Oktane19: Roadmap: Lifecycle Management
Transcript
Details
George Kwon: I'm George Kwon, director of product. I have the privilege of being here today representing a team of product managers, designers, engineers, behind the Life Cycle Management product. This is really an exciting opportunity to tell you a little bit about this product, and where it's going. And really to start a conversation. Right? That's what this is all about. To share how we are thinking about your pain points, how we are thinking about where the product needs to go, so that you can tell us and give us that feedback and we can create this great product and this movement together.
George Kwon: A quick slide here on safe harbor. I am going to be talking about roadmap and future things, legally is not guarantees to deliver things in the future, blah, blah, blah. What I want to cover today are a few things. So there is a mix of people in the room here probably some existing customers. Raise your hand if you are an existing customer of Okta. Wow, most of the room, that's great. Maybe you are a prospect, you're considering buying Okta. A few hands.
George Kwon: So, I want to cover briefly what is Lifecycle Management. We had a great 101 session this morning. I'll talk a little about why we built this product, the use cases. I'll touch on new capabilities. Things you can take home today and use in your environments to improve how you manage users and their life cycle. I'll talk about near term road map, and then finally a chunk of time at the end to cover an exciting investment we are making in workflow. Todd touched on this morning and I would like to go a little bit deeper. We will have someone come up, Andrew, from the team to give a quick demo there and then we'll close out with some questions.
George Kwon: So, I want to quickly survey the room here. How many folks are interested in lifecycle management because you purchased a new Cloud app that needs provisioning? Box, Office 365? Okay, how many folks are trying to improve their day one onboarding experience? Wow, that's a big pain point for folks. Compliance or government needs, trying to pass audits and automate that process? Trying to retire maybe a legacy system? Is that on people's radar? Okay, good.
George Kwon: These are all things that we have top of mind and we are all in this room because we envision this future around a more efficient, modern, agile IT. Use great day one experiences, frictionless access, but secure, auditable, compliant, more sass, less maintenance. These are all things we aspire to. But this is hard as you all know. Life cycles are complicated. You've got different user types in your organization. They're moving, they're joining, they're leaving, your acquiring companies. This business process is a lot to handle.
George Kwon: All of us in this room are familiars with kind of the challenges with identity debt. You have legacy systems, existing business process, your budgets aren't getting any bigger. You've got custom code and integrations lying around that you are scared to touch. If it's not broken, don't try and fix it. These are all things that make achieving this modern future challenging.
George Kwon: So, life cycle management is really set out to help you with this problem. To help you modernize, to help you deal with some of these challenges. And we do that by providing a few things. The first is helping you build a single source of truth for your users, for your identities, your groups, your roles. Incredibly important if you are going to begin this journey down life cycle management. The second is managing those users groups roles at scale. Your organization might be hundreds of people, thousands, tens of thousands, hundreds of thousands. Managing that in a manual way doesn't scale, it is going to be error prone. So, we are out to help you automate how you manage your directory.
George Kwon: Finally, all of those resources, applications. We talked this morning about advanced servers, other resources. How do you connect that to this life cycle so that you are doing less management in individual systems and things are flowing down stream. And finally, we do this for any user. We are really out there to help you with your employees, your external users, your customer identities.
George Kwon: As I talk about the road map, I wanted to highlight two themes and types of features that you are going to see. The first is what you kind of know and love about Okta. I hope. Which is a lot of our out-of-the-box feature, our policies, our rules, our integrations, prebuilt, maintained, admin configurable out-of-the-box. But Todd this morning talked about an important movement for us as product team which is about creating an open platform. The feedback we hear time and time again from customers is, "Allow me to do more. Make it possible." For that reason, a big focus of our roadmap this past year has been giving you the power to customize through hooks, APIs, and standards.
