FACT OR FICTION: I Need Separate SSO Solutions to Access Apps On-Prem and in the Cloud
At Okta, we are highly invested in the latest ideas and practices around authentication and security—and that requires some myth busting. This blog is the latest in a series of posts meant to tackle common misunderstandings and myths around single sign-on (SSO). See below for our full list of the myths we've seen (and busted!) around SSO.
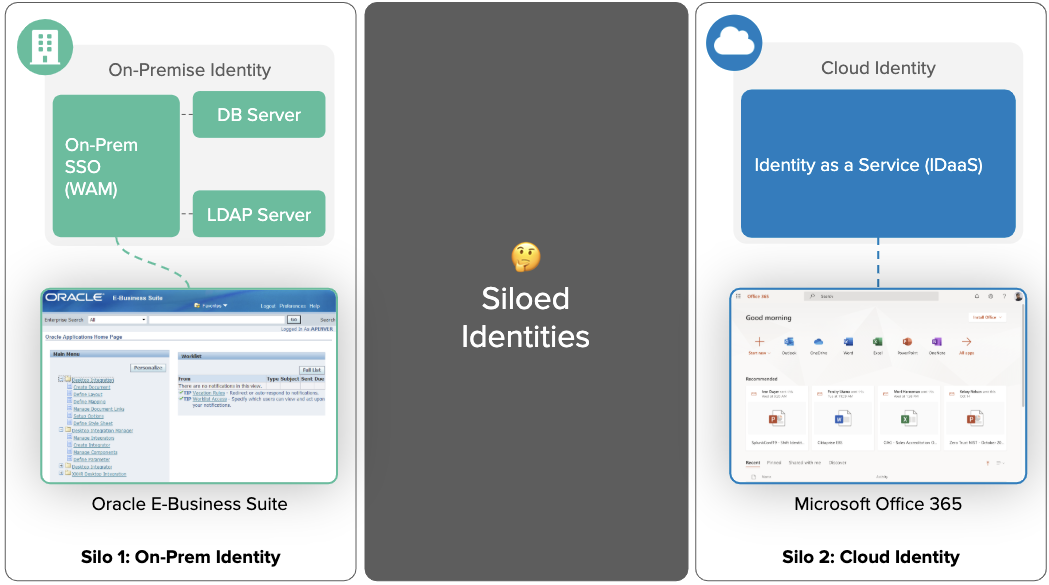
In larger organizations, IT and Security teams often think they need two SSO solutions: one to control access to on-premises apps—Web Access Management (WAM)—and a second one to control access to the cloud—Identity as a Service. However, this is not true. Using a single SSO solution for both on-premises and cloud system, aka Hybrid IT, saves time and money.
Providing users secure and consistent access to all systems is not a new thing, it’s been a challenge since the mid 90s/2000s. To address this challenge in the past, many companies adopted on-premises SSO or WAM solutions. Examples of this are CA SiteMinder, PingAccess, and PingFederate.
With the explosion of the cloud, organizations started adopting cloud SSO—also known as Identity as a Service (IDaaS)—to control access to the new systems. With this, organizations started having two identity providers: one for on-premises and one for the cloud.
Two separate systems were needed because:
- On-premises SSO lacked key features required to support cloud applications, such as native integrations to popular cloud apps like Office 365, AWS, and Salesforce. It also lacked modern security features required in public networks like passwordless access and the ability to easily scale to support cloud traffic.
- Cloud SSO didn't support access to popular on-premises applications, like Oracle E-Business Suite and PeopleSoft. It also lacked support for integration patterns like Header-based authentication, Kerberos, and IWA.
So what’s changed?
This was true until two key trends changed the landscape:
- More SSO on-premises solutions are being deprecated.
- Cloud solutions are now supporting on-prem applications.
Let's break down these trends
SSO on-premises is being deprecated
SSO on-premises is expensive to run, maintain, and support, costing significant time and resources just to keep the lights on. It’s also hard to secure because upgrading systems is a time-consuming uphill battle, leaving you at risk to security vulnerabilities. There are limited, and often insecure, ways to apply MFA to the authentication flow, which doesn’t leave much room to balance security with usability.
