Customer Identity Solution
Authentication
Unlock possibilities with User Authentication
Secure and seamless customer experiences that start right at login.
ROI with real results
50M
daily authentications on the Okta Identity Cloud
10+
SDK’s in the languages you work in
99.99%
uptime for every customer
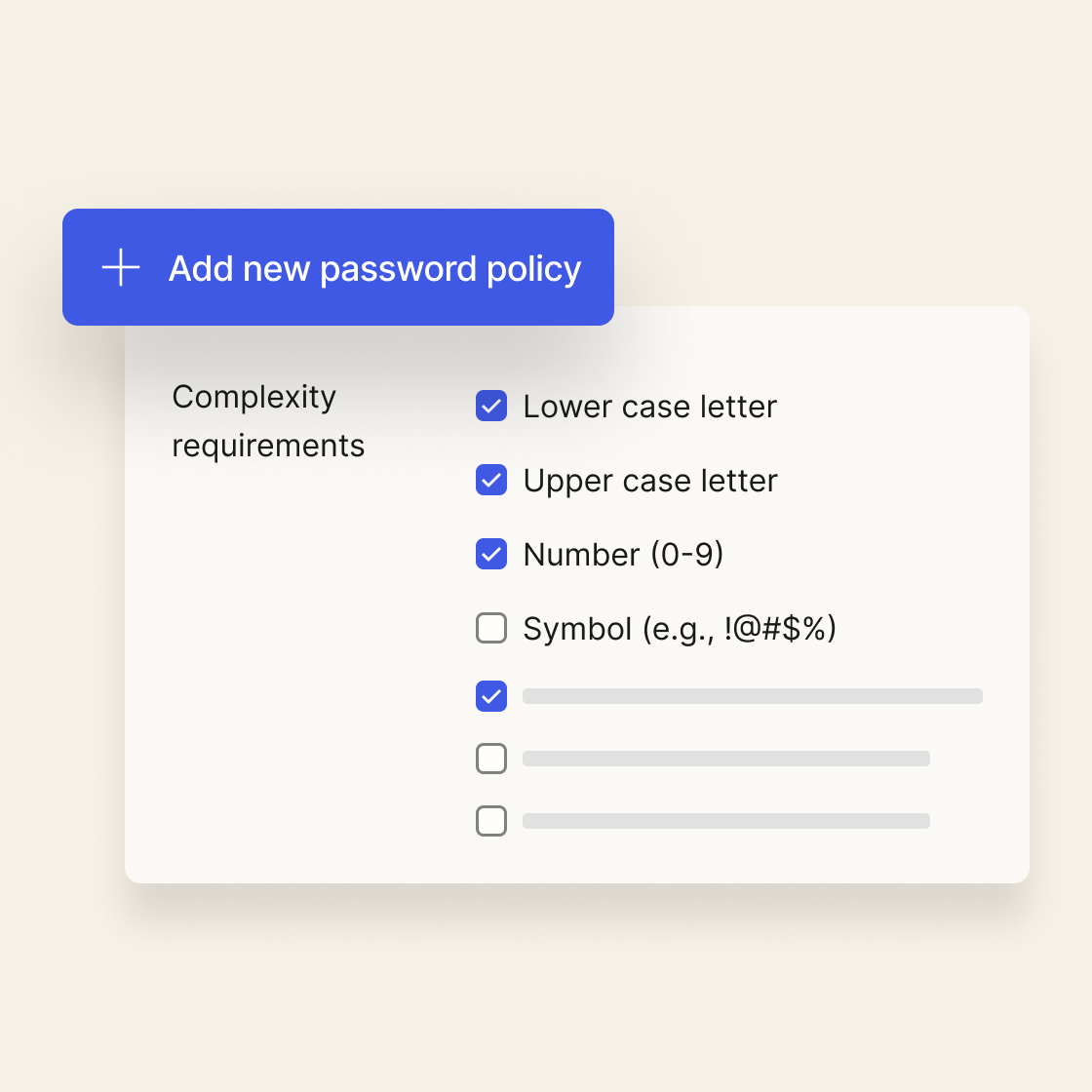
Protect your customer data
Set strong customer authentication policies and reduce account takeover attacks. Easily add a second security factor and enforce strong passwords to protect your users.