George Kwon: So, as I go through this roadmap, I hope you'll see these two types of investments that we have been making both this past year and going forward. So, I'll dive into these three topics and talk a little but again about what we do, what's new and what's coming. Single source of truth. Our vision is really to connect to any HR system, any source of truth of your identity data. Provide a Cloud directory that can be standalone, can serve as a meta directory to consolidate different identities, and help you manage synchronization so you don't have to think about it. Many of you are familiar with UD, for those of you that don't know, flexible users group, schema in the Cloud, easy to manage, easy to customize.
George Kwon: We can connect to any of your existing sources of truth. AD as you all know, multiple ADs, LDAP, your HRIS, maybe writing back to AD. We provide admin interfaces to manage your users, and self-service interfaces for your end users as well. We have a series of out-of-the-box integrations to directories and system record that you can import from and master from that are pre-integrated maintained by Okta. If you have a system that is not in the OIN, we provide again those options to integrate. We have a user's API, a programmable interface for user management into UD. We have an OPP agent which has a skim interface that can sit next to your prime message HRIS or directory. These are all options to really connect anything to Okta. Any systems of record.
George Kwon: When you connect those systems is not just about the integration and calling those APIs, it's about orchestrating identities sync and making that easy for you guys. So it's mappings and transformations, marching rules, all these out-of-the-box features that attempt to make identity synchronization easy. In 2018, this past year since the last Oktane, the team has been really hard at work. We invested in more systems of record, more flexibility, more customization. I want to go some of these features right now.
George Kwon: CSV directory is now GA and can sit next to any file system, pick up CSVs and use that to generate incremental changes to your user directory with all those same great features around mapping et cetera. This is GA use it right now if you're a Lifecycle Management customer. Import scheduling, just a small detail but a huge pain point for our customers. Schedule any time of day, hour, specific time. A lot of our customers say, "I want to run imports after the work day is over, overnight so that I have a chance to catch your shoes in the morning." This is EA, something that you can use with workday in our HRIS integrations, coming soon for AD and LDAP.
George Kwon: Another small detail but important pain point, ability to clear and confirm users. You ran an import with incorrect mappings, you want to start over. This is GA you'll see it right next to your import button.
George Kwon: Finally, advance import marching rules. As our customer base is grown and you're a multinational organization. Oftentimes you need to rely on other unique identifiers and you want to match on more than username or email. So the ability to march on employee ID, or any other identifier, is now possible in imports, and this is also GA.
George Kwon: Now, we can't build all these features, and we can't build every feature. We hear a lot of customers who want to do more in this import process. For that reason we've released in EA support for what we're calling Import Inline Hooks. So in any import process, you can insert your own custom code. So if your development team you write some code, put this in a lambda. And you can complete use cases like auto generating identifiers according to whatever logic you want. Add numbers, middle names, et cetera. Resolve conflicts as they happen through your own custom logic, and maybe even augment a profile or update a profile. So again, in this theme of opening up our platform, giving you the out of the box features, but letting you customize, this is EA.
George Kwon: Looking forward, as more and more customers rely on us for their imports and Okta as a system of record, we're investing in speed of our imports and scales, putting millions of records, better monitoring and control of what's happening in your import jobs and having visibility into failures, continued investment in hooks to open up the platform and provide those abilities to customize.
George Kwon: Managing the directory at scale: Another huge challenge that organizations face and we provide a few new capabilities here that I like to talk about around Self Service Automation, and again, that depth of customization. Many of you may have already be familiar with self service registration, a great out of the box option for your external users most likely to register for access. This is EA.
George Kwon: Coming soon in the coming months, again, an inline hook to customize that registration process. So with your custom code, you could do things like validate an email address, is this a partner identity, and is it coming from a domain that I trust? I may want to add an approval process for the registration flow. These are all be made possible by this registration inline hook. This is coming soon.
George Kwon: Group rules: This is a capability that we see immense adoption almost across our entire customer base. Group rules now supports adding multiple groups to a single rule, to help you cut down that management aspect. We've also created a new UI as people use and have adopted this feature. We now support search, basic thing a lot of people are control effing to find their rules. We have search, we have a collapsible UI to hide details. Group rules now supports up to 2,000 rules. So this is what big ass across our customer base. We've lifted raise that limit, and we're seeing great adoption around this, please use this wisely. And this is GA.
