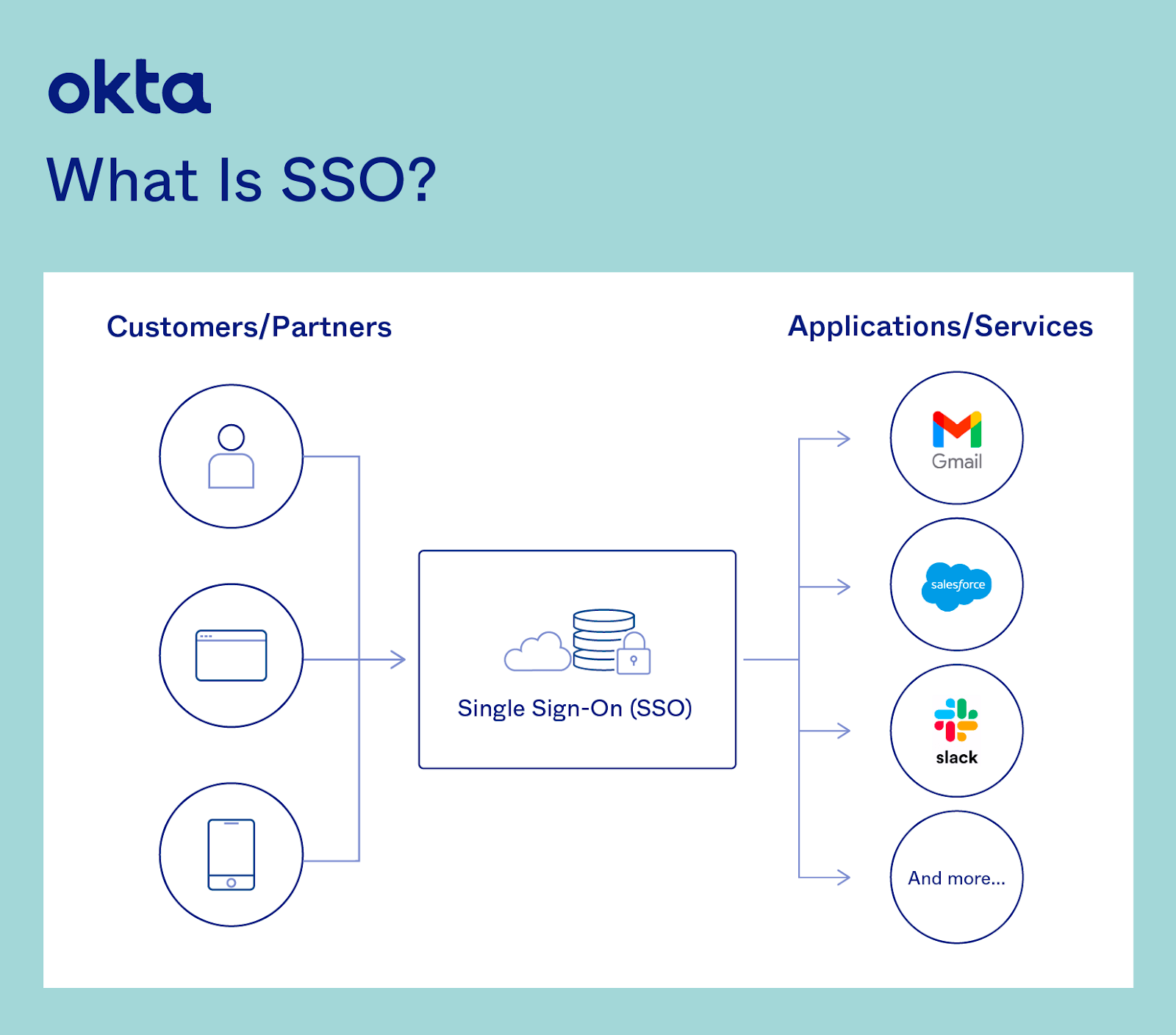
Single sign-on (SSO) is an authentication tool that enables users to securely access multiple applications and services using one set of credentials, eliminating the need to remember different passwords for each service.
