That's what we wanted, is a non-event when it comes to this stuff.
Alfonso Mancuso: For us, I mean, you heard the word. It's partnership, partnering with Okta and extending that partnership through the app dev team and the business is essential. We communicate constantly, often. We're in constant contact, whether it's to resolve an issue or to understand how we can leverage the product and the services to our advantage. That's really key. We don't want to be just another Okta customer. We want Okta to be a partner with us, and that's what we've done.
Speaker 1: Great. Well, thanks, everybody, again, for being on this panel for us and sharing your thoughts. I hope this was a valuable session for you as you explore your customer identity use cases, as well, and partner with Okta on making it happen. Thanks a lot, everybody.
Customer Identity and Access Management (CIAM) is too often limited to a small set of consumer scenarios. This session looks at how organizations have leveraged CIAM to deepen their relationships with a broad spectrum of customers, businesses, and partners. Learn from industry experts on easy-to-implement scenarios that any organization can capture.
Speakers:
Alfonso Mancuso, DIrector, IAM, LabCorp
Thinh Nguyen, SVP of Information Technology, Mr. Cooper
Tris Lingen, CISO, TCF
Rohini Kasturi, VP of Products, Verita