George Kwon: So we've always been good at mirroring that identity lifecycle from your HR ideas. A terminated user gets deactivated in Okta. But as we've seen more user types in our customers put more user types into Okta, we've seen a need to be able to create your own automation and workflow around those life cycles. And that's why we built automation, which is EA as of today. This is a simple interface to build a, If This Then That rule. A couple use cases that we support: Contractor compliance, you have contractors where you want to automatically suspend their account if they're inactive, provides you a backstop in terms of access. That is possible today with automation.
George Kwon: Notifying users ahead of password expiration, cleaning up your directory. Maybe deactivating users based on another attribute that you bring in from your HR system. These are simple rules you can configure in an admin UI, and add more automation around your identity lifecycles.
George Kwon: Looking forward, we already have some conditions and actions in EA. Coming soon additional conditions and actions to again broaden the usage of this capability. Taking action like moving people into groups, updating their attributes, in addition to managing their life cycle, and this is coming soon and Q2 in Q3.
George Kwon: Self Service for applications: This is now GA, and has been for some time, the ability to enable self service for any application, You can require or not require approval. This is a new capability. We get a lot of folks who say I give birthright access to a lot of applications, but I want for some applications people to request them. I don't need an approval, but they only get it if they need it, and that helps save license costs. So approval workflow, on top of requests, and this is all GA.
George Kwon: Finally, again, on the theme of customization and making things possible. There are a lot of events being generated around Okta and UD; users being created, people being granted applications, moving groups. We have a lot of customers who did interesting things with our system log events, they would pull those events to drive downstream workflow. With event hooks, you can now register for a notification. Again, customize a host of integrations and downstream workflows. For some folks, that's creating a ticket when a new user is added to their directory for some IT tasks. It might be notification or alerting when your AD agent is down.
George Kwon: A lot of different use cases this has been in data, and we've gotten really good feedback from customers and seen a lot of interesting use cases. This will be EA in a couple of weeks after Oktane, which is great. These are just some of the events that you'll be able to subscribe to many of the events that you're familiar with in system log, and this will increase over time.
George Kwon: Finally, I want to touch on connecting to all those resources, connecting them to that identity lifecycle, driving more automation. Oktane supports provisioning to over 190 applications. That's user provisioning, create, update, delete, and for subset of those applications supporting group sync as well.
George Kwon: Over the last few months since last Oktane, we've added 61 new provisioning integrations through our SCIM program. So these are ISVs thanks to your pushing and cajoling, saying you need to support SCIM if you're going to be my customer. ISVs coming to Okta implementing SCIM and getting that integration the catalog and over just the last year 61 new provisioning integrations, which is really amazing.
George Kwon: We've added depth to some of our top integrations, improving group push to support linking and pushing into existing groups. We've added SCIM discovery to a number of applications that you see listed here. So constantly improving those top integrations, making sure they support the depth that you need.
George Kwon: We have a SCIM app wizard, so many of you may have internal applications that you want to provision to. So if you can support the SCIM standard, create that SCIM interface, you can add that application directly into your org and start provisioning to that application. And this is GA.
George Kwon: Again, with event hooks, really the possibilities are endless in terms of how you might drive downstream workflow into other resources, applications directories, or even human workflows. So I encourage you to play around with this and come up with more ways to connect more things to that identity lifecycle.