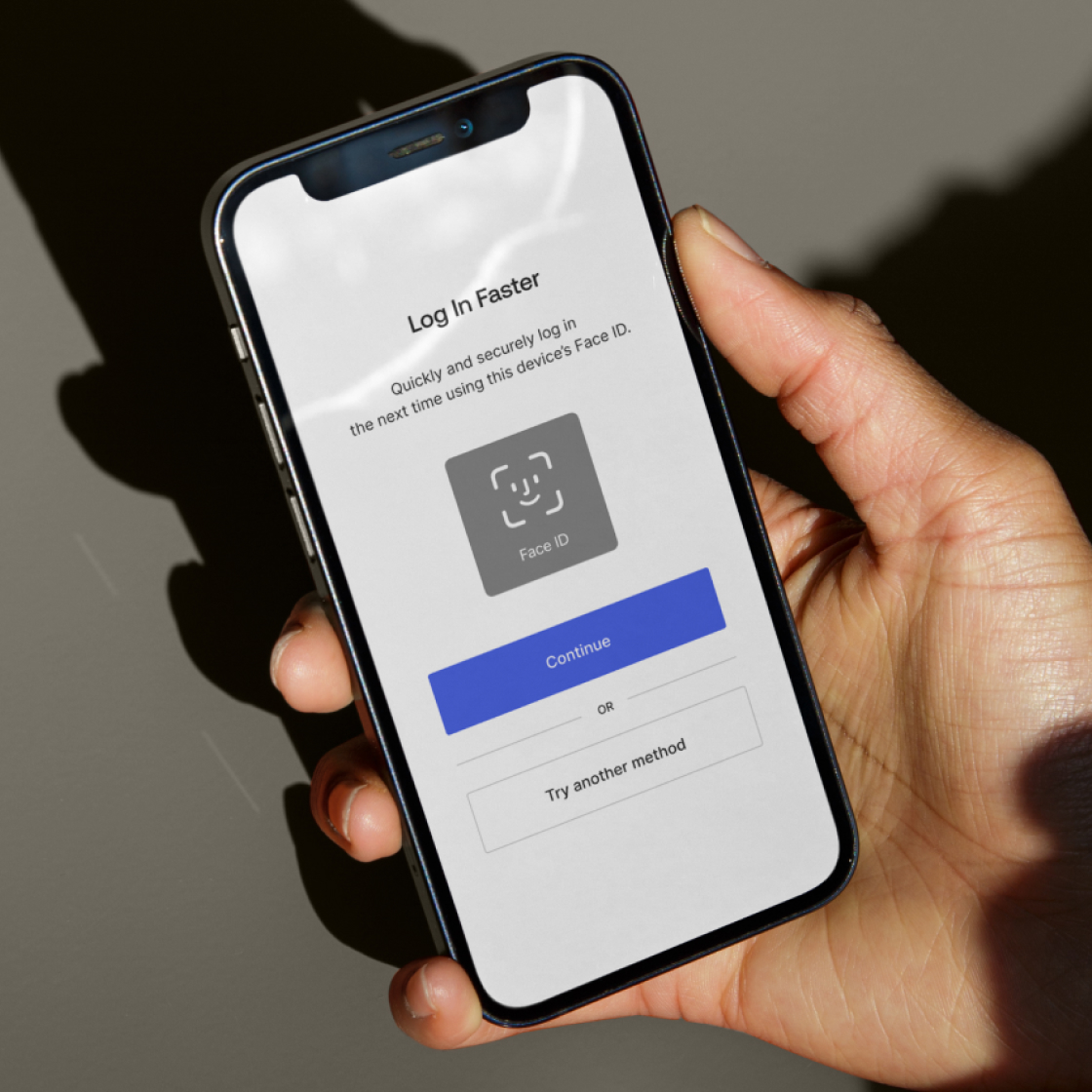
Balance security and user experience
Don’t let your security features get in the way of a positive user experience. Provide customers with passwordless authentication while protecting their data.