In today’s remote work ecosystem, where employees rely on software-as-a-service (SaaS) applications like Slack, Google Workspace, and Zoom, SSO provides a simple pop-up widget or login page with just one password that provides access to every integrated app.
SSO puts an end to the days of remembering and entering multiple passwords and eliminates the frustration of having to reset forgotten passwords. Users can also access a range of platforms and apps without having to log in each time.
How does SSO work?
SSO is built on the concept of federated Identity, which is the sharing of Identity attributes across trusted but autonomous systems. When a user is trusted by one system, they are automatically granted access to all others that have established a trusted relationship with it. This provides the basis for modern SSO solutions, which are enabled through protocols like OpenID Connect and SAML 2.0.
How do SSO tokens work?
SSO works like digital keys that prove a user's Identity. When a user signs in to a service with their SSO login, an authentication token is created and stored either in their browser or in the SSO solution’s central authentication service (CAS) server. Any app or website the user subsequently accesses will check with the SSO service, which then sends the user’s token to confirm their identity and provide them access without having to log in again. This process ensures a seamless and secure experience across different platforms.
The history of SSO
SSO technology has its roots in the on-premises Identity tools that helped organizations securely connect their computers, networks, and servers together in the mid-to-late 1990s. Back then, organizations began to manage their user identities through dedicated systems like Microsoft’s Active Directory (AD) and Lightweight Directory Access Protocol (LDAP), then secured access through on-premises SSO or Web Access Management (WAM) tools.
As IT continues to evolve by moving to the cloud, dispersing across multiple devices, and facing more sophisticated cyberthreats, traditional Identity management tools have struggled to keep pace. IT teams need a solution that provides users with quick, secure SSO access to any application or service.
Types of SSO
There are a variety of protocols and standards to be aware of when identifying and working with SSO. These include:
- Security Access Markup Language (SAML): SAML is an open standard that encodes text into machine language, enabling the exchange of identification information. As a core standard for SSO, it helps application providers ensure their authentication requests are appropriate. SAML 2.0 is specifically optimized for web applications, allowing information to be transmitted through a web browser.
- Open Authorization (OAuth): OAuth is an open-standard authorization protocol that transfers identification information between apps and encrypts it into machine code. This empowers users to grant an application access to their data in another application without having to validate their identities manually.
- OpenID Connect (OIDC): OIDC sits on top of OAuth 2.0 to add information about the user and enables the SSO process. It allows one login session to be used across multiple applications. For example, OIDC enables a user to log in to a service using their Facebook or Google account rather than entering user credentials.
- Kerberos: Kerberos is a protocol that enables mutual authentication, whereby both the user and server verify the other’s identity on insecure network connections. It uses a ticket-granting service that issues tokens to authenticate users and software applications like email clients or wiki servers.
- Smart card authentication: Beyond traditional SSO, hardware can facilitate the same process, such as physical smart card devices that users plug into their computers. Software on the computer interacts with cryptographic keys on the smart card to authenticate each user. While smart cards are highly secure and require a PIN to be operated, they have to be physically carried by the user, running the risk of being lost. They can also be expensive to operate.
On-premises vs. cloud-based SSO
SSO solutions should align with an organization's overall IT strategy, security posture, and operational needs, including whether they are on-premise or cloud-based.
On-premises SSO requires installing and maintaining hardware and software within a physical location. It offers complete control over the SSO environment for organizations with specific compliance or security requirements. However, it involves higher upfront costs for hardware and software purchases and requires significant resources for ongoing maintenance and scaling.
Cloud-based SSO is hosted on a provider's infrastructure and is a more flexible and cost-effective approach. It reduces the need for physical hardware, lowers initial costs, and provides scalability to adjust service usage based on demand. While this model offers less control over the infrastructure, it leverages the cloud provider's security and compliance measures, which can be an advantage for organizations looking for robust security with minimal overhead.