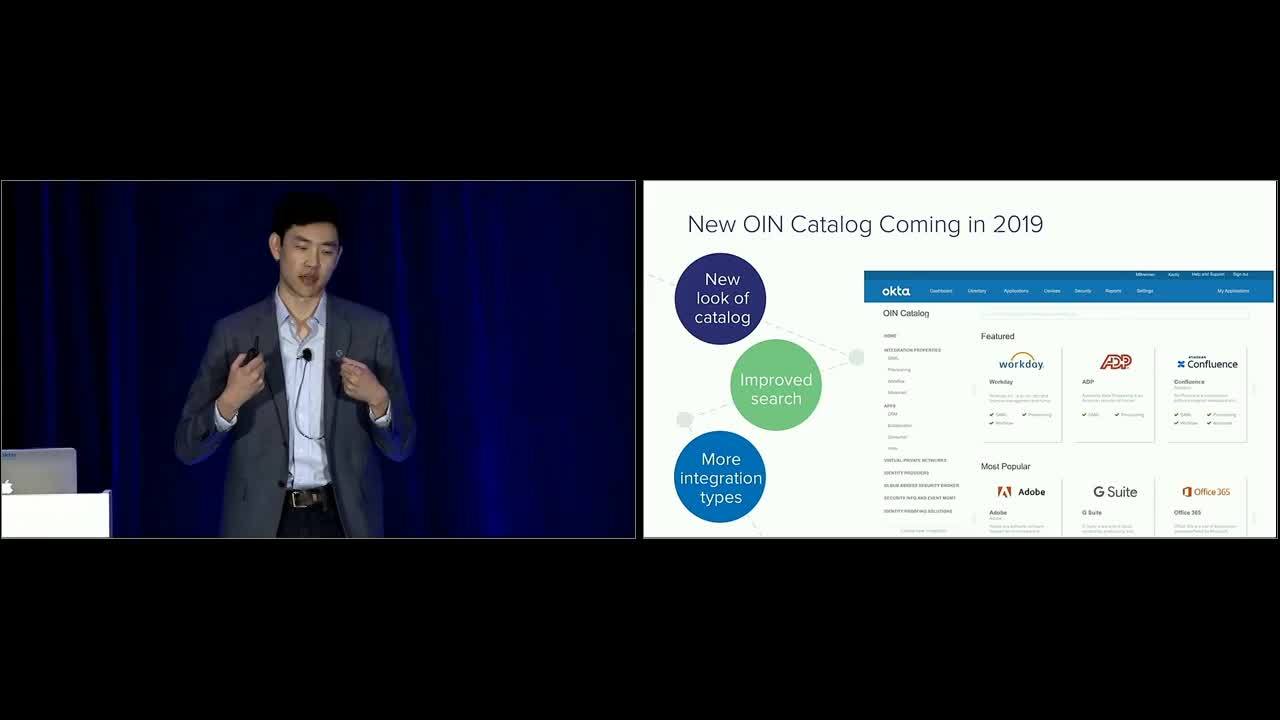
George Kwon: Finally, later this year, we're hard at work at designing a new catalog. You know, a nice enhancement just we get a lot of complaints around, What do you support? What applications are in the ION, what did they do? Do they have these capabilities, these capabilities? We'll be launching a new catalog that will be publicly facing, which will really help your internal teams know and drive adoption of applications. This will be coming later this year.
George Kwon: So again, build that single source of truth with UD and these deep integrations with systems of record, manage your directory at scale with automation, and connecting all those resources to your identity lifecycle. Just a few of the strategies we are putting into your hands to help get control of those user life cycles. features that you can use today in GA, EA go home, try these out, take a picture, ask your CSM and take advantage of these new capabilities.
George Kwon: Coming soon to EA, event hooks and some new automation is coming later in Q2, again, more great functionality to take advantage of. Some beta programs: This morning the team spoke about the identity engine, and if you think about that capability is a flexible, programmable platform to manage the creation onboarding of users, this can be a really powerful tool to create those external user facing experiences for B2B and B2C capabilities that you should take a look at and take advantage of and there are other sessions that go deeper in these areas.
George Kwon: So really proud of the team in what we've built, in what we've been able to deliver in the last year, but as a product team, we're not satisfied. So these are some images of our ideas board. Hopefully, you guys are all familiar with this. We look at this every week as product managers, as engineers, because this is how we stay in touch with your problems. This is how we get a sense of how we can do better. Frankly, this ideas list is long. We know you guys are struggling with custom business process. To give some example.