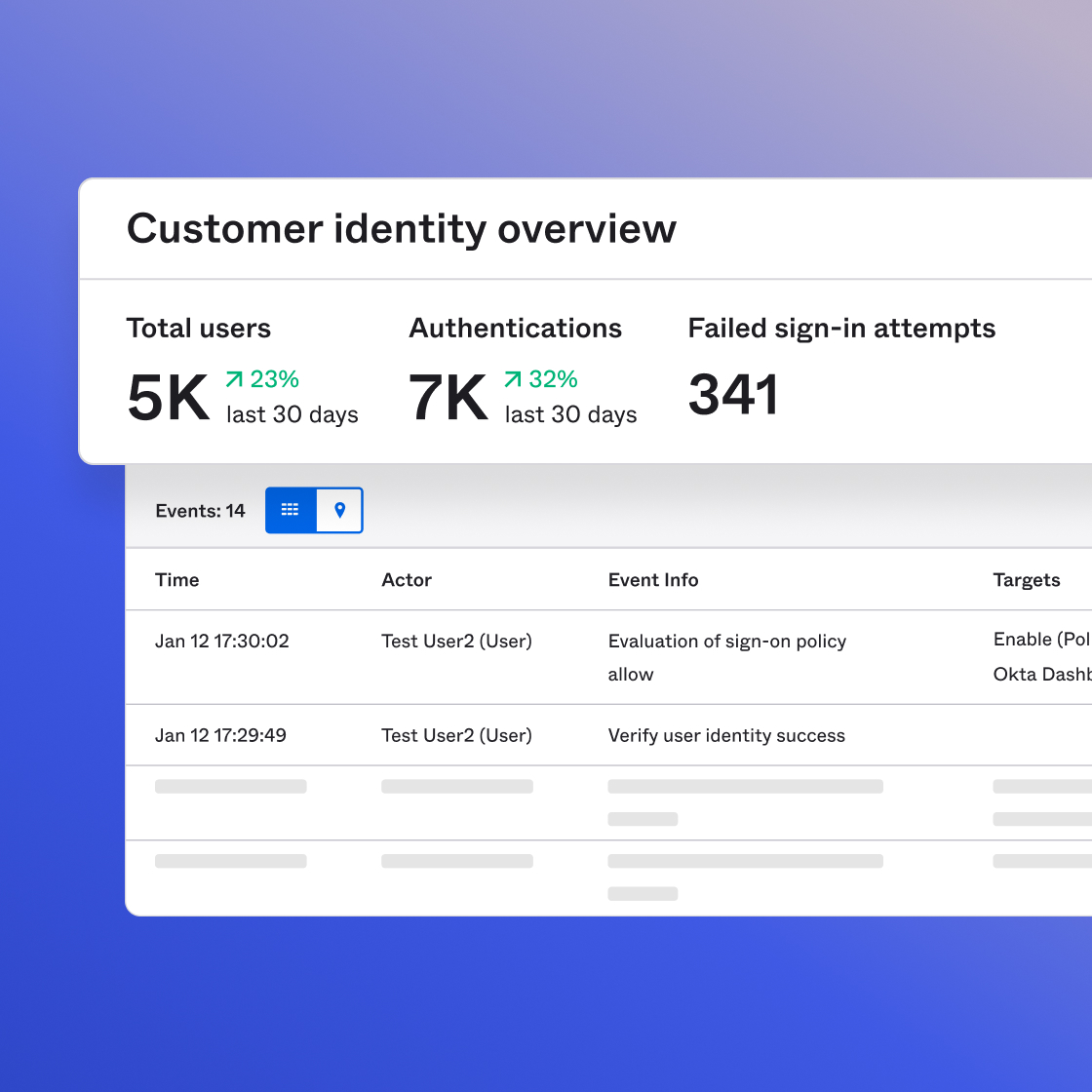
Detect and respond to security risks sooner
Augment your security team and proactively protect your end users from the latest threats.
Learn more about Okta Integration Network

Meet compliance mandates quickly and easily
Stay focused on your company’s core mission while keeping operational costs low and minimizing complexity while meeting compliance requirements.
“Within the past 10 years, rock-solid identity has become key to security and to the user experience. Identity is the crux—the baseline of our trusted digital services.”
Bob Durfee
Head of Digital Engagement and DevSecOps, Takeda
"Now, each customer has a single Identity. We give them tailored customer experiences, but that doesn't mean they need three different user IDs and passwords.."
Ramiya Iyer
GVP, IT Digital, Data and Pharmacy, Albertsons at Albertsons Companies
"[Okta] is one of the things that I can put in my toolkit to say, ‘Hey, we're gonna move faster because we have this Identity component nailed.'"
Scott Howitt
CISO, MGM Resorts International

WHY OKTA
Okta is a world-leading Identity provider
Our solutions are comprehensive, secure, easy-to-use, reliable, and work with your existing technology. So no matter your stack, we’ve got your back. Over 18,000 customers rely on our 7,000+ pre-built integrations, extensibility, and flexibility.
Let’s get you going
Start a free trial or talk with us — the next step is all yours.