With these issues in mind, many traditional on-premises SSO vendors are deprecating or retiring their solutions and encouraging customers to adopt a cloud SSO solution instead.
Many analysts see this trend as well. For example, Gartner predicts that "By 2022, IDaaS will be the chosen delivery model for 80% of access management deployments"*
As a result, many organizations coming up on their on-prem SSO contract renewal are reevaluating their options for securing access to on-premises systems.
Cloud SSO solutions now support on-premises web applications
Cloud SSO solutions traditionally only supported the SSO federation standards used in the cloud, e.g., SAML, OpenID Connect, and OAuth.
Cloud SSO is attractive because it allows organizations to pay as you go/grow and use pre-built app integrations, high-availability beyond on-prem solutions, and regular updates without service outages. Organizations found so much value in Cloud SSO that they started to ask their cloud providers to expand access beyond just cloud, but also to custom apps, servers, and other on-prem applications.
At Okta, we started addressing these asks several years ago:
- For custom apps, we started offering Okta as APIs and SDKs, so developers can quickly secure their apps the same way they use Twillio APIs for communications or Stripe APIs for payments.
- For servers, we launched Advanced Server Access, a solution that controls access to servers, regardless of where and how they are hosted.
- For on-premises access, we launched Access Gateway, a solution that provides SSO and MFA to on-prem web applications, replacing the need for separate on-prem and cloud SSO solutions.
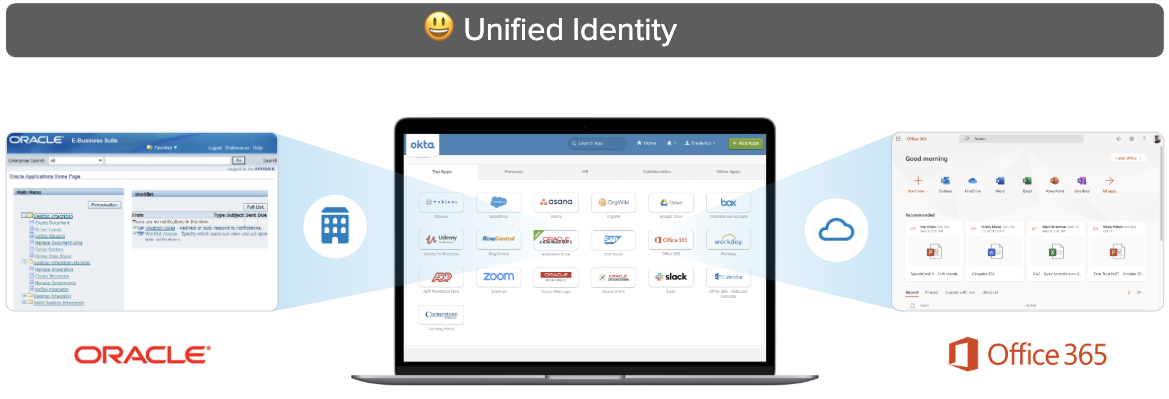
With these solutions, you can consolidate access for all users (employees, contractors, and customers), and all resources (servers, on-prem, and cloud-based apps) into a single platform: the Okta Identity Cloud. All while saving costs and improving ease of use.
What does a single Identity platform look like in practice?
With a single identity platform for everything, you will see differences in both the admin and the end-user experience.