George Kwon: I want to provision users when they're stage not when they're active, or I don't want to disable uses in AD, I want to move them into new OU, or I want to deactivate but at a certain time of day. Why can't you support this application, or when am I going to get integration to that application? In general, and taking a look at this feedback, we've taken a step back as a team. What we're realizing is that there are so many business processes ingrained in Lifecycle Management. This is customer specific process around your users and groups and applications. We need to figure out a way to deliver automation around that business process in a faster way.
George Kwon: But we need to do that in the right way. Legacy identity management products have been very good at being able to codify and automate any business process. You can take a workflow engine and program into that any process. But it's hard to maintain, hard to use. It requires specialized skills, it breaks, your business process changes, and now you're hiring professional services. So when we built Lifecycle Management, we took a fewer set of use cases, but focused on out of the box, easy to use, maintain. But again, we can't support all those detailed business processes. With hooks and custom code, we've done a little bit better. But again, we're not satisfied as a product team. How do we automate any business process around a life cycle of your users and deliver SAS easy to maintain, easy to maintain integrations and workflow? Can we achieve this in a modern way, and can we move this industry forward?
George Kwon: We think we have an answer. We think that answer is low code workflow, automated investment about a month ago in a low code integration platform and we're really excited about this technology. We can automate any business process around your user lifecycle, around provisioning, around onboard off board, off board. But do that with supported connectors in a low code way that doesn't require engineers. That can be your custom business process, but leverage, best practice and community reuse. So we're really excited about this as a major investment in the future of Lifecycle Management, really taking the product to the next level and allowing you to solve more complex Joiner, Mover, Leaver management of your SAS compliance workflows, et cetera. We're really excited to see what you can do with us.
George Kwon: I want to get Andrew up here to do a quick demo of this technology. You saw a brief glimpse of it this morning, but really a deep dive demo is the only way to do it justice. So I'll hand it over to Andrew.
Andrew: Okay, thanks, George. As he indicated, actually, our acquisition is about three weeks old. There's a bunch of my fellow workflow teammates here, and this is our 12th day as Okta employees, and we're pretty excited. We've been diving right into this problem. Thank you.
Andrew: So there was a demo this morning as part of the keynote. As George mentioned, everywhere he talked about there being hooks, and being able to add custom code, we want you also to be able to plug in custom solutions, infinite integrations, without having to write code. So this is our flow chart view. So this is just the simple flow chart that shows what one of these custom automations would do. Of course, they can start with any of those hooks that are supported in Okta.
Andrew: So in this case, his is for an Okta organization I have that assigns G Suite to users. Instead of using the built in Okta provisioning, I want to use a custom provisioning. So anytime users are assigned to G Suite it's going to run this custom code, although I've written it with no code now, after I demo with, I'll go back and show you how I built it. But it's going to basically find out information about that Okta user. Then based on the attributes of that user, like whether it's a full time employee or a contractor, it's going to take two different paths. For a full time employee, maybe it just immediately creates the user in G Suite, looks up their department, and then adds them to the proper group in G Suite, and then composes and sends a slack message to the people who need to know that a new user was added.
Andrew: Again, this is all completely customizable. Then the other path for a contractor, maybe it's going to store that data in a table and then compose an email that starts an approval process that could also be customized. So let's take a look, this workflow is actually turned on. So let's switch to my Okta org. I'm going to go ahead and assign G Suite to a bunch of users. I have that web hook turned on automatically by creating that workflow. We're hard at work at making sure we can put our engine and our UI right within the Okta experience. So you'll be able to ... you won't have to use a code window to set up these web hooks, you just add, drop in a card and turn it on, it'll just automatically work.
Andrew: So when I go ahead and I make these assignments, and I confirm. Okay, now, let's switch the slack, and here's my slack group. You can see, it actually took slower than it took earlier. But you can see I already got two messages, because two of those users that I provisioned we're full time employees. You can see these are customed, it actually gives the name and the department and their title of those people. So let's take a look at the flow that actually built that. You can see, this is the design view. In this view, you see everything that's happening in the flow, you see all of the inputs to each step, and each step has outputs and it runs from left to right.
