Mobile Apps: Why Legacy WAM Can’t Protect them
In recent years, there’s been an explosion of mobile apps for consumers. With this paradigm shift away from on-premises apps, legacy Web Access Management (WAM) solutions are failing to support customer applications outside the traditional firewall perimeter.
Read on to learn exactly what WAM is, and why its architecture can’t protect mobile apps. We’ll also illustrate how best to protect mobile applications outside the perimeter.
What is Web Access Management?
In the early 2000s, WAM was created to pave the way for single sign-on convenience with authentication and authorization, and to provide access control to web resources. The WAM framework provided a way to protect web resources by erecting a firewall, which gave way to a single access point to the servers. Users would then receive authentication and authorization from the WAM agent, then move on to use the apps inside the intranet.
Here’s a real life analogy that is useful for understanding WAM architecture: Imagine you're throwing a party for all your applications on your intranet. You wouldn’t want an uninvited intruder to crash your party, access your apps, and ruin the fun, so you put up firewalls to keep the bad actors out.
But when you build a perimeter, you need a point of access to let the right people in, and a watchful gatekeeper, or "bouncer". The bouncer in this scenerio would be your Web Access Management system. WAM would provide authentication and authorization into the space where the apps reside.
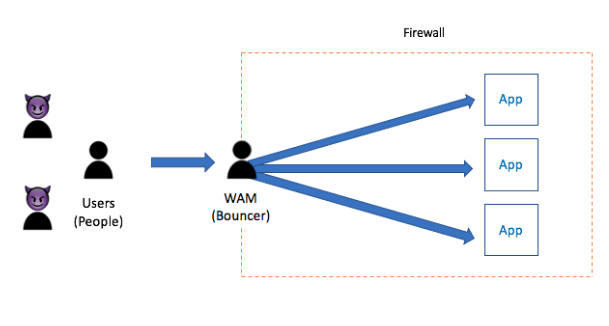
This architecture serves as a solution to vault over firewalls that typically surround enterprise resources (such as ERPs and CRM systems) and let the correct people in. However this architecture doesn't work for mobile apps.
The Challenge with Modern apps
So why is this structure not ideal for mobile apps? Because these apps live outside of the perimeter. Mobile apps live outside the intranet—it’s impossible to hire enough bouncers to control their access.
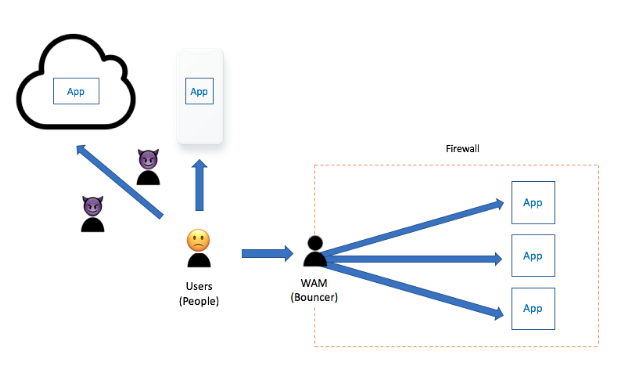
With the development of a distributed network of applications (e.g., mobile, cloud, AWS, Heroku, etc.), the costs associated with maintaining these legacy solutions rapidly rises. The architecture of legacy WAM depends on security perimeters, high-redundancy data centers for disaster recovery, and load balancers. Along with other issues, these maintenance costs have caused a shift away from these legacy infrastructures.
Protecting mobile aps with modern identity
This is where Okta comes in. Okta provides a modern identity solution that works for your mobile apps. In other words, we’ll be the identity system that makes sure the right people get into your "mobile app" party.
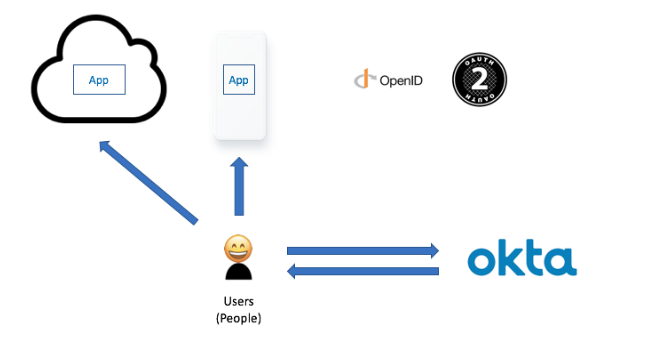
Using SDKs and modern standards like OAuth and OIDC, Okta provides your developers with the services and APIs to control access to your mobile apps, regardless of operating system, iOS, or Android.
So, that’s a simple explanation of why WAM is not a viable approach for mobile apps. But all is not lost if you are currently living in the world of WAM—Okta can help. To learn how we work with and transform legacy WAM solutions, read our whitepaper on Managing Access to Legacy Web Applications with Okta.