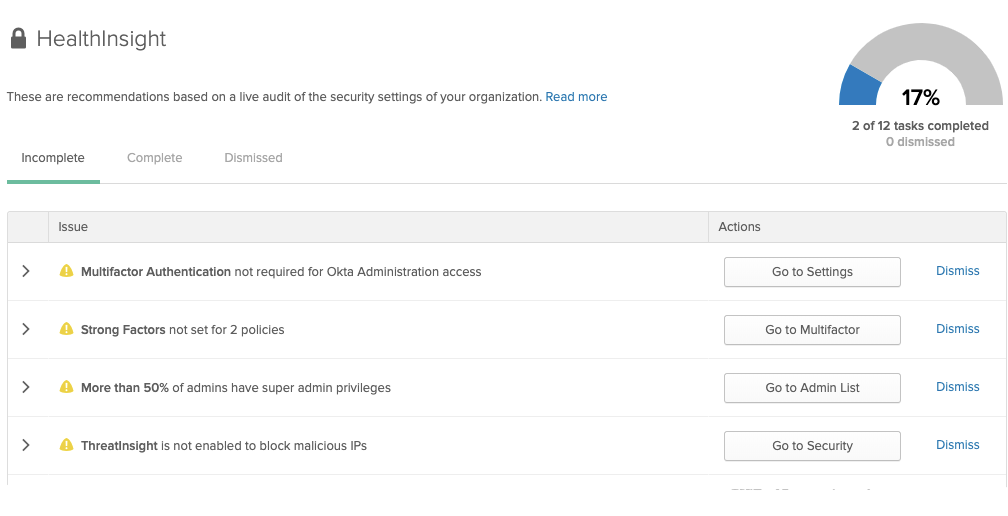
For IT and Security Administrators, they get to control access to both cloud and on-premises solutions from a single interface. This significantly cuts the time spent writing and auditing security policies, users, groups, and MFA policies because can be done from a single place—instead of multiple admin consoles.
Unified Security Policy for on-premises and cloud apps
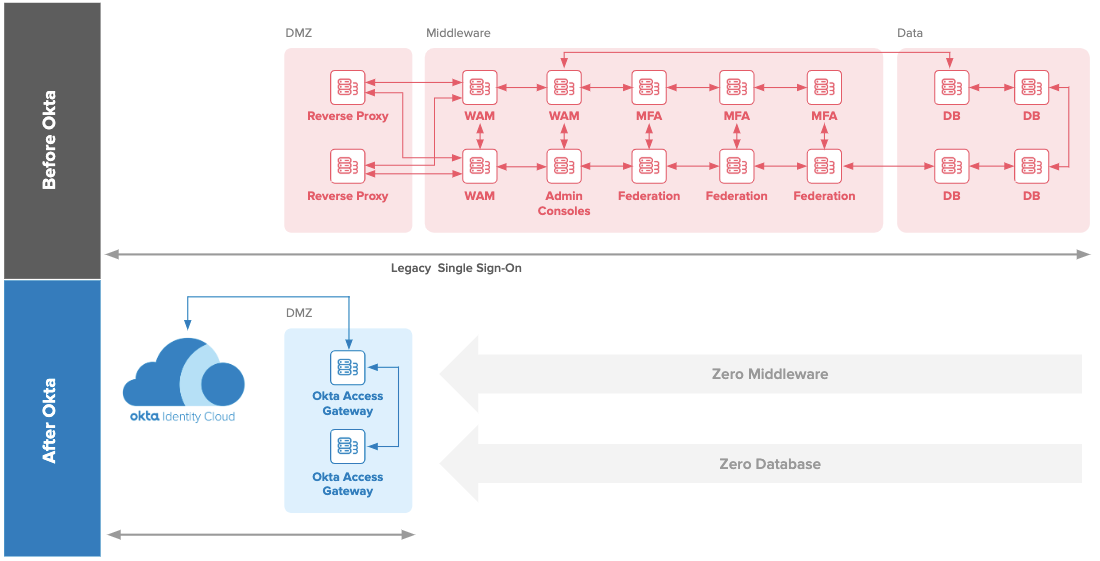
Furthermore, administrators spend less time maintaining and patching servers since this solution reduces the number of servers required in traditional SSO on-premises by up to 90%.