Andrew: So the first thing that runs is the web hook. And when the user is assigned to G Suite, we get the date and time and we get the message and we get all the information about the admin who assigned it and the user who was assigned. I can take and pick up any one of these outputs and drag and drop into a future step. That's how I'm able to easily do things like look up that specific user, and then get more information about them like their first name, their last name, their email, et cetera. As I scroll over to the right you can see that I do the, Create User step there, I've got the conditional logic I add user to the right. I look up the group, the user and add them to the right group based on their department, which was just dragged over from the left, and I can pose and send that slack message.
Andrew: We actually keep track of ... you opt into this, and then you can actually click on flow history. Then you can see here are the three records, and if there were 500 Records, there would have been 500 things that ran. You can see, I could actually click on these and see the actual data that ran through each step. So I can see the message that was composed and the names and in this case, let's click on the second one.
Andrew: That was also a full time employee, and the third one was one of my contractors and I could see it didn't run the true step. It ran the second branch, which was the create that row, compose and send the email. Next to each step, you see the green check mark tells you that it ran successfully. It tells you that ... I can't read that from here. But it took less than half of a second, it looks like to run that step. If there were any errors, I could debug it from here. So it's just really easy environment. I could replay a single card, or I can test it with different values. So as you're building it, you can easily just try different things out.
Andrew: So we're pretty excited to deliver this into Okta, and that's a little teaser of what's to come and also focusing on Lifecycle Management scenarios to begin. Thank you.
George Kwon: Okay, how cool is that? Super exciting. Again, team has been here two weeks, so we asked for your patience. But we are hard at work integrating these products into Lifecycle Management. A few things that get me really excited about this: Your custom business logic but in low code, easy to maintain test debug, the feedback we get about provisioning and our product today, how can I see what happened when there's an error I need to be alerted? How can I see the data flowing through the system? All of those principles are present in this product, and are incredibly powerful.
George Kwon: A host of connectors not only to automate account creation into your SAS but for alerting and ticketing. This morning, you saw a little bit of a security incident response use case, these pre-built connectors but also the ability for you to build your own connectors. For the ability for SIs and our great partners to build out connectors. Getting past this problem of, when will Okta engineering and the product team put my connector on the roadmap? So another really exciting capability here.
George Kwon: So like I mentioned, this year hard at work at integrating these products. You'll see this as part of our Lifecycle Management product, and helping you automate more Joiner, Mover, Leaver as well as provisioning. As we go forward with this integration, you'll certainly see more applications of this local workflow across the Okta product, integrating with the Okta Identity Cloud for use cases like security and customer identity. So stay tuned, it's going to be an extremely exciting year for the product.
George Kwon: With that, I'd like to ask you all to quickly go to Georgekwon.com and fill out a survey, as I'm about to launch into questions that the one thing I hate about these sessions is that we never have enough time to answer everyone's questions. So if you want to give feedback on what you saw, please go here. There's a 32nd form to fill out and leave us your email address so the team can connect with you. With that, I'll take some questions.
George Kwon: Up here, yeah.
Speaker 3: As a first time comer for Okta, I'm very excited to joining this group of people and the team who seems to be very caring about the customers. So my question for you is that we joined Okta planning that we're going through the single sign on tool. But my question here was as a first timer is that what is your future kind of vision on Lifecycle Management part of it, are you planning to be full blown IGA service providers or you are just happened to be Access Management vendor who wants to provide subset of the IGA capability in long term?
George Kwon: Yeah, I can answer that. So as you all know, like our DNA as a company was creating this new category called IdAS, which coming out of the days of CA side minder, identity minder, and Oracle Identity Manager was a out of the box set of capabilities across the identity problem statement delivered itself, and that was our DNA. As we've matured, and our products matured, our customers are asking us to do more, right? Don't just integrate with AD and be a bridge to the cloud, actually be my system of record, integrate with HR, do more provisioning, give us some basic access request.