The benefits of SSO
Organizations that deploy SSO reap a wide range of benefits, from avoiding the risks presented by password recycling to delivering a seamless user experience. Key benefits of SSO include:
- Decreased attack surface: SSO eliminates password fatigue and poor password practices, immediately making your business less vulnerable to phishing. It enables users to focus on memorizing one strong, unique password and reduces time-consuming and costly password resets.
- Seamless and secure user access: SSO provides real-time insight into which users accessed applications when and where from, allowing enterprises to protect the integrity of their systems. SSO solutions also address security risks such as an employee losing their corporate device, enabling IT teams to immediately disable the device’s access to accounts and critical data.
- Simplified user access auditing: Ensuring the right people have the right level of access to sensitive data and resources can be tricky in an ever-changing business environment. SSO solutions can be used to configure a user’s access rights based on their role, department, and level of seniority. This ensures transparency and visibility into access levels at all times.
- Empowered and productive users: Users increasingly demand quick and seamless access to the applications they need to get their jobs done. Managing requests manually is a painstaking process that only serves to frustrate users. SSO authentication eliminates the need for manual oversight, enabling immediate access to up to thousands of apps with a single click.
- Future-proofing: SSO is the first step in securing your company and its users. Additionally, SSO allows organizations to implement other security best practices, including deploying multi-factor authentication (MFA) and hooking into Identity proofing, risk ratings, and consent management tools to address compliance needs and mitigate fraud.
The challenges of SSO
While SSO is user-friendly and convenient, it can pose a security risk if it’s not well-managed or properly deployed. Obstacles include:
User access risks: If an attacker gains access to a user’s SSO credentials, they also gain access to every app the user has the rights to. So, it’s imperative to deploy additional authentication mechanisms beyond just passwords.
Potential vulnerabilities: Vulnerabilities have been discovered within SAML and OAuth that gave attackers unauthorized access to victims’ web and mobile accounts. It’s important to work with a provider that has accounted for these instances in their product and pairs SSO with additional authentication factors and Identity governance.
App compatibility: At times, an app isn’t set up to effectively integrate with an SSO solution. Application providers should have real SSO capability, whether via SAML, Kerberos, or OAuth. Otherwise, the SSO solution is just another password for users to remember and doesn’t provide comprehensive coverage.
Is SSO secure?
An SSO solution from a proven provider delivers verified security protocols and service at scale. Here's how SSO best practices boost security:
- IT teams are able to leverage SSO to protect users with consistent security policies that adapt to their behavior while simplifying the management of usernames and passwords.
- Built-in security tools automatically identify and block malicious login attempts, making business networks safer.
- Organizations can deploy security tools like MFA in tandem with SSO and quickly oversee user access rights and privileges.
What are some SSO security risks and advantages?
The security of SSO systems depends on a number of variables, including the implementation, the technologies used, and the security practices followed by the organization implementing them.
Potential security risks:
- Single point of failure: If an SSO system is compromised, all connected systems and applications are at risk for attack.
- Dependency on third-party services: If SSO relies on third-party services, there's an inherent risk in trusting another entity with the security and availability of the authentication process.
- Implementation flaws: When SSO is Improperly implemented it can introduce vulnerabilities. This includes misconfiguration, inadequate session management, and insufficient encryption practices.
- Cross-domain authentication challenges: SSO systems that authenticate users across different domains must securely manage tokens and credentials across potentially insecure networks.
Advantages for security:
- Reduced password fatigue: By reducing the number of passwords users need to remember, SSO can decrease the likelihood of weak password creation and reuse.
- Centralized control: SSO allows for centralized management of user access and authentication, making it easier to enforce strong security policies, like MFA, and to respond quickly to security incidents.