Collapsed SSO Infrastructure: no middleware and database required
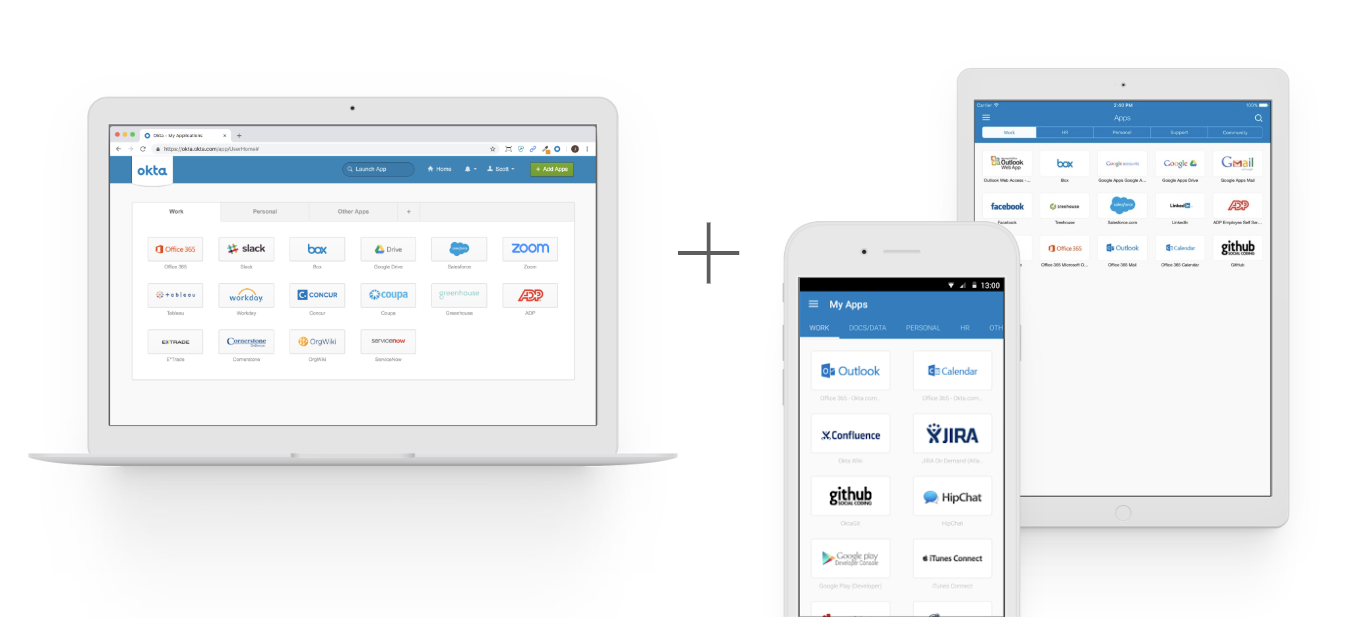
End-Users get consistent access to what they need. It starts from the dashboard, where they can see and access both cloud or on-prem web apps,from Microsoft Office 365 to Oracle E Business Suite, without having to jump through different interfaces, as shown below.
Single dashboard with access to on-premises and cloud resources
Also, end-users can benefit from modern cloud SSO security—such as passwordless access with touch ID—to access on-premises web apps.
In Action: passwordless access to on-premises web portal
And finally, users can access their apps from multiple devices and from any location, avoiding complex network tools like VPNs.
Unified access for desktop and mobile devices
Yes! Use one SSO for all systems, whether on-prem or in the cloud!
As you can see, the multiple SSO solutions myth is debunked! You can use a single SSO solution for cloud apps, custom apps, servers, and on-premises web apps. In fact, this is the recommended path to improve the user and admin experience, reduce costs, and avoid deprecated solutions.
Want to learn more about SSO? Listen to the Things You Don’t Know About Single Sign-On webinar, visit our SSO page, and check out our entire myth busting series:
- Fact or Fiction: SSO is Difficult to Deploy
- Fact or Fiction: SSO Slows Down IT
- Fact or Fiction: SSO Creates a Single Point of Failure, so It’s Less Secure
- Fact or Fiction: SSO Is the Same as a Password Manager
Want to learn about how Okta expanded to support new use-cases?
- For customer identity, check this video and page
- For controlling access to servers, check this video and page
- For controlling access to on-prem apps, check this video and page
*Gartner's Magic Quadrant for Access Management, Worldwide 2018