George Kwon: So in general, we're very customer focused and we let our customers take us to where they need to be, as opposed to drawing lines or entering specific categories. There are folks I'm sure partners in the room who do IGA very well and we partner very closely with them. At the moment, that's not our core business. But our customers take us to amazing places. We've been at this for five, six years, and we hope to evolve our product in the direction that our customers need.
George Kwon: Any other questions around the room? I see one in the back corner? Barely because I'm being blinded by the slide. But-
Speaker 4: Do you have any plans to be improving the workflow for disables? So for example, the use case would be on an HR termination, we would want to disable all accounts but not de-provision them. The suspend workflow that you currently have doesn't quite meet our use case or what we call standard use case in most organizations we're consulting with.
George Kwon: Yeah, that's a very common one in Salesforce. You want to freeze accounts, you don't want to deactivate them because you lose your leads or inbox or collaboration you want to suspend, not transfer those files. That's certainly our vision, and the use case we have in mind as we're talking about low code workflow, being able to choose what actions you take when you're off boarding an application to suspend transfer files, and then deactivate to reclaim the license, those types of multi step workflows and the choice to pick the action is absolutely where we're headed.
George Kwon: Any other questions? Quiet room, I expected more. Got one right here.
Speaker 5: Alright, so this is already in the product, I apologize. One of our biggest issues with the De-provisioning is reassigning assets to other employees. So like a manager leaves, that employee had a bunch of stuff in a random application. A lot of apps have the ability to reassign privileges, but other times we basically just have to like give someone's password to their boss so they can go in and get out the information. Is there any potential way to like a lot people assume de-provision users or something for some period of time?
George Kwon: That's a good one. You know, again, there's been asked to transfer leads and files and things like that, but I think you're actually speaking about impersonating access, et cetera. That's not something that we're focused on at the moment. There are some ways to get around impersonation, but not ones that I would recommend.
George Kwon: Over here.
Speaker 6: Can you speak a little bit about customer Lifecycle Management? What do you guys are thinking in terms of customer identity management?
George Kwon: Yeah, customer identity. Yeah. So there are a few pieces there. One is with customer identity, typically, you're building your own customer facing experience, and in general, that typically involves a registration experience. So this morning, you saw a great demo around registration with progressive profiling, all powered by the identity engine, that's really our focus and investment in that area is giving you the tools and that platform to build a customer facing registration experience, login experience, et cetera. So while I didn't cover that in detail, that is a key focus and there are other sessions around customer identity specifically, that will cover kind of those experiences throughout a customer lifecycle. Was there something specific around customer list?
Speaker 6: On boarding of customers, because I think that was one of the things you're trying to get our hands around, provisioning, de-provisioning, onboarding, just like you talked about the HR, both the integrations, and the whole life cycle of employee in some sense, like the summer was good for the customer as well.
George Kwon: Okay, and you're talking about user, not your employees, your workforce, but your customer identities.
Speaker 6: Yes, exactly.
George Kwon: So I think it depends on the application. A lot of folks, for customer identities are not our self service you're getting access to an application or service versus have tightly controlled managed identity in a directory. So when we typically talk about customer identity, it's building the self service experience. Around lifecycle we have had use cases like cleaning up inactive accounts that have haven't logged in for a year to reclaim the identifier. That's something that actually automation is capable of handling. So you could set a rule or an automation to suspend and then delete inactive accounts. People use that to keep the directory clean and recycle identifiers. But just one example of how people manage your customer identity.
George Kwon: Typically it won't be linked to an HR system. So that's why people kind of use these other ... Sorry.
Speaker 6: So the CRM system, and that's what we're trying to figure out how that works, and how do you keep it like active and synced.
George Kwon: I got you. Yeah. Again, I'll use the example of building a workflow around that. So you might have an event around a customer in your CRM database, turning as a customer no longer being a customer, and having that drive and automation back into Okta to suspend and disable that account, that sort of If This, Then That workflow, I think, is maybe what you have in mind would be very possible with what we're working on in the future.