- Improved user compliance and satisfaction: When the process is simplified, users are more likely to follow security policies and procedures. SSO eliminates the need to remember and enter multiple passwords.
- Enhanced logging and monitoring: Centralizing authentication services allows for more effective logging and monitoring of access patterns and security incidents. .
How is SSO implemented?
Regardless of the specific technology or protocol used, the implementation of SSO generally involves the following steps:
- Identity provider integration: The Identity provider is set up and configured to store and manage the user identities and credentials.
- Service provider registration: Each application or service that will use SSO is registered with the Identity provider, establishing trust between both.
- Authentication flow setup: The specific authentication flow (e.g., SAML, OIDC) is implemented, directing authentication requests from the service provider to the Identity provider and handling the exchange of authentication assertions or tokens.
- User experience configuration: The login experience is configured to redirect users to the Identity provider for authentication when they attempt to access any of the integrated services or applications.
- Security and compliance: Security measures, such as encryption and signing of authentication assertions, protect the integrity and confidentiality of the authentication process and compliance with applicable regulations and standards.
SSO’s role in Identity and Access Management (IAM)
IAM helps organizations manage all aspects of user access, and SSO is one part of that broader Identity landscape. SSO is essential to verifying user identities and providing the right permission levels, and should be integrated with activity logs, tools that enable access control, and processes that monitor user behavior.
How SSO compares to other access management solutions
SSO vs. MFA
SSO and MFA serve complementary roles in managing access to digital services. SSO simplifies user access by allowing one set of credentials to unlock multiple applications, enhancing convenience and efficiency. In contrast, MFA strengthens security by requiring users to provide multiple verification factors before granting access, significantly reducing the risk of unauthorized entry. While SSO aims to streamline the user experience by reducing login redundancies, MFA adds an essential layer of security, making it more difficult for attackers to compromise sensitive information. Many organizations leverage both technologies together, using SSO for ease of access across multiple services and MFA to ensure access remains secure, balancing user convenience with strong security measures.
SSO vs. federated Identity
SSO and federated Identity management (FIM) streamline user access to multiple systems but are related to different aspects of access management. SSO simplifies the login process within a single organizational domain, allowing users to access various applications using one set of credentials. Federated Identity extends these benefits across organizational boundaries, allowing secure and frictionless access to resources across multiple domains without the need for separate credentials for each. This is achieved through establishing trust relationships and using standards like SAML and OAuth for collaboration across companies or services. While SSO focuses on internal ease of access, federated Identity emphasizes interoperability and secure data sharing between different entities.
Identity-as-a-Service (IDaaS) solutions deliver all aspects of IAM, including SSO, adaptive MFA, and user directories in a single package. This simplifies security, provisioning, and workflows, enhances user experience, and saves organizations time and money.
What to look for in an SSO provider
Selecting an SSO provider means navigating a wide range of vendor options. Key provider capabilities include:
Access to any application: The best SSO providers will support integrations with all key apps on the market. When assessing providers, focus on the range of applications and sophistication of integrations they offer. Look for solutions that enable network resource integration across enterprise, SaaS, and web applications.
SSO customization: A modern SSO product must meet the specific needs of each user by providing a dashboard that shows only the apps they have permission to access. Dashboards should be customizable to meet the company's branding needs and ensure brand consistency and continuity across all of its branded sites.
MFA integration: It’s important not to rely solely on usernames and passwords, so look for an SSO provider that integrates with any MFA solution and can capture a wide range of user contextual factors such as location, risk profile, and behavior. This strengthens security by requiring users to provide additional information that confirms their identity.
Monitoring and troubleshooting: An effective SSO provider supplies monitoring tools that help organizations quickly identify and resolve performance issues across their entire IT hybrid or cloud-based environment.
Ready to implement SSO in your organization?
Discover how Okta Single Sign-On provides seamless integration to more than 6,000 popular apps, or check out our end-user experience to get started with SSO.