Speaker 6: Thank you.
George Kwon: Yeah. Right across way.
Speaker 7: Hi, we master our employees through Workday into Okta, works great, terminations doesn't work great. There's a gap between Workday and Okta that has persisted, where only the term date comes over to Okta, it's insufficient for scheduling of terminations. We have a lot of IP we need to protect and we need it protected when we want it protected. So RTS yeah, happens immediately sometimes too immediately. Non RTS happens day after too late. Anything you're doing about that?
George Kwon: If I'm getting your question correctly, in non RTS scenarios, sometimes the termination happens according to very specific time zone and timestamp. There are some enhancements to address that to terminate at a specific time of day.
George Kwon: But more what I'm hearing is that you might have additional or different business logic around the state of the employee that you want to bring in and drive it different workflow around. That's different from what our integration does today, is that right?
Speaker 7: We just want Workday to master determination, and right now it doesn't. It says the day, and in a non RTS situation, you do it tomorrow. That's too late.
George Kwon: Got you. From a timing perspective. Let's take that offline, and let's chat up front here so I can understand it in detail. I might pull in some other folks as well.
Speaker 8: Yeah, I have a quick question about the Self Service ability for users to request access to a service style. It's a great feature, but we need the ability to scope which group can request access to an application. Is that something on the roadmap?
George Kwon: Yeah, the Self Service Access Request roadmap is something that we're looking for a lot of feedback around. On one hand we have customers telling us they want to leverage their existing ITSM system them to build out infinite complexity around that workflow. We have heard that request. So scoping requests, we have heard round, being able to request access to different resources groups and things like that. We don't have any near term roadmap around those enhancements. But it's something we would love to continue to engage with you on and figure out what the right balance is of doing that in Okta versus outside.
Speaker 9: Provisioning all these things are great. Is there any change to the password self service?
George Kwon: Is are there any changes to password self service, is that the question? And specifically password reset?
Speaker 9: Password resets, forgot Password because the policies in password self service like for example, still it uses a legacy, a very old challenge questions, and none of them of your factors, which is in Okta to MFA is not part of that. Those two things are very disconnected, and user behavior. Is there any change coming up?
George Kwon: Yeah. So I can speak to that briefly. And then I'll probably introduce you to a colleague of mine. But one of the goals of the identity engine was to address that. When Okta was first built, we were very password forward, and MFA was always second factor. As a result, a lot of reset flows and enrollment flows were kind of baked into that logic. With the identity engine investment, we're much more agnostic about separating out credentials and factors from primary secondary off and being able to drive enrollment challenge and recovery in a more flexible way depending on what factors you're using. So short answers absolutely that's a pain point we're addressing through the identity engine. I should introduce you to some folks to cover that in more detail.
George Kwon: Great.
George Kwon: One minute left. So maybe one more question. And then we'll wrap up and head to the afternoon session. Anyone else?
George Kwon: One more.
Speaker 10: Thank you. You mentioned when we do use dynamic groups, proceed with caution. I think we've been burned by that. Because groups can be used for so many different things such as policy, push groups, things like that. Is there a roadmap where we're going to be able to see a matrix of where those groups are being used?
George Kwon: That's a good question. And I am not aware of any specific roadmap around that, we should talk to the universal directory team. I do know that visibility and reporting around groups and policies and who is in what, is a pain point that the team both UD and reporting are looking at another area of pain around that is around a hierarchy and group structure to help alleviate some of that as well. So I know those are a couple areas that the product team is looking at, and I'm happy to introduce you to those PMs.
George Kwon: Cool. Thank you everyone for attending this session and enjoy the rest of Oktane. Thanks.
The challenges of managing the lifecycles of your employees, extended enterprise users, and customer identities are larger than ever. Customers need more extensibility and customizability. Come join us for this session to listen to Okta’s vision for how the Lifecycle management product will help you get it all under control. We’ll discuss roadmap for the upcoming year.